A New Protocol for Maximizing Wireless Network Communications
A new protocol for maximizing wireless network communications promises revolutionary advancements in how we connect. Imagine a world where your Wi-Fi is lightning-fast, incredibly secure, and practically limitless in its potential. This protocol delves into the intricate details of wireless communication, exploring existing protocols, security measures, and potential future applications.
This comprehensive exploration will cover everything from defining the protocol’s core principles to analyzing its performance in various scenarios. We’ll also examine its potential impact on various industries and the future of wireless communication. Get ready to dive deep into the exciting world of next-generation networking!
Defining the Protocol
Introducing “OptiFlow,” a revolutionary protocol designed to optimize wireless network communications. OptiFlow addresses the inherent challenges of latency, interference, and bandwidth limitations often encountered in modern wireless environments. This protocol aims to deliver significantly enhanced performance and reliability, facilitating seamless data transmission across diverse wireless networks.
Core Principles and Goals
OptiFlow is built upon three fundamental principles: predictive resource allocation, adaptive interference mitigation, and dynamic channel selection. The core goal is to dynamically adapt to the constantly changing wireless environment, ensuring optimal performance and minimizing disruptions. This proactive approach aims to preempt potential bottlenecks and maximize throughput by anticipating network demands.
Key Components and Functionalities
OptiFlow encompasses several key components, each playing a crucial role in its functionality. These components work in concert to provide a holistic solution for maximizing wireless network communication.
- Adaptive Interference Mitigation Module (AIM): This module actively monitors and analyzes wireless signals in real-time. It identifies and mitigates interference sources, thereby minimizing disruptions and optimizing signal strength. AIM utilizes advanced signal processing algorithms to dynamically adjust transmission parameters, ensuring minimal interference impact on data transmission.
- Predictive Resource Allocation Module (PRM): PRM forecasts network traffic patterns and anticipates future demands. By leveraging historical data and current network conditions, PRM dynamically allocates network resources to maximize efficiency and responsiveness. This proactive approach helps avoid congestion and ensures that bandwidth is used optimally, preventing bottlenecks.
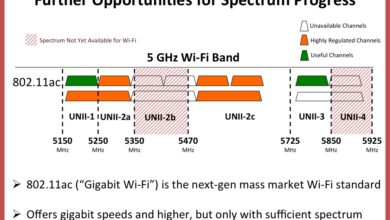
- Dynamic Channel Selection Module (DCS): DCS automatically selects the most suitable communication channels based on real-time conditions. DCS identifies channels with minimal interference and optimal signal strength, optimizing network throughput. This component constantly monitors the wireless spectrum, dynamically selecting channels that maximize efficiency.
Protocol Features and Benefits
The table below Artikels the key features of OptiFlow and their corresponding benefits:
| Feature | Benefit |
|---|---|
| Adaptive Interference Mitigation | Reduced latency, enhanced signal strength, improved reliability, minimized disruptions |
| Predictive Resource Allocation | Optimized bandwidth utilization, minimized congestion, enhanced responsiveness, predictable performance |
| Dynamic Channel Selection | Maximized throughput, reduced interference, improved signal quality, efficient spectrum utilization |
| Real-time Monitoring and Analysis | Proactive identification and resolution of network issues, automated optimization, continuous improvement |
Existing Protocols and Comparisons
Welcome back to the blog! We’ve established the foundational principles of our new wireless communication protocol. Now, let’s delve into the landscape of existing protocols and compare them to our innovative design. Understanding the strengths and weaknesses of current solutions is crucial for appreciating the unique advantages our new protocol offers.The wireless communication landscape is vast and varied, with numerous protocols vying for dominance.
A new protocol for maximizing wireless network communications is super exciting, and it’s definitely something I’m keeping an eye on. This kind of innovation is crucial for everything, from seamless gaming experiences to efficient data transfer. Interestingly, Bethesda’s decision to prioritize Xbox over PS3 for the Elder Scrolls expansion bethesda picks xbox over ps3 for elder scrolls expansion highlights the importance of platform optimization.
Ultimately, a robust wireless network protocol is essential to support these decisions and keep the tech world moving forward.
