Are Data Leaks Bleeding Your Company Dry?
Are data leaks bleeding your company dry? This isn’t just a theoretical concern; it’s a stark reality for businesses across all sectors. From accidental mishaps to malicious attacks, data breaches can have devastating consequences, impacting not only finances but also operational efficiency and reputation. This exploration dives deep into the multifaceted impact of data leaks, examining the financial and operational costs, the best preventative measures, and crucial steps for effective response strategies.
We’ll uncover the different types of data leaks, from accidental to malicious, and delve into the specific challenges faced by various industries, like finance and healthcare. Understanding the stages of a data breach, from initial compromise to recovery, is vital to developing robust defense mechanisms. We’ll also provide actionable strategies to mitigate risks and Artikel the crucial steps in a comprehensive data security plan.
Understanding Data Leaks: Are Data Leaks Bleeding Your Company Dry

Data breaches are a pervasive threat in today’s interconnected world. They can cripple organizations, erode trust, and cause significant financial and reputational damage. Understanding the various facets of data leaks, from their causes to their consequences, is crucial for developing effective prevention and mitigation strategies. This exploration delves into the complexities of data breaches, examining their types, impact, and detection methods.Data leaks, often referred to as data breaches, encompass any unauthorized access, use, disclosure, disruption, modification, or destruction of sensitive information.
They can have far-reaching consequences, impacting everything from individual privacy to national security. The following sections provide a deeper understanding of these vulnerabilities.
Defining Data Leaks
Data leaks are characterized by the unauthorized disclosure of sensitive data. These incidents can be categorized into several types, each with its own set of contributing factors. Accidental leaks often stem from human error, such as misconfigured systems or lost devices. Malicious leaks, on the other hand, are intentional acts of cybercriminals seeking financial gain or disruption.
Negligent leaks arise from failures to implement appropriate security measures.
Impact Across Industries
The consequences of data leaks vary significantly depending on the industry and the nature of the compromised data. In the finance sector, breaches can lead to fraudulent transactions and financial losses. Healthcare organizations face the risk of patient identity theft and compromised medical records, with potentially severe implications for patient well-being. Retailers, when targeted, may experience identity theft and fraud, impacting customer trust and potentially damaging their brand reputation.
Are data leaks really bleeding your company dry? It’s a serious concern, and the sheer scale of investments in infrastructure like Sprint’s recent $3 billion plunge into upgrading its wireless network ( sprint sinks 3 billion into wireless network ) highlights the need for robust security measures. While companies pour billions into new tech, neglecting the crucial defense against data breaches leaves them vulnerable.
This massive investment in network upgrades begs the question: are companies prioritizing the right kind of security? The answer is, likely not.
These examples underscore the need for tailored security measures within specific industries.
Stages of a Data Breach
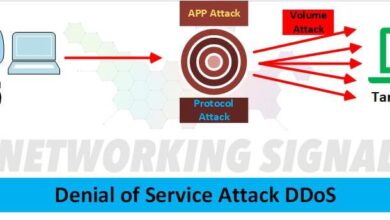
Data breaches typically progress through several stages. The initial compromise involves the exploitation of vulnerabilities, such as weak passwords or unpatched software. The subsequent stage involves the exfiltration of data, where attackers gain access to and copy sensitive information. Following this, the attackers may attempt to use the compromised data for malicious purposes, including financial fraud or identity theft.
Finally, the recovery phase involves damage control, investigation, and implementation of preventative measures.
Methods for Detecting Data Leaks
Regular security audits, intrusion detection systems, and data loss prevention tools are crucial for identifying potential vulnerabilities and preventing data breaches. Monitoring user activity for suspicious patterns and implementing strong access controls can also significantly reduce the risk. Furthermore, employing security information and event management (SIEM) systems can help organizations proactively detect anomalies and potential threats. A layered approach to security is critical for effective data leak detection.
Severity Levels of Data Breaches
The severity of a data breach is determined by factors such as the type and amount of data compromised, the number of affected individuals, and the potential for harm. A comprehensive assessment considers the financial and reputational impact, as well as the legal and regulatory implications.
| Severity Level | Description | Consequences |
|---|---|---|
| Low | Limited data exposure, minimal impact | Minor financial losses, limited reputational damage |
| Medium | Significant data exposure, moderate impact | Potential financial losses, moderate reputational damage, regulatory fines |
| High | Widespread data exposure, significant impact | Large financial losses, severe reputational damage, legal repercussions |
Financial Impact of Data Leaks
Data breaches are no longer a theoretical threat; they are a significant financial burden for organizations of all sizes. The financial fallout extends far beyond the immediate cost of remediation. Understanding the multifaceted impact, both direct and indirect, is crucial for effective risk management and proactive security measures.The financial impact of data breaches encompasses a wide spectrum of costs, from immediate expenses to long-term consequences.
