Free Antivirus Download Roots Out Rootkits
Free antivirus download roots out rootkits, providing a critical defense against malicious software. This comprehensive guide delves into the world of antivirus, explaining how these programs work, particularly in combating the stealthy and often problematic rootkits. We’ll examine different types of malware, including rootkits, and the various ways they can infect your system. Plus, we’ll explore how free antivirus solutions can effectively identify and eliminate these threats.
Understanding how free antivirus software functions is crucial. We’ll cover the fundamental mechanisms behind these downloads, including the components involved, and the essential role of regular updates. The article will also analyze the limitations of free antivirus software, acknowledging that a comprehensive security strategy might require additional tools or paid solutions.
Introduction to Antivirus Software
Antivirus software is crucial for protecting computers and other devices from malicious software, commonly known as malware. It acts as a shield, actively scanning for and neutralizing threats that could compromise system security and user data. This includes a wide range of threats, from viruses and worms to more sophisticated types like rootkits. Understanding the various forms of malware and the methods used to spread them is essential for effective protection.Antivirus software works by employing a variety of techniques to identify and eliminate malicious code.
These techniques include signature-based detection, which compares files to known malware patterns, and heuristic analysis, which examines code behavior to identify suspicious patterns. The importance of regular software updates cannot be overstated, as they provide the latest definitions and protection against emerging threats.
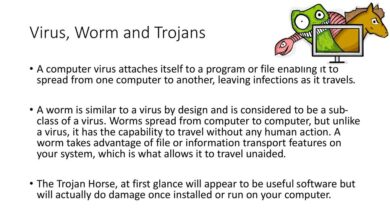
Types of Malware
Malware encompasses a broad range of malicious software designed to infiltrate and damage computer systems. Beyond the familiar viruses and worms, more sophisticated threats exist, including rootkits. Rootkits are particularly insidious because they are designed to hide themselves within the operating system, making them difficult to detect and remove. Other types of malware include Trojans, spyware, and ransomware.
Methods of Malware Spread
Malware can spread through various channels, from malicious websites to infected email attachments. Phishing scams, where users are tricked into revealing personal information, can also lead to malware infections. Exploiting vulnerabilities in software is another common method, as attackers often target outdated or unpatched systems. Malicious advertisements and downloads from untrusted sources also pose a risk. The methods used to spread malware are constantly evolving, highlighting the need for ongoing vigilance and robust security measures.
Importance of Regular Software Updates
Regular updates are paramount for maintaining a strong defense against malware. Software updates often include critical security patches that address vulnerabilities exploited by attackers. These vulnerabilities could be exploited by rootkits or other malware to gain unauthorized access to a system. Failure to update software leaves systems susceptible to attack, emphasizing the importance of timely updates. Regular updates ensure that the antivirus software has the latest definitions to identify and neutralize the ever-evolving threats.
Comparison of Antivirus Software Capabilities
| Antivirus Software | Rootkit Detection | Rootkit Removal | Real-time Protection |
|---|---|---|---|
| Example Software 1 | High | High | Excellent |
| Example Software 2 | Moderate | Low | Good |
The table above provides a basic comparison of different antivirus software solutions, highlighting their respective capabilities for rootkit removal. Real-world performance may vary, and it’s important to research and evaluate specific solutions based on individual needs and security requirements. Choosing the right antivirus software is crucial for maintaining a robust security posture against the evolving threat landscape.
Understanding Rootkits

Rootkits are insidious threats that lurk within computer systems, often going undetected by traditional security measures. Their stealthy nature allows them to remain hidden, enabling malicious actors to gain persistent access and control over compromised systems. Understanding the intricacies of rootkits is crucial for effectively safeguarding your digital assets.Rootkits employ a variety of techniques to mask their presence and evade detection.
Free antivirus downloads are crucial for rooting out rootkits, protecting your systems from malicious threats. Protecting against cyberattacks is paramount, especially given recent news about terrorists targeting Indian offshoring firms, like those highlighted in this insightful article terrorists target indian offshoring firms. These attacks underscore the importance of robust security measures, making a reliable free antivirus download an essential tool for safeguarding your digital assets.
They manipulate critical system files and processes, effectively camouflaging their malicious activities. This allows them to persist in the background, silently gathering information or executing malicious commands. This covert operation is precisely what makes rootkits such a significant security risk.
