Checkmarx Grapples with Dark Web Data Leak Following Sophisticated Supply Chain Attacks, LAPSUS$ Group Claims Responsibility.
Checkmarx, a leading provider of application security testing solutions, has officially disclosed that its ongoing forensic investigation into a complex supply chain security incident has confirmed the publication of proprietary company data on the dark web by a prominent cybercriminal group. This revelation escalates an already serious situation for the Israeli security firm, which has been battling a series of breaches targeting its development infrastructure since late March 2026. The company’s announcement, made on April 27, 2026, confirmed that the compromised data is believed to have originated from its GitHub repository, with unauthorized access facilitated by the initial supply chain attack that first came to light on March 23, 2026.
The Unfolding Crisis: Data on the Dark Web
The disclosure from Checkmarx comes after mounting speculation and reports from cybersecurity intelligence platforms. On April 26, 2026, the Dark Web Informer, a well-known X (formerly Twitter) account tracking cybercrime activities, alerted the public to claims made by the notorious LAPSUS$ cybercrime group. According to the Dark Web Informer’s post, LAPSUS$ had listed Checkmarx as one of three new victims on its data leak site, indicating a successful breach and exfiltration of sensitive information. The group, infamous for its extortion tactics and targeting of high-profile technology companies, reportedly claimed to possess a trove of data including source code, an employee database, API keys, and MongoDB/MySQL credentials from Checkmarx.
Checkmarx’s statement acknowledged these claims, stating, "Based on current evidence, we believe this data originated from Checkmarx’s GitHub repository, and that access to that repository was facilitated through the initial supply chain attack of March 23, 2026." This direct link confirms a severe compromise of the company’s development environment, raising immediate concerns about the integrity of its internal operations and the potential downstream impact on the broader software development ecosystem.
Crucially, Checkmarx has sought to reassure its clientele by emphasizing that the compromised GitHub repository is maintained entirely separately from its customer production environment. The company unequivocally stated that no customer data is stored within this repository. This distinction is vital for mitigating panic among its extensive customer base, which relies on Checkmarx for securing their own applications. Despite this assurance, the leak of internal source code, employee data, and critical credentials like API keys and database access details poses significant risks, including potential intellectual property theft, phishing attempts against employees, and the possibility of further lateral movement within Checkmarx’s systems or even exploitation of vulnerabilities within its own products.
Checkmarx’s Response and Assurance
In the wake of the dark web publication, Checkmarx has reinforced its commitment to a thorough and transparent investigation. The company’s forensic probe into the incident is described as ongoing, with dedicated teams actively working to verify the precise nature and scope of the posted data. As part of its immediate incident response efforts, Checkmarx confirmed that it has "locked down access to the affected GitHub repository," a critical step to prevent further unauthorized access or data exfiltration.
The company reiterated its protocol for customer communication in such events: "If we determine that customer information was involved in this incident, we will notify customers and all relevant parties immediately." This commitment aligns with standard cybersecurity best practices and regulatory requirements, aiming to maintain trust and facilitate proactive measures should client data be demonstrably at risk. However, the incident inherently challenges the trust clients place in a cybersecurity vendor whose own systems have been repeatedly breached.
A Chronology of Compromise: From March to April
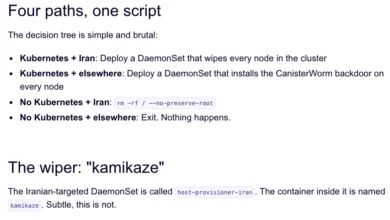
The current dark web leak is not an isolated incident but rather the latest development in a series of sophisticated attacks targeting Checkmarx’s development infrastructure. The timeline of these events paints a concerning picture of persistent targeting by advanced threat actors:
-
March 23, 2026: The Initial Supply Chain Breach. Checkmarx first suffered a significant breach, identified as a supply chain attack. This incident involved the compromise of its GitHub Actions workflows and two plugins distributed via the Open VSX marketplace. The attack vector exploited vulnerabilities within the software supply chain, a common and increasingly dangerous method for cybercriminals. The threat actor, identified as "TeamPCP," was responsible for tampering with these components to deploy a credential stealer. This malware was designed to harvest a wide range of developer secrets, including authentication tokens, API keys, and other sensitive credentials crucial for accessing various development and production environments. The use of the Trivy vulnerability scanner, an open-source tool, in the attack chain was particularly ironic, as Trivy is designed to prevent vulnerabilities, not facilitate attacks. The compromise of GitHub Actions, automated workflows that run code directly within a repository, allowed the attackers to inject malicious code into the build and deployment processes. Similarly, tampering with Open VSX plugins meant that any developer using these compromised plugins would inadvertently install the credential stealer.

-
"Last Week" (Prior to April 27, 2026): Subsequent Attacks and Cascading Impact. In the week leading up to the dark web disclosure, Checkmarx faced further suspected compromises. This time, the financially motivated TeamPCP group was believed to have compromised Checkmarx’s KICS (Keep Infrastructure as Code Secure) Docker image. KICS is Checkmarx’s open-source static analysis solution for Infrastructure as Code (IaC), designed to help developers identify security vulnerabilities in their cloud infrastructure definitions. The compromise of a KICS Docker image, alongside additional VS Code extensions and another GitHub Actions workflow, again involved similar credential-stealing malware. This indicated a continued and persistent effort by the attackers to infiltrate Checkmarx’s development pipelines and exfiltrate sensitive information.