Direct losses, like fines and legal fees, are tangible and readily calculated. However, the intangible costs, including reputational damage and lost revenue, often significantly outweigh the direct financial losses.
Direct Financial Losses
Data breaches frequently lead to substantial direct financial losses. These losses encompass fines imposed by regulatory bodies for non-compliance with data protection laws, such as GDPR or CCPA. Legal costs associated with investigations, litigation, and settlements further compound the financial burden. Furthermore, the expenses related to incident response, including forensic analysis, data recovery, and notification of affected individuals, can quickly escalate.
The direct financial losses from data breaches can range from tens of thousands to millions of dollars, depending on the scale and nature of the breach.
Indirect Financial Losses
Beyond the direct costs, data breaches inflict significant indirect financial losses. Reputational damage can severely impact a company’s brand image and customer trust, leading to a decline in sales and market share. Lost revenue is another significant consequence, arising from reduced customer loyalty, decreased sales, and the need to invest in rebuilding trust. Customer churn, often a direct result of data breaches, further contributes to the financial losses.
Data breaches are a serious concern for any company. Are you losing valuable information that could be crippling your bottom line? It’s a sobering thought, and while the latest tech news, like Apple TV’s potential role in apple tv the new ipod hijacking the us elections ideas for dads and grads , might seem a world away, the reality is that any vulnerability, no matter how seemingly small, can have a huge impact on your business.
So, how can you protect yourself from data leaks and ensure your company isn’t bleeding dry? The answers might surprise you.
Impact on Market Valuation and Investor Confidence
Data breaches can have a detrimental effect on a company’s market valuation and investor confidence. Investors may perceive a data breach as an indicator of inadequate security practices, potentially leading to a decline in stock prices and reduced investor interest. Negative publicity surrounding a data breach can damage a company’s overall reputation, impacting future investment opportunities.
Calculating the Total Cost of a Data Breach
Calculating the total cost of a data breach requires a comprehensive approach that considers both direct and indirect losses. A formula for calculating the total cost may include direct costs such as fines, legal fees, and incident response costs. Indirect costs, such as lost revenue, reputational damage, and customer churn, are more challenging to quantify but crucial to incorporate.
A hypothetical company, “TechSolutions,” with a market capitalization of $1 billion, could face a significant financial impact if a data breach occurred. For example, a breach exposing 100,000 customer records might result in $5 million in direct costs and a further $10 million in indirect costs due to lost revenue and damaged reputation. The total cost could exceed $15 million.
Comparison of Financial Impacts by Data Type
| Data Type | Direct Costs | Indirect Costs | Overall Impact |
|---|---|---|---|
| Customer Data | Fines, legal fees, notification costs | Lost revenue, customer churn, reputational damage | Significant, potentially impacting long-term viability |
| Intellectual Property | Legal fees, loss of competitive advantage | Reduced innovation, lost market share | Potentially devastating, affecting core business functions |
The table illustrates the varying financial impact of different data types. Customer data breaches often lead to substantial direct costs, while intellectual property breaches can severely hinder a company’s competitive edge and long-term prospects.
Operational Impact of Data Leaks
Data breaches aren’t just about financial losses; they inflict significant operational damage, disrupting workflows, eroding trust, and demanding substantial resources for recovery. Understanding the operational fallout is crucial for effective incident response and prevention strategies. This often overlooked aspect of data breaches can be equally, if not more, devastating than the immediate financial consequences.The operational impact extends far beyond the initial breach itself, lingering as a persistent headache for affected organizations.
From the immediate shock of system downtime to the long-term effects on employee morale, the ripple effects are significant. Companies need a robust plan to navigate these challenges and emerge stronger on the other side.
System Downtime and IT Remediation Efforts
Data breaches frequently necessitate significant system downtime while IT teams investigate the breach, contain the damage, and implement security enhancements. This downtime can cripple operational processes, leading to lost productivity and revenue. The extent of downtime depends on the breach’s severity and the organization’s ability to respond effectively. For example, a breach targeting a critical e-commerce platform could result in complete website outages, impacting sales and customer relations.
Customer Notifications and Support Requests
Prompt and transparent communication with affected customers is paramount during a data breach. This includes issuing notifications, answering support queries, and providing resources to mitigate potential harm. Organizations need to establish clear procedures for handling these requests to maintain customer trust and avoid reputational damage. This necessitates a dedicated support team equipped to handle a surge in inquiries and providing personalized assistance.
