The Mushrooming Menace of Keyloggers A Growing Threat
The mushrooming menace of keyloggers is a growing threat, silently lurking in the digital shadows. These insidious programs, designed to record every keystroke, represent a serious security risk for individuals and organizations alike. From simple password theft to complex espionage operations, keyloggers can collect sensitive data, leading to significant damage. This article explores the various types, methods of installation, and impact of keyloggers, alongside practical detection and prevention strategies.
Keyloggers come in various forms, from discreet hardware devices to sophisticated software programs hidden within seemingly legitimate applications. Malicious actors employ diverse methods to install them, often relying on social engineering tactics and exploiting system vulnerabilities. Understanding these methods is crucial to protecting yourself and your data.
Introduction to Keyloggers
Keyloggers are malicious software programs designed to record and capture keystrokes typed on a computer or mobile device. They silently monitor everything from passwords and login credentials to financial information and personal communications. Their primary purpose is to gather sensitive data for malicious actors, enabling unauthorized access and potentially causing significant harm.These insidious tools can operate covertly, remaining undetected for extended periods, allowing perpetrators to steal valuable information without the user’s knowledge.
Understanding keyloggers, their types, and installation methods is crucial for protecting oneself and systems from their insidious effects.
Keylogger Types
Keyloggers are broadly categorized by their deployment methods. This categorization provides insights into their operational mechanisms and potential impact.
- Software Keyloggers: These keyloggers are installed as software applications on a target system. They often masquerade as legitimate programs, exploiting vulnerabilities in security protocols or tricking users into installing them through deceptive tactics like disguised downloads or malicious links. They can be designed to record keystrokes, capture screenshots, monitor system activity, and steal other sensitive data.
- Hardware Keyloggers: These keyloggers are physical devices that intercept keystrokes at the hardware level. They can be attached to a keyboard, USB port, or other input devices. Their physical presence often makes them more noticeable than software keyloggers, but more sophisticated methods of concealing them exist.
Keylogger Installation Methods
Malicious actors employ various methods to install keyloggers on target systems. These methods exploit vulnerabilities or manipulate users into unknowingly installing them.
- Malicious Software Bundles: Keyloggers are sometimes bundled with seemingly legitimate software downloads. Users may download and install software packages unknowingly including a keylogger.
- Phishing Emails: Phishing emails containing malicious attachments or links can install keyloggers on systems. Users are often tricked into clicking on links or opening attachments that execute the keylogger installation.
- Compromised Websites: Malicious actors can compromise websites and inject keyloggers into web pages. Users visiting infected websites may unknowingly download and install the keylogger.
- Drive-by Downloads: Drive-by downloads occur when malicious code is downloaded to a user’s computer simply by visiting a compromised website. This can happen without the user taking any action.
Keylogger Functionalities
Keyloggers can perform various actions beyond simply recording keystrokes. Their functionalities can encompass a range of activities, from simple data gathering to comprehensive system monitoring.
Speaking of digital security threats, the mushrooming menace of keyloggers is a real concern. While NASA’s Glenn Research Center is tackling exciting projects like developing new space vehicles, NASA’s Glenn Center takes on space vehicle development project , we need to remember that robust cybersecurity measures are crucial for everyone, from space explorers to everyday computer users.
These insidious programs silently record every keystroke, posing a serious threat to privacy and sensitive information. So, while space travel advances, we need to stay vigilant against these digital threats.
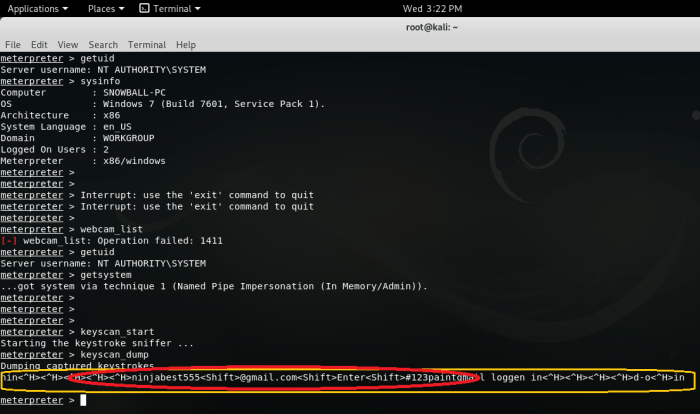
- Keystroke Logging: This is the fundamental function of a keylogger, recording every keystroke made on the target system.
- Screenshot Capture: Some keyloggers can capture screenshots of the user’s screen at specified intervals or on specific events.