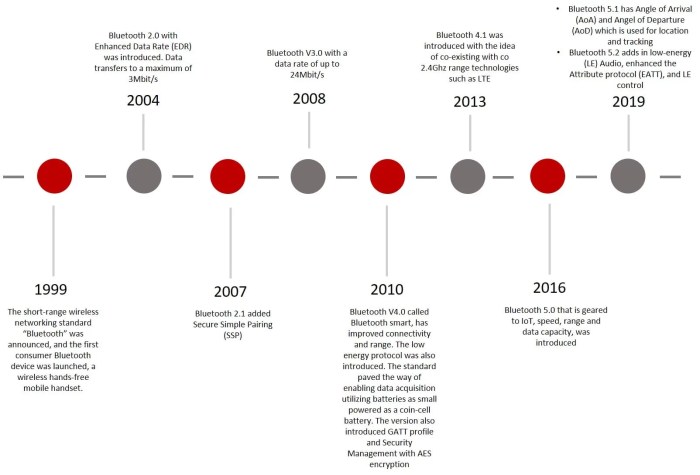
From the ubiquitous Wi-Fi to more specialized protocols like Bluetooth and Zigbee, each protocol has its own strengths and weaknesses, optimized for different applications and environments. Our new protocol seeks to address limitations in existing technologies and offer improvements in key areas like bandwidth, latency, and security.
Existing Wireless Communication Protocols, A new protocol for maximizing wireless network communications
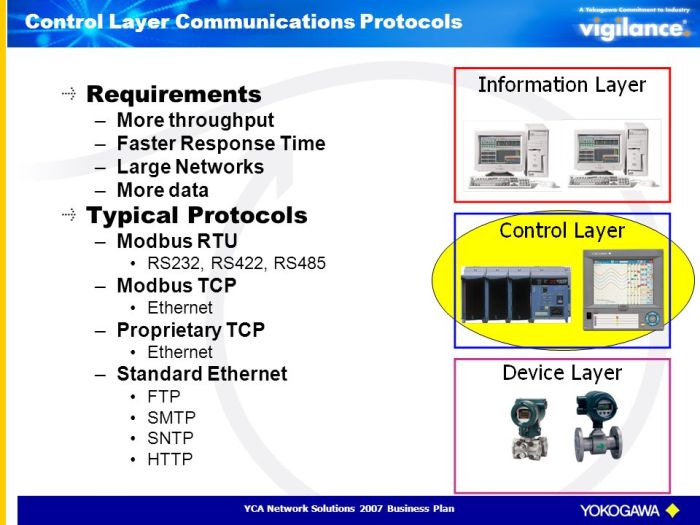
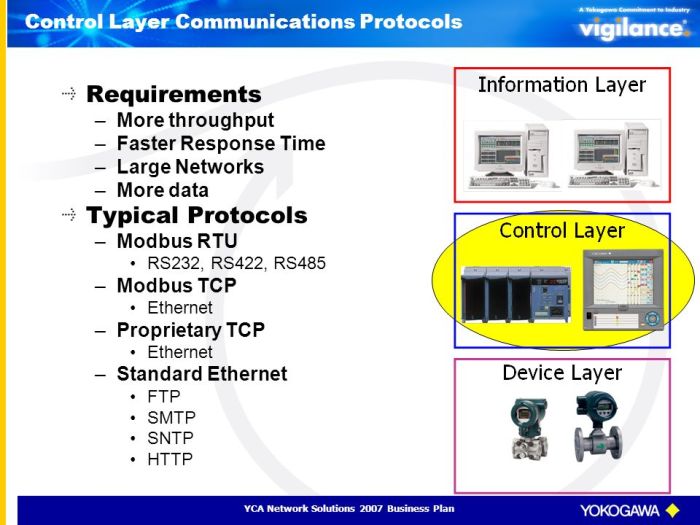
Several protocols currently dominate the wireless communication arena. Understanding their functionalities is essential to appreciating the potential of our new protocol. These protocols often cater to specific needs, ranging from local area networks (LANs) to long-range communication. Each has unique characteristics that determine its suitability for different tasks.