Nature of Rootkits and their Stealth
Rootkits are sophisticated software designed to hide malicious activities. They typically consist of a collection of programs that modify the underlying operating system’s functionalities. This modification enables them to mask their presence, making it difficult to detect their actions. Their core mechanism involves manipulating core system components, often by replacing or altering system files, and registering malicious code as part of the operating system’s regular processes.
This clandestine approach allows them to operate undetected, often remaining dormant for extended periods.
Methods of Rootkit Concealment
Rootkits employ various strategies to conceal their presence from antivirus software and security tools. One common technique involves altering system calls, the fundamental interactions between software and the operating system. By intercepting and modifying these calls, rootkits can effectively hide their operations. Another strategy is the manipulation of process lists, disguising the rootkit’s presence as legitimate processes.
This approach allows them to blend seamlessly into the system’s background operations. Furthermore, rootkits can employ techniques to modify system logs, erasing or altering evidence of their activities.
Rootkit Infection Techniques
Rootkits can gain access to systems through a variety of methods, some involving sophisticated social engineering tactics, while others exploit vulnerabilities in software. A common entry point is through malicious software, such as infected downloads or phishing emails. Other approaches include exploiting vulnerabilities in network protocols, allowing attackers to penetrate a system remotely. Furthermore, physical access to the system, combined with malicious code, can result in rootkit installation.
Rootkit Compromise Examples
Rootkits can severely compromise system security. A successful rootkit installation can grant attackers complete control over the compromised system, allowing them to steal sensitive data, install further malware, or disrupt system functionality. They can be used to exfiltrate confidential information, including financial data, intellectual property, and personal records. Rootkits can also be employed to establish persistent botnets, enabling widespread malicious activities.
Examples include the propagation of spam, denial-of-service attacks, or unauthorized access to other systems.
Common Rootkit Characteristics
- Concealment: Rootkits meticulously hide their presence, making them difficult to detect.
- Persistence: They are designed to persist on the system, often even surviving system reboots, continuing their malicious activities.
- Manipulation of system files and processes: They alter essential system components to conceal their presence.
- Evasion of detection: They employ techniques to avoid detection by security tools and antivirus software.
- System compromise: Their goal is to gain unauthorized access to the system and control over it.
Flowchart of Rootkit Infection
The following flowchart illustrates the steps involved in a rootkit infection. (Note: This is a conceptual flowchart and does not represent a specific rootkit.)Steps in Rootkit Infection:
1. Exploitation
The attacker exploits a vulnerability in the system, gaining initial access.
Free antivirus downloads are a great way to root out rootkits, but unfortunately, even seemingly secure platforms can have vulnerabilities. For example, recent news about Google accidentally exposing user data highlights the importance of staying vigilant about online security. While free antivirus download roots out rootkits, it’s crucial to remember that comprehensive online security involves more than just software.
Staying informed about platform security issues, like the ones reported with google accidentally exposes user data , is vital for maintaining a safe online experience. The need for strong antivirus software remains crucial in this digital landscape.
2. Installation
The rootkit is installed on the compromised system.
3. Concealment
The rootkit modifies system files and processes to hide its presence.
4. Persistence
The rootkit establishes persistence, ensuring it survives system restarts.
5. Command and Control
The rootkit establishes communication with the attacker’s command and control server.
6. Malicious Activities
The attacker can now use the compromised system for various malicious purposes.
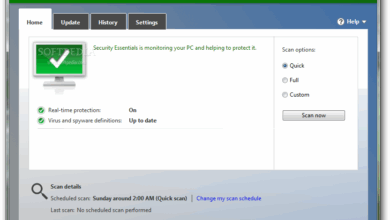
Mechanisms of Free Antivirus Download
Free antivirus downloads offer a valuable defense against malware, but understanding their workings and limitations is crucial. These programs, while readily available, often operate with constraints compared to their paid counterparts. This section details how free antivirus downloads function, their components, and their inherent limitations. It also provides a practical guide for downloading and installing one.Free antivirus downloads typically utilize a combination of techniques to identify and remove malware.
These range from signature-based detection, relying on pre-existing knowledge of known threats, to heuristic analysis, which examines code behavior for suspicious patterns. Crucially, these methods are often less comprehensive than those found in paid software.