-
Cascading Impact on Bitwarden CLI. The compromise of these Checkmarx-related assets had a significant cascading effect, demonstrating the interconnectedness of modern software development ecosystems. Specifically, the malicious activity led to a brief compromise of the Bitwarden CLI (Command Line Interface) npm package. Bitwarden is a popular open-source password manager, and its CLI tool is widely used by developers for managing credentials. A compromise of such a critical tool can have far-reaching implications, potentially exposing sensitive login information for countless developers and their projects. While the compromise was described as "brief," it highlights the severe downstream risks associated with supply chain attacks on foundational development tools and security vendors. Bitwarden would have undoubtedly acted swiftly to mitigate the threat and issue advisories to its user base, underscoring the rapid response required when such critical infrastructure is impacted.
The Threat Actors: LAPSUS$ and TeamPCP
The involvement of LAPSUS$ in the dark web data publication adds another layer of gravity to the Checkmarx incident. LAPSUS$ is a notorious cybercrime group that emerged in late 2021 and quickly gained infamy for its highly effective social engineering tactics and its focus on extorting large technology companies. Unlike traditional ransomware groups, LAPSUS$ primarily specializes in data exfiltration and extortion, often publishing stolen data if their demands are not met. Their victim list includes a who’s who of global tech giants, such as NVIDIA, Samsung, Microsoft, Okta, and Vodafone, demonstrating their capability to penetrate even the most robust security infrastructures. Their methods often involve bribing insiders, exploiting misconfigured systems, and leveraging stolen credentials to gain initial access, followed by rapid lateral movement and data exfiltration. The group’s public claims and subsequent data dumps serve as powerful psychological pressure tactics.
TeamPCP, the group initially responsible for the March 23 breach, appears to be a distinct but equally sophisticated threat actor. While less publicly documented than LAPSUS$, their ability to execute complex supply chain attacks targeting GitHub Actions and Open VSX plugins, and their persistence in subsequent attacks on KICS Docker images, marks them as a highly capable and financially motivated group. The coordination, or potential collaboration, between TeamPCP and LAPSUS$ remains unclear, but the ultimate public disclosure by LAPSUS$ suggests a possible hand-off of stolen data or a separate, opportunistic exploitation of Checkmarx’s vulnerabilities by the latter.
Understanding the Attack Vectors: GitHub, Supply Chains, and Trust
The series of attacks on Checkmarx underscores critical vulnerabilities inherent in modern software development. GitHub repositories are central to collaborative coding, housing not just source code but also configuration files, API keys, and deployment scripts that, if compromised, offer attackers keys to an organization’s digital kingdom. GitHub Actions, designed to automate software workflows, are powerful tools that, when tampered with, can become potent conduits for malicious code injection into build pipelines.
Supply chain attacks, like those leveraged against Checkmarx, exploit the trust relationships within the software ecosystem. By compromising a single component or dependency (like a GitHub Action, a VS Code extension, or a Docker image), attackers can inject malicious code into countless downstream applications and systems that rely on that component. The irony of a leading application security vendor like Checkmarx being repeatedly targeted and compromised through its own development supply chain is stark. Checkmarx’s own tools are designed to secure software, making these breaches particularly damaging to its reputation and highlighting the universal challenge of securing the complex, interconnected development process.
The specific targeting of Trivy (a vulnerability scanner) and KICS (an Infrastructure as Code security tool) within these attacks is especially notable. It demonstrates attackers’ strategy to subvert the very tools designed to enhance security, effectively turning defenses into attack vectors. This tactic, often referred to as "attacking the security," aims to undermine the foundational trust in security tools themselves.
Broader Industry Implications and Future Challenges
The Checkmarx incidents carry significant implications for the broader cybersecurity industry and software development community.
- Erosion of Trust: When a security vendor is breached, it erodes trust not only in that specific company but also in the broader ecosystem of security tools. Organizations rely on these vendors to protect them, and such incidents raise questions about the efficacy of even the most advanced security measures.
- Sophistication of Supply Chain Attacks: The attacks against Checkmarx highlight the increasing sophistication and prevalence of supply chain attacks. These are no longer theoretical threats but a concrete and persistent danger that can bypass traditional perimeter defenses. Companies must invest more heavily in securing their development pipelines, including code repositories, build systems, and package managers.
- Developer Security: The compromise of developer credentials, API keys, and source code emphasizes the critical need for enhanced developer security practices. This includes multi-factor authentication for all development tools, regular security training, rigorous access controls, and the use of secrets management solutions.
- Interconnectedness Risks: The cascading impact on the Bitwarden CLI npm package perfectly illustrates the interconnected nature of modern software. A vulnerability in one part of the supply chain can quickly propagate and affect numerous other applications and services, leading to widespread disruption.
- Proactive Defense: The industry must move towards more proactive and resilient security architectures that assume compromise is inevitable. This means implementing robust detection and response capabilities, comprehensive logging, and frequent security audits of all development infrastructure.
- Regulatory Scrutiny: Such high-profile breaches will likely intensify regulatory scrutiny on software vendors, pushing for stricter security standards and mandatory disclosure requirements, particularly concerning supply chain vulnerabilities.
As Checkmarx continues its investigation, the cybersecurity community will be watching closely for further details, particularly regarding the exact nature of the data published by LAPSUS$ and any potential impact on its customers, however indirect. This series of events serves as a stark reminder that even companies dedicated to security are not immune to the relentless and evolving threats posed by sophisticated cybercriminal groups, reinforcing the critical importance of continuous vigilance and adaptive security strategies across the entire software development lifecycle. The full ramifications of these breaches for Checkmarx’s standing and for the broader industry’s approach to supply chain security are yet to be fully realized.