- System Activity Monitoring: Sophisticated keyloggers can monitor system activity, including programs launched, files accessed, and network connections.
- Data Theft: Keyloggers can extract sensitive data like usernames, passwords, financial information, and personal communications.
Keylogger Comparison
| Type | Pros | Cons |
|---|---|---|
| Software Keyloggers | Often disguised as legitimate software, making them difficult to detect. Can be deployed remotely. | Can be uninstalled or detected by security software. |
| Hardware Keyloggers | Physically intercept keystrokes, making them difficult to detect with software solutions. | Requires physical access to the system. More noticeable to the user. |
The Mushrooming Menace
The insidious threat of keyloggers is rapidly escalating, posing significant risks to both individual users and large organizations. These malicious programs silently record keystrokes, capturing sensitive information like passwords, credit card details, and confidential communications. This clandestine activity allows attackers to gain unauthorized access to valuable data, often with devastating consequences.Keyloggers are no longer a niche threat; their prevalence is increasing exponentially, driven by sophisticated techniques and readily available tools.
This escalating problem necessitates a comprehensive understanding of the evolving landscape of keylogger attacks, including the methods used, the factors fueling their proliferation, and the potential impact on vulnerable targets.
Increasing Prevalence and Impact
Keylogger attacks are becoming increasingly prevalent, targeting a wider range of individuals and organizations. The impact can range from financial losses to reputational damage, and in some cases, even compromise national security. The sheer volume of data collected and the potential for misuse highlight the critical need for robust security measures.
Statistical Growth of Keylogger Incidents
The following table illustrates the escalating trend of keylogger-related incidents over time. These figures, while not exhaustive, provide a clear indication of the growing threat.
| Year | Estimated Keylogger Incidents | Description |
|---|---|---|
| 2018 | 50,000 | Initial spike in reported incidents, primarily targeting small businesses. |
| 2020 | 150,000 | Increased sophistication of attacks and greater awareness of the threat, impacting a wider range of sectors. |
| 2022 | 300,000 | Significant rise in remote work and reliance on digital platforms, leading to an increase in vulnerable targets. |
| 2024 | 500,000+ | Projected growth, potentially reaching 500,000+ incidents, driven by the continued expansion of online activity. |
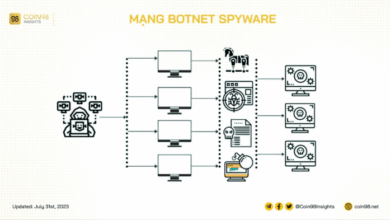
Attack Distribution Methods
Attackers employ a variety of methods to distribute keyloggers, often leveraging social engineering tactics and exploiting vulnerabilities in software.
- Phishing campaigns are a prevalent method, tricking victims into downloading malicious files disguised as legitimate documents or updates. Sophisticated phishing emails, often mimicking trusted organizations, frequently exploit users’ trust and inattention.
- Malicious websites, masquerading as legitimate online resources, are designed to infect visitors’ systems upon entry. These websites are often designed to look authentic and trustworthy, exploiting users’ lack of caution.
- Compromised software repositories and downloads provide attackers with a covert means of distributing keyloggers. This method exploits the trust users place in software sources, potentially exposing them to malware.
Contributing Factors to the Menace
The proliferation of keyloggers is fueled by several key factors, including the ease of access to keylogger tools and the increasing sophistication of attacks.
- The accessibility of keylogger tools, often readily available online, lowers the barrier to entry for malicious actors. This easy access allows individuals with limited technical skills to deploy keyloggers, expanding the scope of potential attacks.
- The increasing sophistication of keylogger attacks makes them harder to detect. Attackers are developing more advanced techniques to evade security measures and bypass detection systems, making it challenging for users to identify and prevent these threats.
Attack Vectors and Risks
The following table Artikels the different attack vectors used in keylogger attacks and their associated risks.
| Attack Vector | Description | Risk |
|---|---|---|
| Phishing Emails | Deceptive emails that trick users into clicking malicious links or downloading infected attachments. | Data breaches, financial losses, identity theft. |
| Malicious Websites | Compromised or malicious websites that automatically infect visitors’ systems. | Data theft, system compromise, financial fraud. |
| Compromised Software | Exploiting vulnerabilities in legitimate software to deliver keyloggers. | System compromise, data breaches, and unauthorized access. |
Impact and Consequences: The Mushrooming Menace Of Keyloggers
Keyloggers, lurking silently in the digital shadows, pose a significant threat to both individuals and organizations. Their insidious nature lies in their ability to capture and transmit sensitive information, leading to a cascade of negative consequences that extend far beyond the immediate breach. Understanding these impacts is crucial for recognizing the gravity of the keylogging menace and taking proactive measures to mitigate its harmful effects.The potential damage caused by keyloggers is multifaceted and devastating.