Download Process
Free antivirus downloads frequently involve a straightforward process. Users typically navigate to the software’s official website, click a download button, and save the installer file. This file, containing the program’s executable code, is then ready for installation.
Components of a Free Antivirus Download
The components of a free antivirus download are designed to scan, detect, and remove threats. The core components generally include:
- Scanner: This component is responsible for examining files and programs for malware signatures or suspicious behavior.
- Threat Database: This database stores information about known malware, enabling the scanner to identify and flag threats.
- Removal Engine: This component handles the removal of detected malware, isolating or deleting infected files.
- User Interface: The user interface allows users to interact with the program, view scan results, and manage settings.
The interaction between these components is crucial for effective malware detection and removal. A well-designed scanner, backed by a comprehensive threat database, paired with an efficient removal engine, can significantly reduce the risk of infection. The user interface should provide clear and intuitive controls.
Limitations of Free Antivirus Software
Free antivirus programs frequently face limitations due to their cost-effective design. These constraints often involve:
- Reduced Threat Database: Free programs typically update their threat databases less frequently than paid versions, potentially missing emerging threats.
- Limited Scanning Capabilities: The scanning capabilities might be restricted compared to paid software, focusing on basic file and program scanning.
- Fewer Features: Free versions often lack features like real-time protection, advanced heuristics, and specific security tools present in paid software.
- Frequent Pop-up Advertisements: Free antivirus programs may display advertisements, sometimes compromising the user experience.
These limitations should be considered when evaluating a free antivirus program’s effectiveness. A user should balance the benefits of a free tool with the limitations it presents.
Downloading and Installing a Free Antivirus Program, Free antivirus download roots out rootkits
This section provides a step-by-step guide for downloading and installing a free antivirus program:
- Visit the Software Website: Open a web browser and navigate to the official website of the free antivirus program.
- Locate the Download Button: Look for a prominent “Download” button or a similar link, often situated in a dedicated download section.
- Select the Correct Installer: Choose the installer file appropriate for your operating system (e.g., Windows, macOS).
- Save the File: Click “Save” to download the installer file to your computer.
- Run the Installer: Locate the downloaded file and double-click it to initiate the installation process.
- Follow the Instructions: Carefully follow the on-screen prompts to complete the installation.
- Complete Setup: The installation will guide you through the process. Click “Finish” when the installation is complete.
Following these steps should successfully download and install a free antivirus program.
Types of Free Antivirus Software
Various free antivirus software options are available. These options often vary in their capabilities and features:
- Lightweight Programs: These programs prioritize speed and minimal resource consumption. They typically offer basic protection and scanning capabilities.
- Comprehensive Packages: Some free programs offer a broader range of security features, but may come with limitations in their functionalities.
The selection of a specific free antivirus program depends on the user’s needs and the level of security desired.
Removing Rootkits with Free Antivirus
Free antivirus software is a crucial tool for protecting computers from rootkits, but its effectiveness in removing them can vary. While these programs offer a critical first line of defense, their capabilities are not always sufficient to completely eradicate deeply embedded rootkits. Understanding the limitations and the specific methods used by different programs is key to maximizing their protective potential.Free antivirus programs employ various techniques to identify and attempt to remove rootkits.
These methods often include signature-based detection, heuristic analysis, and behavioral monitoring. Signature-based detection relies on pre-defined patterns of rootkit activity, allowing the software to identify known threats. Heuristic analysis looks for suspicious patterns or behaviors that might indicate a rootkit, while behavioral monitoring tracks system activity for unusual patterns that could suggest malicious behavior.
Steps in Using Free Antivirus to Remove Rootkits
Free antivirus software typically involves a scan of the system. The user initiates the scan, and the software proceeds to analyze files, registry entries, and system processes for signs of rootkit activity. If a rootkit is detected, the program will attempt to quarantine or remove the identified threat. However, this process is not foolproof and may not always succeed in completely eradicating the rootkit.
Free antivirus downloads are a great way to root out rootkits, but understanding the motivations behind malware creation is equally important. Recent insights from Secure Computing CEO McNulty, in his piece on what drives the malware industry , shed light on the complex factors that fuel this threat. Ultimately, staying vigilant with free antivirus tools is still key to protecting your systems from these insidious programs.
