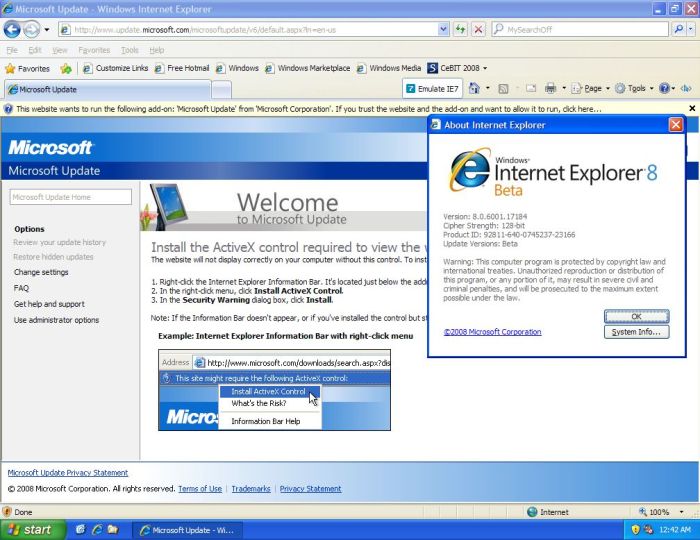
New Worm Masquerades as IE7 Beta Download
New worm masquerades as IE7 beta download, a sneaky threat disguised as a legitimate update, is on the rise. This malicious program leverages the familiarity of the IE7 beta download to trick unsuspecting users into installing harmful software. We’ll explore how this worm operates, the channels it uses to spread, and, crucially, the steps you can take to protect yourself.
This worm’s ability to mimic a familiar file type underscores the importance of always verifying download sources. We’ll delve into infection vectors, including deceptive websites, email attachments, and even peer-to-peer networks. A table will illustrate the risks associated with different download sources and the best mitigation strategies. Furthermore, we’ll uncover the technical characteristics of the worm, analyze its propagation methods, and examine how to identify its presence on your system.
Threat Identification
A “new worm masquerading as an IE7 beta download” poses a significant threat to computer systems. This type of malicious software leverages the public’s trust in legitimate software updates and downloads to infiltrate and compromise systems. Understanding the tactics, methods, and potential impact of this threat is crucial for proactive security measures.
Malicious Nature of the Worm
This worm, disguised as a legitimate IE7 beta download, is designed to exploit vulnerabilities in vulnerable systems. It often contains malicious code that can replicate itself, spreading across networks and infecting other systems. This self-replication capability makes it a significant threat to both individual users and larger organizations. The worm’s actions are often designed to steal data, disrupt operations, or create further vulnerabilities in the targeted systems.
Common Tactics for Disguising Malware
Malware authors frequently employ sophisticated tactics to disguise their malicious software. A common tactic involves mimicking legitimate software updates, such as the IE7 beta download. This deception leverages the user’s expectation of receiving a legitimate update, making the user more susceptible to unknowingly installing malicious software. Other tactics include using similar filenames and packaging to legitimate software, and exploiting vulnerabilities in the user’s operating system or applications.
Phishing emails and fake websites are also common ways to distribute malware disguised as legitimate software downloads.
Potential Methods of Spread
The worm can spread through various channels. Downloads from compromised websites, malicious advertisements, and infected email attachments are common vectors. Social engineering, where users are tricked into downloading the infected file, plays a significant role. A deceptive IE7 beta download could be easily distributed via compromised websites or forums, appearing as a legitimate software update to unsuspecting users.
Types of Harm Caused by the Threat
The harm caused by this type of worm can range from minor inconveniences to severe data breaches. Infected systems can experience performance degradation due to the worm’s replication and resource consumption. Data theft, including sensitive personal information, financial records, and intellectual property, is a significant concern. Furthermore, the worm can create backdoors into systems, enabling attackers to control the compromised machines remotely, and potentially deploy other malware.
System instability, and even complete system crashes, are possible outcomes.
Impact on Computer Systems and Networks
The impact on individual systems and networks can be significant. A widespread infection can lead to network congestion and slowdowns, impacting productivity and accessibility. Individual computers can be rendered unusable due to the worm’s actions, and crucial data could be lost or stolen. The impact on critical infrastructure, such as hospitals, financial institutions, or government agencies, could be devastating.
The worm could disrupt essential services and cause widespread economic and social damage.