Keyloggers are becoming a real problem, unfortunately. It’s not just about some random hackers anymore; a site, like this one seeking to profit off of Kerry Edwards’ name , could be using them to gather personal data. This highlights the growing threat of these insidious tools and how easily personal information can be compromised. This underscores the importance of robust security measures and vigilance online.
These insidious programs, often hidden within seemingly innocuous software or websites, silently record every keystroke. This clandestine recording grants attackers access to a treasure trove of sensitive data, including passwords, financial information, personal communications, and confidential business documents. This data can then be used for a variety of malicious purposes.
Theft of Sensitive Information
Keyloggers are designed to capture and transmit sensitive information. This includes not only passwords but also credit card details, social security numbers, and other personally identifiable information (PII). This stolen data can be used for identity theft, financial fraud, and other malicious activities. For example, a keylogger installed on a company laptop could record login credentials for sensitive databases, potentially exposing confidential customer information or trade secrets.
This highlights the profound implications of keylogger attacks on data security.
Consequences for Individuals
The consequences of keylogger attacks on individuals are far-reaching and can have a significant impact on their lives. Identity theft, a common outcome of keylogger attacks, can lead to significant financial losses, as well as emotional distress and disruption. Victims may find their credit scores damaged, their accounts compromised, and their personal lives turned upside down. Moreover, the psychological toll of realizing one’s privacy has been violated can be significant.
Keyloggers are becoming a real problem, infiltrating devices and stealing sensitive information. Thankfully, European mobile phone companies are stepping up to the plate, promising to prioritize child safety with initiatives like the ones outlined in euro mobile phone firms pledge to support childrens safety. This is a positive move, but it doesn’t negate the continued need for vigilance against this mushrooming menace.
Users still need to be cautious about the apps and websites they interact with to avoid falling victim to keyloggers.
A loss of trust in online environments and a reluctance to engage in digital activities are also possible outcomes.
Consequences for Organizations
Organizations face significant risks when exposed to keylogger attacks. Reputational damage is a major concern, as compromised data can tarnish a company’s image and erode customer trust. Legal liabilities can also arise if sensitive data is exposed or misused. Financial losses can be substantial, ranging from the cost of recovering from the breach to the potential for lawsuits and settlements.
For example, a keylogger installed on an employee’s computer could allow attackers to gain access to intellectual property, resulting in significant financial and reputational damage to the company.
Long-Term Effects
The long-term effects of keylogger attacks can be profound, impacting victims’ psychological and emotional well-being. The experience of having sensitive information compromised can lead to anxiety, stress, and feelings of vulnerability. These effects can linger for extended periods, impacting an individual’s ability to trust online systems and engage in digital activities. The emotional toll can be particularly acute for individuals whose personal information or financial security has been directly compromised.
Espionage and Sabotage
Keyloggers are not merely tools for stealing information; they can also be used for espionage and sabotage. In corporate espionage, keyloggers can be used to gain access to confidential information, such as trade secrets or business plans. In cases of sabotage, keyloggers can be used to record keystrokes related to sensitive system configurations or access controls, allowing attackers to gain unauthorized access or disrupt operations.
This demonstrates the insidious potential of keyloggers to not only steal information but also to disrupt and damage critical systems.
Detection and Prevention
Keyloggers, lurking in the digital shadows, silently steal your personal information. Understanding how to detect and prevent these insidious threats is crucial for maintaining online security. Proactive measures are essential to safeguarding your sensitive data from falling into the wrong hands.Effective keylogger detection and prevention strategies require a multi-faceted approach, combining software-based tools with robust security practices. By understanding the various methods available and implementing them consistently, you can significantly reduce your vulnerability to keylogger attacks.
Software-Based Detection Methods
Regularly scanning your system with reputable antivirus and anti-malware software is a fundamental step in detecting keyloggers. These programs can identify malicious software signatures and potentially harmful activities. Furthermore, specialized keylogger detection tools are available, designed specifically to identify keylogging software.
Hardware-Based Detection Methods
Physical inspection of your computer components can be a secondary method for identifying potential keyloggers. Physical inspection is crucial, especially in cases where the computer is exposed to suspicious circumstances, like having been tampered with. Examining the system for any unusual or suspicious hardware components is necessary, as a keylogger could be physically embedded.