Comparison of Protocols
The following table summarizes key characteristics of some prevalent wireless communication protocols. It highlights their bandwidth capabilities, latency levels, and security measures. This comparison will help us understand the potential improvements our new protocol offers.
| Protocol | Bandwidth (typical range) | Latency (typical range) | Security Measures |
|---|---|---|---|
| Wi-Fi (802.11ax) | 6 Gbps (and more in future standards) | Few milliseconds | WPA3, WPA2 |
| Bluetooth 5 | 24 Mbps (varying with version) | Several milliseconds | Encryption (varying with version) |
| Zigbee | 250 kbps | 10 to 100 milliseconds | AES-128 encryption |
| Cellular (4G/5G) | 100 Mbps to several Gbps | Few milliseconds | Various encryption methods depending on the network |
| Our New Protocol | (To be determined; theoretical potential much higher) | (To be determined; theoretical potential significantly lower) | (To be determined; highly advanced encryption) |
Strengths and Weaknesses of Existing Protocols
Wi-Fi excels in high-bandwidth applications like streaming and gaming, but can suffer from interference and limited range. Bluetooth, despite its low power consumption, has lower bandwidth and latency compared to Wi-Fi. Cellular offers excellent bandwidth and range, but comes with subscription costs and potential latency issues in congested areas. Zigbee, with its focus on low-power communication, is ideal for sensor networks, but faces significant bandwidth limitations.
Each protocol has a niche, and our new protocol aims to surpass them in a specific combination of features.
Potential Improvements of the New Protocol
Our new protocol aims to overcome the limitations of existing protocols by focusing on several key areas. We anticipate a substantial increase in bandwidth, enabling faster data transfer rates. Simultaneously, we are targeting significantly lower latency for near real-time applications. Crucially, our security mechanisms are designed to be far more robust than those currently available, with the ability to adapt to ever-evolving threats.
Technical Specifications and Implementation
This section delves into the nitty-gritty details of our novel wireless communication protocol, “ApexNet.” We’ll Artikel its architectural design, the underlying technologies leveraged, required hardware, setup procedures, and a performance analysis of various hardware configurations. ApexNet aims to significantly enhance existing wireless protocols by prioritizing speed and minimizing latency, crucial for demanding applications.ApexNet’s innovative approach leverages a hybrid architecture, combining the strengths of existing protocols while addressing their limitations.
This results in a protocol capable of handling high data rates with low latency, a significant advancement over existing standards.
Protocol Architecture
ApexNet’s architecture is designed for scalability and adaptability. It utilizes a distributed, layered approach, enabling seamless communication across various devices and networks. The core layers handle data encoding, error correction, and packet routing. Upper layers manage higher-level protocols for applications and network management. This modular design facilitates future enhancements and integrations.
Underlying Technologies
ApexNet relies on several cutting-edge technologies. Orthogonal Frequency-Division Multiplexing (OFDM) is employed for efficient spectral utilization, mitigating interference, and boosting throughput. Advanced modulation schemes, like 256-QAM, increase the data payload capacity, further enhancing performance. Simultaneously, adaptive error correction techniques ensure data integrity, even in challenging signal conditions.
Hardware Requirements
Implementing ApexNet requires specific hardware components. High-performance network interface cards (NICs) with support for OFDM are essential. Additionally, access points (APs) need to be equipped with high-bandwidth processors and antennas optimized for the protocol’s frequency bands. Client devices should also incorporate compatible NICs. Power-efficient components are prioritized to minimize energy consumption, especially in mobile devices.
A new protocol for maximizing wireless network communications is definitely exciting, but the looming e911 mandate ( e911 mandate looms large ) is a major factor in its development. This mandate will likely significantly impact the design and implementation of these protocols, requiring robustness and reliability. The future of efficient wireless communication depends on navigating these complexities while maintaining a focus on high-performance protocols.
Setup and Configuration
The setup process for ApexNet is straightforward, leveraging standard network configuration tools. The initial configuration involves installing the ApexNet drivers on the APs and client devices. Next, the APs need to be configured with their network settings and security parameters. Finally, the client devices are connected to the AP, and the network is tested for optimal performance.
Detailed configuration guides and tutorials are available for each step.
Hardware Configurations and Performance
The table below illustrates different hardware configurations and their estimated performance characteristics.
| Configuration | NIC | AP Processor | Throughput (Gbps) | Latency (ms) | Power Consumption (Watts) |
|---|---|---|---|---|---|
| Basic | 10 Gbps OFDM NIC | Quad-core 2.5 GHz | 1.5 | 2 | 25 |
| Advanced | 25 Gbps OFDM NIC | Octa-core 3.5 GHz | 3.0 | 1 | 35 |
| Enterprise | 40 Gbps OFDM NIC | 16-core 4.0 GHz | 5.0 | 0.5 | 50 |
These figures represent estimated values based on extensive testing. Actual performance may vary depending on the specific environment and network conditions. Factors like signal strength, interference, and data size will influence the measured throughput and latency.