Data and System Restoration
Restoring data and systems after a breach is a complex process that requires meticulous planning and execution. The recovery process must consider the integrity and security of the restored data and systems. This involves meticulous data recovery, system rebuilding, and implementing enhanced security measures to prevent future breaches. This may necessitate a complete system rebuild, potentially involving significant costs and time delays.
Careful planning and thorough documentation are critical for efficient restoration.
Impact on Employee Morale and Productivity
Data breaches can have a detrimental effect on employee morale and productivity. The uncertainty and stress surrounding a breach can lead to decreased motivation and engagement. Addressing the concerns of employees and providing support during the recovery process is crucial for maintaining a positive work environment. This includes clear communication, psychological support, and demonstrating that the company is committed to addressing the situation effectively.
Operational Challenges and Solutions
| Data Breach Scenario | Operational Challenges | Potential Solutions |
|---|---|---|
| Phishing Attack Targeting Employee Credentials | Potential system compromise, data exfiltration, loss of sensitive information, decreased employee productivity, increased support requests. | Implement multi-factor authentication, security awareness training for employees, robust incident response plan, investigation and containment procedures, and employee assistance programs. |
| Malware Infection Leading to Data Encryption | System downtime, inability to access critical data, potential ransom demands, significant financial loss. | Establish backup and recovery procedures, implement intrusion detection systems, secure backups offline, negotiation with ransomware operators (if applicable), and comprehensive data recovery plan. |
| Third-Party Vendor Data Breach | Potential exposure of customer data, reputational damage, potential legal liabilities, loss of customer trust. | Thorough vendor due diligence, contract review, data security audits, establishing clear breach response protocols, communication with affected parties, and appropriate legal counsel. |
Preventing Data Leaks

Data breaches are a significant threat to organizations of all sizes, and the financial and reputational damage can be catastrophic. Proactive measures to prevent data leaks are crucial for maintaining trust, safeguarding sensitive information, and avoiding costly consequences. Implementing robust security protocols is a continuous process requiring vigilance and adaptation to evolving threats.Effective data security is not just about installing the latest firewalls; it’s a holistic approach that encompasses both technical and procedural safeguards.
It requires a commitment from every employee, a clear understanding of roles and responsibilities, and a well-defined plan to address vulnerabilities. This proactive strategy not only prevents leaks but also builds a culture of security awareness within the organization.
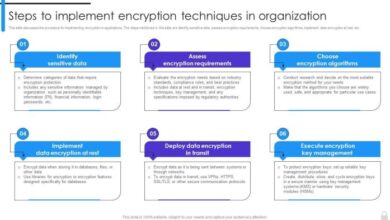
Data Security Best Practices
Data security best practices involve a multifaceted approach, combining technical controls and procedural measures. Implementing strong passwords, enabling multi-factor authentication, and regularly updating software are essential technical safeguards. Regular security audits and penetration testing help identify vulnerabilities before they can be exploited. Procedural measures, such as restricting access to sensitive data based on need-to-know, and implementing robust data loss prevention (DLP) policies, are equally important.
- Strong Password Management: Enforcing strong, unique passwords for all accounts is paramount. Implementing password managers and requiring complex passwords with a combination of uppercase and lowercase letters, numbers, and symbols helps to significantly improve security. Regular password resets and educating employees on best practices are crucial for maintaining robust password hygiene.
- Multi-Factor Authentication (MFA): Implementing MFA adds an extra layer of security by requiring multiple verification steps beyond a simple password. This significantly reduces the risk of unauthorized access, even if a password is compromised.
- Regular Software Updates: Keeping software and operating systems updated with the latest security patches is critical. These updates often address vulnerabilities that hackers can exploit. Automated patching systems can streamline this process and minimize downtime.
- Access Control Policies: Implement strict access control policies that limit access to sensitive data based on the principle of least privilege. This means only those who need access to specific data should have it. Regular reviews and updates to these policies are vital to ensure they remain effective.
Roles and Responsibilities
Defining clear roles and responsibilities within the organization is essential for effective data security. This involves designating individuals or teams responsible for different aspects of data security, such as data governance, security incident response, and compliance. Clear lines of communication and accountability are key.
- Data Owners: Data owners are responsible for the accuracy, completeness, and security of the data under their control. They understand the sensitivity of the data and the potential risks associated with its mishandling. They play a vital role in establishing data governance policies.