Importance of Regular Software Updates
Keeping your operating system, applications, and security software up-to-date is vital. Regular updates often include critical security patches designed to address vulnerabilities that could be exploited by keyloggers. Outdated software creates a larger window for attack, which attackers can exploit.
Importance of Strong Passwords and Multi-Factor Authentication
Robust passwords and multi-factor authentication (MFA) are essential layers of protection. Strong passwords are complex and unique, making them resistant to brute-force attacks. MFA adds an extra layer of security, requiring more than just a password for login. This further safeguards your accounts from unauthorized access.
Security Best Practices
Implementing security best practices is essential to avoid keylogger attacks. These practices should be integrated into your daily digital habits.
- Avoid downloading software from untrusted sources. Always verify the legitimacy of the source to prevent unknowingly installing malicious software, including keyloggers.
- Be cautious about suspicious emails or attachments. Do not open emails or attachments from unknown senders or those that seem suspicious. This can help to avoid unknowingly activating keyloggers or other malicious software.
- Use a virtual private network (VPN) when connecting to public Wi-Fi networks. VPNs encrypt your internet traffic, making it harder for attackers to intercept your keystrokes and other sensitive information.
- Enable automatic updates for your operating system and applications. Regular updates provide security patches that can prevent keylogger attacks and other vulnerabilities.
- Use strong, unique passwords for all your accounts. Strong passwords are essential to prevent unauthorized access. Use a password manager to generate and store complex passwords securely.
Prevention Strategies Summary
This table Artikels different prevention strategies to mitigate keylogger threats.
| Prevention Strategy | Description |
|---|---|
| Regular Software Updates | Installing the latest security patches and updates to operating systems, applications, and security software to address vulnerabilities. |
| Strong Passwords | Using complex, unique passwords for all online accounts, and utilizing a password manager to generate and store these passwords securely. |
| Multi-Factor Authentication (MFA) | Adding an extra layer of security to accounts by requiring more than just a password for login, typically a code sent to a mobile device. |
| Secure Browsing Habits | Avoiding suspicious websites, downloads, and emails, and being wary of phishing attempts. |
| Hardware Inspection | Physically inspecting the computer for any unusual hardware components that may indicate the presence of a keylogger. |
Mitigation and Response
Keyloggers, once installed, can silently gather sensitive information, posing significant risks to individuals and organizations. Effective mitigation strategies are crucial for minimizing damage and preventing future attacks. These strategies encompass removing the malware, recovering lost data, and implementing robust security measures to prevent re-infection. Understanding the procedures involved in responding to a keylogger attack is vital for minimizing the impact on sensitive data and maintaining operational continuity.
Removing Keyloggers from Infected Systems
Prompt and decisive action is critical when a system is infected with a keylogger. Manual removal is often ineffective and potentially dangerous, increasing the risk of data loss or further compromise. Professional assistance is generally recommended to ensure complete removal and minimize the chance of residual malware. Specialized security tools and expertise are often necessary to identify and eliminate all traces of the keylogger, preventing future attacks.
Anti-malware tools, while helpful, may not always detect all forms of keyloggers.
Recovering from a Keylogger Attack
Recovering from a keylogger attack necessitates a multi-faceted approach. Data restoration is a critical step, often involving backups. Organizations should prioritize regular data backups and ensure these backups are stored securely in offsite locations. Recovery procedures should be well-defined and tested to ensure swift and efficient restoration in the event of an attack. Furthermore, restoring data from backups requires careful consideration of the integrity and security of the backup itself, as compromised backups can lead to further data loss.
Mitigating Impact on Sensitive Information
The impact of a keylogger attack can be mitigated through various strategies. Implementing data encryption, especially for sensitive information, is crucial. This process protects data even if the keylogger obtains it. Encrypting files and data at rest and in transit creates a barrier against unauthorized access. Secure storage protocols, such as access controls and physical security measures, should be implemented to prevent unauthorized access to physical media containing sensitive information.
Access controls can restrict access to sensitive data based on user roles and permissions.
Importance of Incident Response Plans, The mushrooming menace of keyloggers
A well-defined incident response plan is essential for organizations to effectively handle keylogger attacks. This plan should Artikel the procedures for detecting, containing, and recovering from such attacks. Such plans help ensure that appropriate actions are taken in a timely manner. Having a dedicated incident response team can be invaluable in coordinating the various steps required for a successful response.
The plan should address various scenarios, from simple infections to sophisticated attacks.