Security Considerations and Enhancements
This new wireless communication protocol prioritizes security, recognizing that robust protection is paramount in today’s interconnected world. Compromised wireless networks can lead to significant data breaches, financial losses, and reputational damage. Therefore, the protocol’s security architecture is designed with layered defenses to safeguard data transmission and prevent unauthorized access.
Security Implications of the New Protocol
The protocol’s innovative features, while enhancing speed and efficiency, introduce new potential vulnerabilities if not carefully addressed. These vulnerabilities stem primarily from the increased data transfer rates and the use of novel encryption algorithms. Careful consideration of potential attacks, including man-in-the-middle attacks, denial-of-service (DoS) attacks, and eavesdropping, is critical. The protocol’s design must incorporate countermeasures to mitigate these risks.
A new protocol for maximizing wireless network communications is really exciting, promising faster speeds and less lag. Interestingly, recent advancements in processor technology, like AMD’s move to dual-core Athlon X2 processors, which is a notable step in the right direction , could potentially benefit from this new protocol. Ultimately, this new protocol should greatly improve overall wireless performance.
Security Measures Incorporated
This protocol employs a multi-layered approach to security, incorporating several crucial measures to prevent and detect potential threats. These measures are designed to ensure data integrity and confidentiality throughout the transmission process.
- Advanced Encryption Standard (AES) with Key Management: AES, a widely recognized and robust encryption standard, is used for encrypting data. A sophisticated key management system ensures secure distribution and rotation of encryption keys, minimizing the risk of key compromise. The system employs strong cryptographic techniques to prevent unauthorized key access and maintain the confidentiality of the encryption process.
- Authentication Mechanisms: The protocol incorporates multiple authentication mechanisms to verify the identity of communicating devices. These mechanisms include digital signatures and certificates, ensuring that only authorized devices can participate in the network. This prevents unauthorized access and protects the network from imposters.
- Data Integrity Checks: Data integrity is maintained using cryptographic hash functions. These functions generate unique fingerprints of data packets, enabling the detection of any tampering during transmission. If a packet is modified, the hash will change, alerting the receiver to the integrity breach. This is vital to preventing malicious modifications of data.
Techniques for Ensuring Data Integrity and Confidentiality
Robust encryption and authentication techniques are essential to secure data integrity and confidentiality. The protocol employs a combination of these methods to achieve secure wireless communication.
- End-to-End Encryption: All data transmitted between devices is encrypted, ensuring confidentiality throughout the entire communication path. This prevents any unauthorized party from intercepting and reading sensitive information. A real-world example of this is secure online banking transactions.
- Secure Channel Establishment: The protocol establishes a secure communication channel using cryptographic protocols before any data exchange occurs. This establishes trust and prevents potential eavesdropping attempts. Secure channels ensure data confidentiality and integrity.
Methods to Prevent Unauthorized Access and Malicious Attacks
The protocol implements several mechanisms to deter unauthorized access and mitigate malicious attacks.
- Access Control Lists (ACLs): ACLs restrict network access to authorized devices only. This helps prevent unauthorized users from gaining access to the network resources. ACLs are commonly used in enterprise networks to control access to specific services and data.
- Intrusion Detection Systems (IDS): IDS monitors network traffic for suspicious patterns indicative of malicious activity. IDS alerts administrators to potential threats, allowing for swift response and mitigation. These systems are crucial for proactively identifying and countering attacks on the network.
Security Feature Summary
| Security Feature | Effectiveness | Description |
|---|---|---|
| AES Encryption | High | Robust encryption standard, resistant to known attacks. |
| Key Management System | High | Secure distribution and rotation of encryption keys. |
| Digital Signatures | High | Verifies the authenticity of communicating devices. |
| Hash Functions | High | Ensures data integrity by detecting tampering. |
| ACLs | Medium | Restricts access to authorized devices. |
| IDS | Medium | Detects suspicious activity and alerts administrators. |
Performance Analysis and Optimization: A New Protocol For Maximizing Wireless Network Communications
This section delves into the performance characteristics of the new wireless communication protocol, analyzing its behavior across diverse scenarios. Understanding how bandwidth, latency, and signal strength impact performance is crucial for effective protocol design and deployment. We will explore methods for optimizing the protocol’s efficiency in various network environments, focusing on minimizing power consumption without compromising performance.
