Cybersecurity
-

Amazon Simple Email Service Increasingly Abused in Sophisticated Phishing Campaigns, Evading Traditional Security Measures
The Amazon Simple Email Service (SES), a robust cloud-based email sending platform, is experiencing a significant surge in malicious exploitation…
Read More » -
Checkmarx Grapples with Dark Web Data Leak Following Sophisticated Supply Chain Attacks, LAPSUS$ Group Claims Responsibility.
Checkmarx, a leading provider of application security testing solutions, has officially disclosed that its ongoing forensic investigation into a complex…
Read More » -

Twitter Whistleblower Complaint: The TL;DR Version
A bombshell whistleblower report, filed by Twitter’s former head of security, Peiter "Mudge" Zatko, has ignited a firestorm of controversy,…
Read More » -

The Underground Credit Card Market Transforms as Criminals Adopt Sophisticated Vetting and Operational Strategies
The illicit underground market for stolen credit card data has long been characterized by its inherent volatility and deceptive nature,…
Read More » -
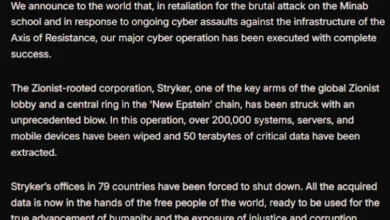
Iranian-Linked Hacktivist Group Handala Claims Massive Data-Wiping Attack on Medical Technology Giant Stryker, Triggering Global Disruptions
A sophisticated and destructive cyberattack targeting Stryker, a global leader in medical technology, has caused widespread operational disruptions across the…
Read More » -

NIST Overhauls National Vulnerability Database Operations Amid Record CVE Growth
The National Institute of Standards and Technology (NIST) has announced a significant restructuring of its National Vulnerability Database (NVD) operations,…
Read More » -

Over 80,000 Hikvision Cameras Remain Vulnerable to Critical, 11-Month-Old Flaw, Posing Widespread Security Risks.
Tens of thousands of surveillance cameras globally have failed to implement a crucial security patch for a critical vulnerability, now…
Read More » -

Kyrgyzstan’s Grinex Cryptocurrency Exchange Halts Operations Following $13.7 Million Hack, Blaming "Western Intelligence Agencies"
Grinex, a cryptocurrency exchange operating out of Kyrgyzstan, has announced the suspension of its services following a sophisticated cyberattack that…
Read More » -
International Law Enforcement Disrupts Global IoT Botnet Network Responsible for Record-Breaking DDoS Attacks
The U.S. Justice Department, in concert with Canadian and German authorities, has successfully dismantled the intricate online infrastructure underpinning four…
Read More » -

Google Strengthens Android Privacy Policies and Intensifies Fight Against Malvertising with AI-Powered Defenses
Google has unveiled a comprehensive suite of policy updates for the Android ecosystem and the Play Store, significantly bolstering user…
Read More »