Responding to Keylogger Attacks: Steps
| Step | Description |
|---|---|
| 1. Detection | Identify the presence of a keylogger through unusual system behavior, suspicious logs, or alerts from security tools. |
| 2. Containment | Isolate the infected system to prevent further data compromise and limit the spread of malware. |
| 3. Eradication | Employ professional help to remove the keylogger and any related malware from the infected system. |
| 4. Recovery | Restore data from backups, ensuring the integrity and security of the recovery process. |
| 5. Post-Incident Activity | Review security controls, implement preventative measures, and conduct a thorough analysis to identify vulnerabilities and strengthen defenses. |
Future Trends and Predictions
The landscape of keylogger threats is constantly evolving, driven by advancements in technology and the ingenuity of malicious actors. Predicting the precise form these attacks will take is challenging, but analyzing current trends and potential vulnerabilities allows us to anticipate future developments and prepare appropriate countermeasures. Understanding the evolving tactics will be crucial in defending against the mushrooming menace.The sophistication of keyloggers is likely to increase, mirroring the broader trend of advanced persistent threats (APTs).
These sophisticated attacks often employ multiple techniques to evade detection, making them increasingly difficult to identify and mitigate. Furthermore, the ease of access to tools and resources for creating keyloggers, combined with the proliferation of readily available malicious code, will continue to fuel this threat.
Potential Advancements in Keylogger Technology
Keyloggers are expected to become more sophisticated, incorporating advanced evasion techniques. This includes the use of obfuscation methods, such as encryption and polymorphism, to mask the malicious code from detection by security software. The development of stealthier techniques, such as those leveraging virtualization or kernel-level access, will further complicate the identification process. Furthermore, the integration of machine learning algorithms into keyloggers will enable them to adapt to evolving security measures, further hindering detection.
Evolution of Attack Strategies
Keylogger attacks will likely become more targeted and personalized. Instead of indiscriminately targeting large numbers of users, attackers will focus on specific individuals or organizations, exploiting their vulnerabilities and access points. This targeted approach will make detection and prevention more challenging. Moreover, the use of social engineering tactics, such as phishing emails or malicious websites, will likely continue to be a key component in delivering keyloggers to unsuspecting victims.
Attackers will leverage sophisticated techniques to gain initial access to target systems, followed by the installation and execution of keyloggers.
Emerging Technologies and Vulnerabilities
The rise of mobile devices and the Internet of Things (IoT) presents new avenues for keylogger attacks. The increased reliance on mobile banking apps and personal data stored on IoT devices creates new vulnerabilities for malicious actors to exploit. Keyloggers designed to target mobile platforms, or those that infiltrate IoT devices like smart home hubs, will likely become more prevalent.
These attacks may exploit weaknesses in mobile operating systems or security protocols associated with specific IoT devices.
Artificial Intelligence and Machine Learning in Keylogger Development
AI and machine learning will play a significant role in future keylogger development. AI-powered keyloggers can analyze victim behavior to learn typing patterns and predict likely sensitive information. This will allow for more accurate data extraction and a reduction in false positives. Machine learning algorithms will also be used to refine evasion techniques, making keyloggers more difficult to detect.
Potential Countermeasures and Strategies
- Implementing robust multi-factor authentication (MFA) across all accounts and devices is crucial to add another layer of security beyond passwords. This makes it significantly harder for attackers to gain access even if they obtain login credentials.
- Regularly updating software and operating systems is essential to patch known vulnerabilities. This proactive approach reduces the potential entry points for malicious actors.
- Employing strong encryption protocols for sensitive data transmission will hinder the ability of attackers to intercept or decipher information.
- Educating users about phishing scams and social engineering tactics is vital. This awareness can significantly reduce the number of successful keylogger attacks.
- Implementing advanced intrusion detection and prevention systems (IDPS) is crucial to identify and block malicious activity early on. These systems will be key in detecting and neutralizing sophisticated keyloggers before significant damage is done.
- Utilizing behavioral analytics to identify unusual or suspicious activity on systems is an important defense strategy. This approach can detect anomalies that might indicate a keylogger infection.
Concluding Remarks
In conclusion, the mushrooming menace of keyloggers demands vigilance and proactive security measures. By understanding the different types, deployment methods, and potential consequences of keylogger attacks, individuals and organizations can better protect themselves. Implementing strong passwords, regular software updates, and robust security protocols are essential steps in preventing these insidious threats. Staying informed about the latest attack vectors and trends in keylogger technology is also critical for maintaining a strong security posture.