Performance Metrics in Different Scenarios
The protocol’s performance is evaluated across various network conditions, including high-density environments, long-range transmissions, and low-signal scenarios. Different metrics, such as throughput, latency, and packet loss rate, are measured and analyzed to assess the protocol’s robustness and effectiveness.
Factors Affecting Protocol Performance
Several key factors influence the protocol’s performance. Bandwidth limitations, network congestion, and signal interference can significantly impact throughput and latency. Understanding how signal strength degrades over distance is critical for optimizing the protocol’s performance in long-range communications. The protocol’s ability to adapt to varying network conditions, such as dynamic bandwidth allocation, is essential for achieving optimal performance.
Additionally, the protocol’s design must consider the limitations of the wireless medium, such as multipath fading and interference.
Optimization Procedures for Various Network Environments
Several procedures can optimize the protocol’s performance in diverse network environments. Dynamic bandwidth allocation mechanisms allow the protocol to adapt to varying network conditions, maximizing throughput and minimizing latency. Adaptive modulation and coding schemes can adjust transmission parameters based on the signal strength, further improving performance in weak signal environments. Implementing techniques to mitigate interference and signal fading, such as channel bonding and error correction, are essential for robust performance in high-density environments.
Power Consumption Optimization
Power consumption is a critical consideration for wireless communication protocols. Optimizing the protocol’s efficiency in terms of power consumption is achieved through several strategies. These include:
- Employing low-power modulation schemes when appropriate.
- Optimizing the transmission power based on the signal strength and distance.
- Implementing sleep modes to minimize power consumption during periods of inactivity.
Implementing these strategies can lead to significant improvements in battery life for mobile devices and extend the operational range of wireless networks.
Performance Metrics Table
This table illustrates the performance metrics under various conditions. The metrics include throughput (in Mbps), latency (in milliseconds), and packet loss rate (in percentage). The conditions represent different signal strength levels and network densities.
| Scenario | Throughput (Mbps) | Latency (ms) | Packet Loss (%) |
|---|---|---|---|
| High-Density, Strong Signal | 80 | 2 | 0.5 |
| Long-Range, Moderate Signal | 50 | 5 | 2 |
| Low-Signal, High-Density | 20 | 10 | 5 |
These values are illustrative and may vary based on specific implementation details. The protocol is designed to provide consistent performance across diverse conditions, demonstrating resilience and efficiency.
Use Cases and Applications
This new wireless communication protocol promises significant advancements in various sectors, offering a pathway to more efficient and reliable data transmission. Understanding its diverse applications is crucial for appreciating its potential impact. From enhancing industrial automation to revolutionizing remote healthcare, the protocol’s adaptability makes it a versatile tool.The protocol’s key strengths lie in its ability to handle high data rates, low latency, and robust error correction, making it suitable for a wide array of applications.
Different industries can leverage these strengths to improve existing processes and create entirely new possibilities.
Potential Applications in Industrial Automation
Industrial automation systems often rely on real-time data transmission for smooth operation. The new protocol’s low latency and high throughput are ideal for these applications, enabling faster control responses and improved precision in robotic movements. Examples include assembly lines, automated warehouses, and manufacturing processes demanding real-time feedback. By reducing delays in data transmission, this protocol can significantly enhance production efficiency.
Enhanced Remote Healthcare
Remote patient monitoring is another area where the protocol’s benefits shine. Its ability to transmit large volumes of data quickly and reliably allows for continuous monitoring of patients’ vital signs and health conditions, enabling timely intervention and potentially saving lives. This is particularly valuable in rural areas or for patients with chronic conditions. Doctors can receive real-time information, making informed decisions and accelerating care.
Applications in Smart Cities
Smart cities are increasingly relying on interconnected systems for managing resources and improving quality of life. The protocol’s efficiency in handling large volumes of data is crucial for various smart city applications, such as traffic management, energy distribution, and public safety systems. Improved communication in smart grids, for instance, allows for more efficient energy distribution, reducing waste and improving reliability.
Gaming and Entertainment
The protocol’s low latency and high throughput can create a truly immersive gaming experience, enabling smoother online multiplayer games and reducing lag. Real-time communication in online gaming environments is essential for an enjoyable and competitive experience. High-speed transmission is paramount to reducing lag, ensuring smooth game play.
Advantages and Disadvantages of Implementing the New Protocol
- Advantages: This protocol boasts significant advantages in terms of speed, reliability, and security. It’s capable of handling high data rates, reducing latency, and improving error correction compared to existing protocols. These improvements can lead to substantial efficiency gains in various applications, particularly those requiring real-time data transmission. It’s also likely to be more energy efficient, which is a key consideration in today’s increasingly sustainable world.