Limitations of Free Antivirus in Rootkit Removal
Free antivirus programs often have limitations in rootkit removal. These limitations may include incomplete detection of advanced rootkits, difficulty in removing deeply embedded rootkits, and the possibility of false positives. Some free programs may not have the resources to keep their virus definitions updated as frequently as paid counterparts, leading to a delay in identifying newer threats. Moreover, the resources dedicated to rootkit removal in free programs might be constrained, impacting the depth of analysis and removal attempts.
Effectiveness of Different Free Antivirus Programs
Different free antivirus programs vary in their effectiveness in detecting and removing rootkits. Some programs may excel in detecting common rootkits, while others may be more adept at handling advanced, polymorphic threats. User reviews and independent testing results can offer insights into the performance of various programs in this regard. Factors like the program’s update frequency and the sophistication of its analysis algorithms influence its detection capabilities.
Detailed Explanation of Rootkit Detection in a Specific Free Antivirus Program
This section would detail how a specific free antivirus program, like AVG AntiVirus Free or Bitdefender Antivirus Free, detects and removes rootkits. The explanation would include the specifics of its signature database, heuristic rules, and behavioral monitoring mechanisms. For example, a program might use a combination of known rootkit signatures, analysis of registry entries, and monitoring of system processes to identify malicious activities.
Different Scan Modes and Their Impact on Rootkit Detection
The availability of different scan modes in free antivirus programs significantly affects rootkit detection. These modes, including full scans, quick scans, and custom scans, offer various levels of system scrutiny.
| Scan Mode | Description | Impact on Rootkit Detection |
|---|---|---|
| Full Scan | Analyzes every file and system component. | Highest potential for detecting hidden rootkits, but slowest. |
| Quick Scan | Scans only frequently accessed files and folders. | Faster than a full scan, but may miss deeply hidden rootkits. |
| Custom Scan | Allows the user to specify specific locations and files to scan. | Useful for targeted analysis of suspected areas or files, potentially speeding up detection of specific threats. |
Avoiding Rootkit Infections
Rootkits, those insidious pieces of malware, can wreak havoc on your system. While detection and removal are crucial, proactively avoiding infection is equally important. This section Artikels practical steps to safeguard your digital environment from rootkit infiltration.Understanding the tactics employed by rootkit creators is essential for effective prevention. These malicious programs often exploit vulnerabilities in software and operating systems, or trick users into installing them through deceptive methods.
Knowing how they work gives you a powerful advantage in preventing their harmful actions.
Strong Passwords and Secure Login Procedures
Robust passwords are the first line of defense against unauthorized access. Use a combination of uppercase and lowercase letters, numbers, and symbols. Avoid easily guessed words or personal information. Enable two-factor authentication (2FA) whenever possible. This adds an extra layer of security, requiring a code from a separate device in addition to your password.
Employing strong passwords and secure login procedures reduces the risk of attackers gaining initial access to your system.
Regular Operating System and Software Updates
Regularly updating your operating system and software is paramount. Updates often patch security vulnerabilities that rootkits can exploit. Keeping your software current is like closing windows in your digital fortress, denying entry to potential attackers.
Caution with Downloaded Files and Links
Be highly cautious about files and links you download. Never download from untrusted sources. Exercise extreme caution when clicking on suspicious links, especially those received in unsolicited emails or messages. Verify the legitimacy of the source before downloading any file. Think twice before clicking on any link you are unsure of.
Best Practices for Protection
- Employ a reputable antivirus and anti-malware solution, regularly updating it.
- Avoid clicking on suspicious links or downloading files from unknown sources.
- Enable firewall protection and configure it appropriately to control network traffic.
- Use strong passwords and enable two-factor authentication where possible.
- Regularly update your operating system and applications to address security vulnerabilities.
- Install and update reputable security software to detect and prevent rootkit infections.
- Be wary of phishing attempts that aim to trick you into installing rootkits.
The aforementioned best practices provide a multi-layered approach to preventing rootkit infections. Employing a combination of these strategies significantly reduces the chances of becoming a victim of these malicious programs.