Likelihood of Widespread Infection
The likelihood of this threat becoming widespread depends on several factors. The effectiveness of security measures in place to detect and block malicious downloads plays a significant role. The worm’s sophistication, along with the extent of its spread, will also influence its prevalence. The susceptibility of users to phishing attempts and the ease of obtaining the malicious download are also key elements to consider.
That new worm disguised as an IE7 beta download is seriously concerning. Thankfully, there are proactive steps you can take to protect yourself, like utilizing tools like imlogic releases free im and p2p blocking software to block instant messaging and peer-to-peer traffic. This can help limit the worm’s potential spread and impact. It’s crucial to remain vigilant against these threats in the ever-evolving digital landscape.
Past malware outbreaks provide evidence of how rapidly a threat can spread, given the right conditions. The effectiveness of security awareness campaigns and the timely release of security patches will influence the likelihood of a widespread infection.
Infection Vectors: New Worm Masquerades As Ie7 Beta Download
Malware disguised as legitimate downloads often exploits user trust and inexperience. Sophisticated social engineering tactics are employed to trick victims into installing malicious software. Understanding these vectors is crucial for recognizing and avoiding these threats.
Typical Distribution Channels
Malicious actors frequently utilize seemingly legitimate download sources to distribute malware. These channels exploit the ease of access and trust users place in common online platforms. This tactic is particularly effective because users often lack the time or expertise to thoroughly investigate each download.
Social Engineering Tactics
Social engineering plays a significant role in the spread of malware disguised as legitimate downloads. Attackers leverage psychological manipulation and deception to trick victims into taking specific actions. This often involves creating a sense of urgency or exploiting existing anxieties.
Deceptive Websites and Email Tactics
Deceptive websites and emails are common tools used in social engineering. These often mimic legitimate websites or organizations to trick users into revealing sensitive information or downloading malicious files.
- Fake Download Pages: These websites closely mimic legitimate download pages for popular software, tricking users into downloading malicious software instead of the genuine version. These sites often use identical logos and layouts, making them appear trustworthy.
- Phishing Emails: Malicious actors send emails that appear to be from trusted organizations (e.g., banks, software companies) requesting users to download a file or click a link. These emails may contain urgent requests or warnings, aiming to create a sense of panic and encourage immediate action.
- Spoofed Links: Malicious actors create fake URLs that closely resemble legitimate websites. Users clicking these links are redirected to malicious websites, which then attempt to download malware.
Download Source Risks
The risk associated with different download sources varies significantly. Understanding these risks is essential for making informed decisions about where to download software and files.
| Download Source | Risk Level | Description | Mitigation Strategies |
|---|---|---|---|
| Unofficial websites | High | Websites that mimic legitimate sites to trick users, often lacking security measures. | Verify website legitimacy, avoid suspicious links, use official websites whenever possible. |
| Email attachments | Medium | Malicious attachments disguised as legitimate files (e.g., invoices, documents), exploiting user’s trust in the sender. | Avoid opening attachments from unknown senders, scan attachments with reputable antivirus software before opening. |
| Peer-to-peer networks | Low | Files shared through peer-to-peer networks that might contain malware, although often relying on users’ trust in the file sharer. | Use trusted sources, scan downloaded files with reputable antivirus software. |
User Tricking Mechanisms
Attackers employ various techniques to trick users into installing malware. These include exploiting users’ trust, creating a sense of urgency, or exploiting existing vulnerabilities in software or operating systems.
- Creating a Sense of Urgency: Attackers might create a false sense of urgency, prompting users to act quickly without properly verifying the legitimacy of the download or link.
- Exploiting Trust: Attackers often exploit the trust users place in legitimate organizations or individuals. They might use logos, colors, or language similar to legitimate sources to make the threat appear authentic.
- Leveraging User Inexperience: Attackers target users who lack the knowledge or experience to identify malicious downloads or websites. This is why education and awareness campaigns are critical in combating these threats.
Technical Analysis
This section delves into the technical intricacies of the IE7-disguised worm, focusing on its infection characteristics, resource impact, propagation mechanisms, and identification methods. Understanding these aspects is crucial for effective defense strategies.The worm’s infection process typically involves exploiting system vulnerabilities. Once a user interacts with a compromised file or website, malicious code executes, initiating the infection. This often results in the worm replicating itself across the system and network, potentially causing significant disruption.
Worm Infection Characteristics
Worm infections manifest in several key ways. These include unauthorized access to system resources, file corruption, and the creation of numerous processes, which can dramatically impact system performance. The worm’s behavior is often characterized by an aggressive replication rate, aiming to spread quickly and broadly across a network. This replication can lead to a significant drain on system resources, including CPU time, memory, and network bandwidth.