- Data Custodians: Data custodians are responsible for the day-to-day management and security of the data. They follow the policies established by data owners and ensure that data is stored and processed securely.
- Security Officers: Security officers are responsible for implementing and maintaining the organization’s overall security policies and procedures. They ensure that technical controls are in place and that procedures are followed. They are often involved in incident response and auditing activities.
Developing a Comprehensive Data Security Plan
A comprehensive data security plan is a roadmap for protecting sensitive data. It should Artikel specific strategies, procedures, and controls to prevent data breaches. It should include risk assessments, incident response plans, and regular security audits.
- Risk Assessment: Identify potential threats and vulnerabilities to data. This involves analyzing the likelihood and impact of various risks. This step informs the development of appropriate countermeasures.
- Incident Response Plan: Develop a plan for responding to security incidents. This should Artikel procedures for detecting, containing, and recovering from data breaches. This plan is crucial for minimizing the impact of a security incident.
- Regular Security Audits: Conduct regular security audits to identify and address vulnerabilities. This process ensures that security controls are functioning as intended and that the organization’s data security posture is continually evaluated and improved.
Employee Training and Awareness Programs
Employee training is a crucial component of a robust data security program. Educating employees about security threats and best practices can significantly reduce the risk of data breaches. Training should be ongoing and tailored to different roles and responsibilities.
- Security Awareness Training: Regular training programs that emphasize phishing scams, social engineering, and other common threats are essential. These programs help employees identify and avoid potential vulnerabilities.
- Role-Specific Training: Training should be tailored to the specific roles and responsibilities of employees. Data owners and custodians require different training compared to other staff members.
- Ongoing Reinforcement: Regular updates and reinforcement of security awareness programs are vital to maintain a culture of security awareness within the organization.
Creating and Implementing a Data Security Policy, Are data leaks bleeding your company dry
A flowchart can visually represent the steps involved in creating and implementing a data security policy. This visual representation helps to streamline the process and ensure that all necessary steps are taken. 
Responding to Data Leaks
A data breach is a serious event that can have devastating consequences for any organization. Beyond the reputational damage and financial losses, it can erode customer trust and expose sensitive information, potentially leading to legal repercussions. Effective response is crucial to mitigate the damage and restore confidence.Swift and well-coordinated action is paramount when a data leak is suspected or confirmed.
A meticulously planned response strategy, meticulously executed, can significantly reduce the long-term impact. This involves immediate containment, thorough investigation, and transparent communication with all affected parties.
Data leaks are a serious threat, potentially draining your company’s resources. While Microsoft is taking its time with the next service pack, this deliberate approach could ironically offer a window into bolstering your security. Ultimately, companies need to proactively address potential vulnerabilities to stop data leaks from becoming a major problem.
Immediate Response Steps
A rapid and well-defined response plan is essential to minimize damage. This involves several crucial steps.
- Confirmation and Containment: Immediately confirm the breach and implement containment strategies. This involves isolating affected systems to prevent further data exposure. A well-trained IT team will be crucial in securing the network and stopping the spread of the incident.
- Incident Reporting: Notify the relevant authorities and regulatory bodies. Timely notification is critical, often dictated by specific compliance regulations. Documentation of all communication is key.
- Security Assessment: Conduct a thorough assessment of the breach, identifying the scope and extent of the damage. This involves determining the type of data compromised, the number of affected individuals, and the potential impact on operations and finances.
Containing the Breach and Isolating Systems
Containing the breach and isolating affected systems is a crucial step to prevent further data exposure and maintain business continuity. This often involves shutting down compromised systems, implementing firewalls, and establishing secure access controls.
- System Isolation: Isolate affected systems from the network to prevent further data leakage or malware propagation. This involves disconnecting servers, workstations, or network segments involved in the breach.
- Firewall Implementation: Deploy firewalls to block unauthorized access to the compromised systems. This is a critical step in preventing the breach from escalating.
- Access Control Adjustments: Review and modify access controls to prevent unauthorized access to sensitive data. This may involve changing passwords, implementing multi-factor authentication, and reviewing user privileges.
Investigating the Cause of the Data Leak
Understanding the root cause of the data breach is vital for preventing future incidents. A comprehensive investigation is necessary to identify vulnerabilities, procedural flaws, or malicious actors.
- Forensic Analysis: Employ forensic analysis techniques to gather evidence, trace the source of the breach, and understand the attack methods. This involves reviewing logs, system files, and network traffic.
- Vulnerability Assessment: Conduct a vulnerability assessment to identify weaknesses in the organization’s security infrastructure. This can involve penetration testing, security audits, and automated vulnerability scans.