Role of Firewalls in Preventing Rootkit Infections
Firewalls act as a gatekeeper for network traffic, blocking unauthorized connections and preventing malicious software from entering your system. A properly configured firewall can prevent rootkits from communicating with malicious servers, thus significantly reducing the risk of infection. Configure your firewall to block unauthorized outgoing connections and monitor incoming connections.
Case Studies and Real-World Examples: Free Antivirus Download Roots Out Rootkits
Real-world cases demonstrate the effectiveness, and sometimes the limitations, of free antivirus software in combating rootkits. These instances highlight the importance of proactive security measures and the challenges involved in rootkit removal. While free solutions often provide a crucial first line of defense, they may not always offer the depth of analysis or the advanced features of paid counterparts.The effectiveness of a free antivirus program in removing a rootkit depends significantly on the sophistication of the rootkit itself.
Simple rootkits might be easily detected and removed, while more advanced ones might require specialized tools or a deeper understanding of the system’s architecture. Successful removal often involves a combination of detection, quarantine, and remediation steps.
Successful Rootkit Removal with Free Antivirus
Free antivirus software frequently plays a vital role in detecting and removing rootkits, even if the rootkit’s infection process is sophisticated. This effectiveness hinges on the quality of the software’s scanning engine and its ability to identify suspicious system modifications.
- Many free antivirus programs utilize heuristic analysis, which involves examining program behavior rather than just signatures. This can help detect rootkits that haven’t been previously encountered or those that have modified their code to evade detection by signature-based methods. This capability is crucial in a rapidly evolving threat landscape.
- Some free antivirus solutions employ sandboxing techniques to isolate and analyze potentially malicious processes. This allows for the detection of rootkit activity that might not be apparent through traditional scanning methods.
- The free antivirus program may flag unusual system modifications or changes in file access permissions, which could be indicative of a rootkit infection. These alerts provide users with the opportunity to investigate and potentially remove the rootkit.
User Experiences with Rootkit Infections and Free Antivirus
User experiences with rootkit infections often involve a gradual deterioration of system performance or unexpected behavior. This deterioration is sometimes subtle, making it challenging to pinpoint the source of the issue.
- A user experiencing intermittent network connectivity problems, or unexplained slowdowns in application performance, might suspect a rootkit infection. The free antivirus program, upon scanning, might detect and remove the rootkit, restoring normal system functionality.
- In cases where a rootkit has modified system files or drivers, the free antivirus program’s detection engine might identify the changes and prompt the user to restore the affected files from a backup or through a system recovery process.
- A user might encounter a situation where the free antivirus program identifies and removes a rootkit, enabling them to regain control of their system and access critical data.
Challenges in Rootkit Removal and the Role of Free Antivirus
Rootkit removal can be challenging due to the rootkit’s stealthy nature and its ability to modify system files and processes. Free antivirus solutions often face limitations in handling these sophisticated threats.
- Rootkits often employ techniques to hide themselves from detection. This necessitates sophisticated detection methods and constant updates to antivirus databases to identify the ever-evolving rootkit signatures.
- Some rootkits can modify the system’s kernel or core components, making them extremely difficult to remove without specialized tools or knowledge. Free antivirus programs may be less effective in dealing with such sophisticated attacks.
- The limited resources of free antivirus programs compared to their paid counterparts can impact their ability to perform thorough scans or offer advanced features for rootkit remediation.
Specific Examples of Rootkit Detection and Removal
While precise details of specific cases are often not publicly available, numerous reports detail instances where free antivirus software identified and removed rootkits. These examples showcase the ability of these programs to detect malicious activities and provide a level of protection against sophisticated threats.
- A free antivirus program might detect a rootkit that was attempting to establish a covert communication channel with a remote server. This detection allows the user to take immediate action to prevent further damage.
- A free antivirus program might detect and remove a rootkit that had modified critical system files. This detection would allow the user to restore the affected files and prevent potential data loss.
Last Point
In conclusion, free antivirus downloads offer a powerful tool for protecting your digital assets against rootkits and other malware. While free solutions might have limitations, they provide a valuable first line of defense. By understanding the intricacies of rootkit infections and the methods used by free antivirus programs to detect and remove them, you can significantly enhance your online security.
Regular updates, careful file handling, and a strong understanding of your system are crucial components of a comprehensive security plan.