Potential Impact on System Resources and Performance, New worm masquerades as ie7 beta download
The impact of a worm infection on system resources and performance is significant. Increased CPU usage, reduced memory availability, and heightened network traffic are common consequences. In severe cases, these issues can lead to system instability, application failures, and network congestion. A notable example is the MyDoom worm, which caused widespread network disruptions due to its high replication rate and network scanning.
This demonstrates how a worm’s resource consumption can quickly overwhelm systems.
That new worm masquerading as an IE7 beta download is definitely a sneaky tactic. While it’s unsettling to see malware exploit vulnerabilities like this, it’s interesting to consider how advancements in neurotech, like neurotech links brain waves with computers , might lead to entirely new security threats in the future. The potential for malicious actors to manipulate brainwaves to control devices is quite a scary prospect, making the current worm problem seem almost quaint in comparison.
Worm Propagation Mechanisms
Worms employ various techniques to propagate across networks and systems. These methods exploit vulnerabilities in software, scan networks for vulnerable hosts, or leverage social engineering tactics. The choice of method often depends on the worm’s design and the target environment.
Comparison of Worm Propagation Techniques
| Propagation Technique | Description | Impact | Mitigation |
|---|---|---|---|
| Exploiting vulnerabilities | Leveraging known security holes in software. | High infection rate. | Patch software regularly. |
| Network scanning | Searching for vulnerable systems on a network. | Widespread infection. | Implement network security measures. |
| Social engineering | Tricking users into installing malware. | High impact on human error. | User awareness training. |
This table summarizes the different propagation techniques and their respective impacts. Effective mitigation strategies are essential to counter these techniques.
Identifying the IE7-Disguised Worm
Identifying the IE7-disguised worm necessitates a multi-faceted approach. Firstly, careful examination of the downloaded file is essential. Look for unusual file sizes, suspicious file extensions, and any discrepancies from legitimate IE7 update files. Secondly, analyze the process list and network traffic to identify unusual activity. Thirdly, monitoring system logs for error messages or suspicious events can be beneficial.
By employing these methods, the worm’s characteristics can be identified.
Mitigation Strategies
This worm masquerading as an IE7 beta download poses a significant threat, demanding proactive measures to prevent infection. Failing to implement robust mitigation strategies can lead to significant data loss, system downtime, and reputational damage. This section Artikels crucial steps to safeguard systems and users from this malicious code.
Preventive Measures
Implementing a multi-layered approach is essential to minimize the risk of infection. This involves a combination of software updates, strong passwords, regular security scans, and established response protocols. By combining these measures, users and organizations can significantly reduce their vulnerability to such threats.
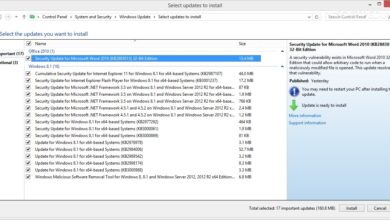
- Software Updates: Regularly updating operating systems, applications, and security software is paramount. Outdated software often contains vulnerabilities that attackers exploit. This is a critical step as attackers often target known weaknesses. Security patches frequently address newly discovered vulnerabilities, thus significantly reducing the risk of infection.
- Strong Passwords: Employing complex and unique passwords for all accounts is crucial. Use a combination of uppercase and lowercase letters, numbers, and symbols. Avoid using easily guessable information like birthdays or names. Consider a password manager to store and manage strong passwords securely. Weak passwords are a primary entry point for malicious actors, who can use various techniques to gain unauthorized access.
That new worm masquerading as an IE7 beta download is definitely a sneaky one. It’s interesting to consider how these kinds of exploits, and the constant need for security updates, are directly connected to the broader history of tech development. Think about how the design philosophies behind baby apples how the apple legacy shapes new products , for instance, have influenced the way we approach security in new products.
Ultimately, though, it all boils down to this: stay vigilant and avoid clicking on suspicious links!
- Regular Malware Scanning: Scheduled malware scans are essential to detect and remove malicious software before it can cause significant damage. Employ reputable antivirus software and run regular scans to identify and neutralize threats. By proactively scanning systems, organizations can promptly address potential issues and mitigate the risk of infection.
Responding to a Potential Infection
A well-defined response protocol is critical in containing the spread of an infection. A structured approach helps to limit the damage and ensure a swift recovery. This includes immediate isolation of infected systems and notification of relevant personnel.