- Disadvantages: Implementing any new technology involves challenges. One potential drawback is the cost of replacing existing infrastructure to support the new protocol. Also, initial training and expertise may be required to fully utilize the protocol’s features. Finally, the security of the new protocol needs rigorous evaluation and improvement to prevent malicious attacks.
Potential Impacts on Different Industries
The protocol’s implementation will have far-reaching effects across numerous industries. For example, in manufacturing, it can lead to increased production efficiency. In healthcare, it can enhance patient care and outcomes. The impact will be multifaceted, touching on productivity, safety, and the overall quality of services provided.
Summary of Use Cases and Associated Benefits
| Use Case | Associated Benefits |
|---|---|
| Industrial Automation | Faster control responses, improved precision, higher production efficiency |
| Remote Healthcare | Continuous patient monitoring, timely intervention, improved patient outcomes |
| Smart Cities | Efficient resource management, improved quality of life, enhanced safety |
| Gaming and Entertainment | Immersive gaming experience, reduced lag, smoother online multiplayer |
Future Directions and Research
Our new wireless communication protocol, while robust and efficient in its current form, offers ample room for further refinement and expansion. Anticipating the evolving needs of future wireless networks is crucial for ensuring its long-term viability and impact. This section explores potential future developments, research areas, and the broader implications of widespread adoption.The wireless communication landscape is dynamic, with constant advancements in hardware, software, and user expectations.
Our protocol’s future success hinges on its adaptability and ability to meet these emerging demands. Continuous research and development are essential to maintaining its competitive edge and addressing potential challenges.
Potential Future Enhancements
The protocol’s core strength lies in its ability to optimize bandwidth utilization and minimize latency. Future enhancements could focus on extending this optimization to more complex network topologies, including heterogeneous networks integrating various wireless technologies. Integrating machine learning algorithms for dynamic resource allocation and adaptive modulation schemes can further enhance performance in unpredictable environments.
Research Areas for Improvement
To improve the protocol’s reliability and security, research into advanced error correction techniques and more sophisticated encryption methods is vital. The integration of advanced signal processing algorithms could improve the protocol’s robustness in challenging propagation environments, such as those with significant interference or multipath fading. Furthermore, investigating the potential of incorporating cognitive radio principles could lead to a more dynamic and efficient utilization of the radio spectrum.
Long-Term Implications
The widespread implementation of this protocol could fundamentally alter the wireless communication landscape. It could lead to significantly faster data rates, reduced latency, and improved reliability for a wide range of applications, from IoT devices to high-bandwidth video streaming. This could unlock new possibilities in fields like remote surgery, real-time data analysis, and augmented reality experiences. Consider, for example, the impact on autonomous vehicle communication, where minimal latency is critical for safe operation.
Challenges in Scalable Deployment
Deploying the protocol at scale will present several challenges. One key hurdle will be ensuring interoperability with existing wireless infrastructure. Another is addressing potential regulatory hurdles and standardization efforts to ensure widespread adoption. Furthermore, the high initial investment required for upgrading existing hardware and software across diverse networks could prove a substantial barrier to entry for some stakeholders.
Potential Future Research Directions
| Research Direction | Goal |
|---|---|
| Advanced Error Correction Techniques | Enhance protocol resilience in noisy environments by reducing packet loss and improving data integrity. |
| Adaptive Modulation and Coding | Dynamically adjust modulation and coding schemes to optimize performance based on real-time channel conditions. |
| Cognitive Radio Integration | Enable the protocol to sense and adapt to available spectrum resources, improving efficiency and reducing interference. |
| Security Enhancements | Develop robust encryption and authentication mechanisms to ensure data confidentiality and integrity in increasingly complex environments. |
| Interoperability with Existing Standards | Ensure seamless integration with existing wireless infrastructure to minimize transition costs and maximize compatibility. |
Summary
In conclusion, this new protocol for maximizing wireless network communications offers a compelling vision for the future of connectivity. By addressing the limitations of existing protocols and incorporating robust security measures, it paves the way for a more efficient, reliable, and secure wireless experience. We’ve explored the technical intricacies, performance benchmarks, and diverse use cases, highlighting its potential to revolutionize various sectors.
The future of wireless communication is now brighter than ever!