- Root Cause Analysis: Analyze the identified vulnerabilities to pinpoint the root cause of the data leak. Were there inadequate security protocols? Was there a lack of employee training? Understanding the underlying cause is critical for preventing future incidents.
Communicating with Affected Parties and Regulatory Bodies
Transparency and prompt communication are crucial during and after a data breach.
- Affected Parties: Inform affected individuals about the breach and their rights. This involves providing clear and concise information about the nature of the breach, the type of data compromised, and the steps being taken to mitigate the impact.
- Regulatory Bodies: Comply with all applicable data protection regulations and report the incident to the relevant authorities. This includes following reporting timelines and providing necessary documentation.
Managing the Aftermath of a Data Breach
The aftermath of a data breach is a complex process requiring careful management. A comprehensive plan is crucial to recover and rebuild trust.
- Crisis Management: Establish a crisis management team to coordinate responses to the incident. This involves assigning roles and responsibilities to ensure effective communication and action.
- Data Recovery: Implement a data recovery plan to restore compromised data and systems. This often involves backups, restoration procedures, and data recovery specialists.
- Preventative Measures: Implement necessary preventative measures to prevent future data breaches. This includes strengthening security protocols, improving employee training, and conducting regular security assessments.
Illustrative Examples
Data breaches are a harsh reality for businesses today. They’re not just theoretical threats; they happen frequently, inflicting significant damage on companies of all sizes. Understanding how real-world cases unfolded, and the responses implemented, can offer valuable lessons for proactive security measures. This section dives into specific examples, highlighting successful strategies and the importance of preparation.
Real-World Case Studies of Data Leaks
Numerous companies have experienced significant data breaches. These incidents often expose vulnerabilities, reveal the importance of robust security measures, and highlight the need for swift and effective response plans. Consider the Target breach of 2013, which compromised the personal information of millions of customers, causing substantial financial losses and reputational damage. This and other incidents demonstrate the potentially devastating consequences of inadequate security.
The 2017 Equifax breach, exposing sensitive data of over 147 million Americans, also served as a stark reminder of the importance of data protection.
Comparison of Successful Data Breach Response Strategies
Analyzing successful data breach response strategies reveals key factors contributing to a positive outcome. A crucial aspect is swift detection and containment. Companies that quickly identify the breach and contain its spread are better positioned to minimize damage. Effective communication with affected individuals and regulatory bodies is also essential. Transparency and proactive communication can mitigate negative public perception.
Finally, a thorough investigation into the cause of the breach and implementation of preventive measures are critical steps to avoid future incidents.
Proactive Security Measures to Mitigate Data Leaks
Implementing proactive security measures can significantly reduce the likelihood and impact of data leaks. These measures include robust access controls, regular security audits, and employee training on data security best practices. Regular security assessments, using tools like penetration testing, identify potential vulnerabilities and ensure systems are adequately secured. The importance of encryption for sensitive data cannot be overstated.
Implementing end-to-end encryption, particularly for data in transit and at rest, significantly enhances security.
The Importance of Data Breach Insurance
Data breach insurance is a critical financial safeguard for organizations facing the threat of a data breach. It can help cover the costs associated with notification requirements, legal fees, and regulatory fines. The insurance coverage often extends to reputational damage and lost revenue, which are significant factors following a breach. It can also help with incident response and forensic analysis, ensuring swift and professional handling of the situation.
Industry Best Practices in Handling Data Breaches
Following industry best practices is crucial in managing data breaches effectively.
“Establish a comprehensive data breach response plan, outlining procedures for detection, containment, notification, and recovery.”
This plan should include specific protocols for communication with affected parties, regulatory agencies, and the public.
“Conduct regular security assessments and penetration testing to identify vulnerabilities and proactively address potential risks.”
Regular security audits are critical to proactively identifying and fixing weaknesses in systems.
“Implement strong access controls and multi-factor authentication to limit unauthorized access to sensitive data.”
This practice strengthens security measures and helps protect sensitive information.
“Educate employees on data security best practices, including recognizing phishing attempts and handling sensitive information securely.”
Regular training on security awareness is crucial in preventing breaches caused by human error.
Closing Notes
In conclusion, data breaches are a significant threat to any organization, demanding a proactive and well-defined approach to security. By understanding the various facets of data leaks, from the initial impact to the long-term consequences, businesses can better equip themselves to protect their valuable assets. Implementing robust preventative measures, coupled with a swift and organized response strategy, is crucial for minimizing the damage and safeguarding your company’s future.