- Isolate Infected System: Immediately disconnect the infected system from the network to prevent the spread of the infection. This includes disconnecting any external storage devices connected to the affected system.
- Contain the Infection: Identify and isolate any other systems or devices that might have been compromised. Restrict access to potentially affected systems to prevent further damage.
- Notify Relevant Personnel: Alert IT support, security personnel, or other relevant personnel about the potential infection. A rapid response is critical to minimize the impact of the threat.
- Scan for Malware: Employ reputable antivirus software to scan the infected system for malware. This helps to identify the specific malware and determine the extent of the damage.
- Quarantine Infected Files: Identify and quarantine any infected files to prevent further spread of the malicious code. This might involve creating a separate folder to isolate potentially infected files.
- Remediate the Infection: Follow the instructions provided by the security software to remove the malware. If the infection is particularly complex or if you lack the expertise, consult with security professionals.
- Restore System: Once the infection has been removed, restore the system to a known good state. This may involve restoring from backups, if available. It is crucial to understand the specific recovery procedures for the operating system and applications used.
Recovery from Infection
Recovery involves a series of steps to restore the system to its previous functional state. This often involves restoring from backups, replacing infected files, and ensuring all systems are updated to the latest versions.
- Restore from Backups: If backups are available, restore the system from a recent, known good backup to minimize data loss.
- Replace Infected Files: Replace any infected files with clean copies, ensuring data integrity.
- Update Software: Update all software and security applications to patch any vulnerabilities exploited by the malware.
- Verify System Functionality: Thoroughly test the system’s functionality to ensure all applications and services are operating as expected. Test critical applications to verify their integrity.
- Reinforce Security Measures: Implement enhanced security measures, such as firewalls, intrusion detection systems, and enhanced password policies, to prevent future attacks.
Real-World Examples
The proliferation of malware disguised as legitimate downloads, like the notorious worm masquerading as an IE7 beta, underscores the ever-evolving sophistication of cybercriminals. These tactics prey on user trust and the natural inclination to download software, often exploiting vulnerabilities in software or operating systems. Understanding past incidents provides invaluable insights into how these threats manifest and how they can be mitigated.
Analyzing successful countermeasures can inform future defenses.Malware disguised as legitimate downloads often leverages the same tactics: exploiting user curiosity or urgency, employing misleading file names and descriptions, and leveraging vulnerabilities in software or operating systems. The worm masquerading as IE7 beta is a case study in this approach.
Past Incidents and Mitigation Strategies
Numerous incidents in the past highlight the effectiveness of this tactic. One prominent example involves a campaign distributing a malicious PDF file disguised as a legitimate update for a popular software application. Critically, this highlights the importance of validating the source of downloads, not just relying on perceived legitimacy. Users were enticed to download the malicious file due to a sense of urgency, coupled with the perceived importance of keeping software up to date.
Successful Mitigation Strategies
Successful mitigation strategies often combine multiple approaches, encompassing technical, educational, and policy-based interventions. For instance, in cases where malicious files were distributed through email, implementing strong email security protocols, such as spam filters and anti-phishing measures, proved crucial. Additionally, regularly updating software to patch known vulnerabilities can greatly reduce the risk of exploitation.
Evolution of Malware Techniques
Malware techniques have evolved significantly over time. Early examples often relied on simple social engineering tactics, but modern threats frequently employ advanced techniques like polymorphic code, making them more resilient to detection. Furthermore, the ability to spread malware through various channels, including social media and peer-to-peer networks, further amplifies the potential impact of these threats. The worm masquerading as IE7 beta was a significant example of this evolving sophistication.
It leveraged the popularity of the browser and the user’s desire to keep their software up to date.
Impact of User Education
User education plays a pivotal role in preventing such incidents. By educating users about common red flags, such as suspicious file names, unexpected download requests, and unsolicited emails, organizations can empower their workforce to make informed decisions. Training users to critically evaluate the source of downloads and to exercise caution when clicking on links or attachments can significantly reduce the likelihood of successful attacks.
Wrap-Up

In conclusion, the new worm masquerading as an IE7 beta download highlights the ever-evolving nature of malware threats. By understanding the tactics employed by this and similar malicious programs, and by taking proactive measures like verifying download sources, keeping software updated, and practicing strong password habits, we can significantly reduce the risk of infection. Regular system scans are crucial for detecting and removing malicious software.
The provided mitigation strategies will equip you with the knowledge and tools to protect your systems against this and other threats.