Microsofts Unix, Dells Linux Virus Warning – Infected, Fired
Microsofts unix dells linux and a virus warning get infected get fired – Microsoft’s Unix, Dell’s Linux, and a virus warning get infected, get fired. This post dives deep into the vulnerabilities of these systems, examining how viruses exploit weaknesses, the consequences of infections, and crucial security measures. From the impact of software vulnerabilities to employee responsibility, we’ll explore the entire spectrum of potential issues and solutions.
This comprehensive guide explores the interconnectedness of software, hardware, and human error in the face of a viral threat. We’ll examine case studies, best practices, and proactive strategies to mitigate risks and ensure data safety. We’ll also analyze employee responsibility and potential consequences for security breaches.
Impact of Software Vulnerabilities
Software vulnerabilities, present in all types of systems, are a constant threat to security. These weaknesses can be exploited by malicious actors, potentially leading to severe consequences. Understanding how these vulnerabilities manifest and how they can be exploited is crucial for protecting sensitive data and systems. Microsoft’s Unix-based systems, Dell’s Linux-based systems, and all software have varying degrees of vulnerability, and the methods of exploitation can differ greatly.Vulnerabilities in software allow malicious code, often in the form of viruses, to gain unauthorized access to systems.
This access can be used for a variety of malicious purposes, including data theft, system disruption, and the installation of further malware. The impact of such an attack can range from minor inconveniences to catastrophic system failures, affecting businesses and individuals alike. Understanding the potential consequences is essential for effective security measures.
Exploitation Methods
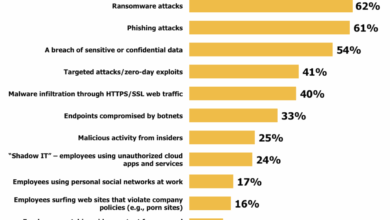
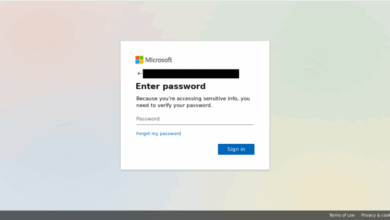
Malicious actors utilize various techniques to exploit vulnerabilities. These range from exploiting known weaknesses in software libraries to crafting sophisticated attacks targeting specific configurations or user behavior. Social engineering, phishing scams, and malware disguised as legitimate software are common methods employed. A critical element is the ability of viruses to adapt to defenses, constantly evolving to bypass security measures.
Potential Damage
The consequences of a successful attack can be significant. Data breaches can expose sensitive information, leading to financial losses, reputational damage, and legal liabilities. System disruptions can cause downtime, impacting productivity and operations. The introduction of further malware can lead to the ongoing compromise of the system, allowing attackers to maintain control for extended periods. Financial losses, legal penalties, and long-term damage to an organization are potential results.
Operating System Susceptibility
Different operating systems have varying levels of susceptibility to different types of viruses. This susceptibility is influenced by the design, implementation, and security measures built into the system. It’s not just about the operating system itself, but also the specific software and applications running on top of it. This makes a precise comparison complex.
| Operating System | Susceptibility to Virus Types |
|---|---|
| Microsoft Unix-based Systems | Generally susceptible to viruses targeting Unix vulnerabilities, but security patches and updates can significantly reduce risk. The specific implementation of Unix within Microsoft’s ecosystem plays a role. |
| Dell Linux-based Systems | Linux systems, in general, have a strong reputation for security. However, vulnerabilities can exist in specific applications or configurations. The specific Linux distribution (e.g., Ubuntu, Fedora) and the packages installed will affect susceptibility. |
| Other Systems (e.g., macOS) | Each operating system has its own unique vulnerabilities and security protocols. Susceptibility depends on the specific implementation and the use of security measures. |
Consequences of Infections: Microsofts Unix Dells Linux And A Virus Warning Get Infected Get Fired
A virus infection can have devastating consequences, impacting not only individual users but also businesses and entire industries. The repercussions can extend beyond simple data loss, reaching into legal, financial, and reputational realms. Understanding these consequences is crucial for implementing proactive security measures.Understanding the various repercussions of a virus infection is essential for building a robust security posture.
This includes recognizing the multifaceted nature of the damage, ranging from the direct impact on data to the far-reaching consequences on a company’s reputation and financial stability.
Data Security Risks
Virus infections compromise data integrity and confidentiality. Malicious software can steal sensitive information, encrypt valuable data, or delete critical files, leading to significant losses. For example, a ransomware attack can encrypt critical business files, rendering them inaccessible until a ransom is paid. This not only disrupts operations but also jeopardizes the security of customer data.
Business Operations Disruption
Virus infections can severely disrupt business operations. Systems may crash, services may be unavailable, and productivity can plummet. The downtime caused by a virus outbreak can lead to significant financial losses, especially for businesses relying heavily on technology for their daily operations. For instance, a manufacturing plant experiencing a virus infection could halt production lines, resulting in lost revenue and potential damage to the supply chain.
Individual User Impact
Individual users face various risks when infected with a virus. Personal data can be compromised, leading to identity theft or financial fraud. Moreover, viruses can damage personal devices, making them unusable. For example, a virus infection could lead to the theft of financial information from a personal computer, potentially resulting in significant financial losses for the victim.
Legal Ramifications
Virus infections can lead to legal repercussions, especially when sensitive data is compromised. Companies may face lawsuits from affected individuals or customers, leading to significant legal costs. Depending on the type of data compromised and the jurisdiction, legal penalties could be substantial. Data breaches related to healthcare records or financial information can trigger significant fines and legal battles.
Financial Ramifications
The financial impact of a virus infection can be substantial. Costs include remediation efforts, legal fees, lost revenue, and potential fines. The financial burden can be particularly heavy for smaller businesses, potentially leading to closure. For example, a small retail business affected by a ransomware attack could face significant financial losses due to downtime, ransom payments, and legal fees.
Reputational Damage
A virus outbreak can severely damage a company’s reputation and erode customer trust. Customers may lose confidence in the organization’s ability to protect their data, potentially leading to a loss of customers and revenue. A well-publicized data breach can damage a company’s image, making it difficult to attract and retain clients in the future. For instance, a major retailer experiencing a data breach could see a significant drop in customer loyalty and sales.
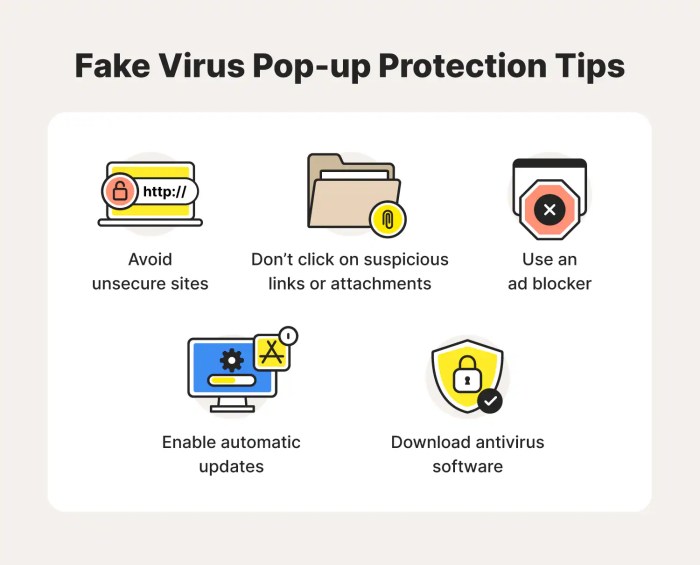
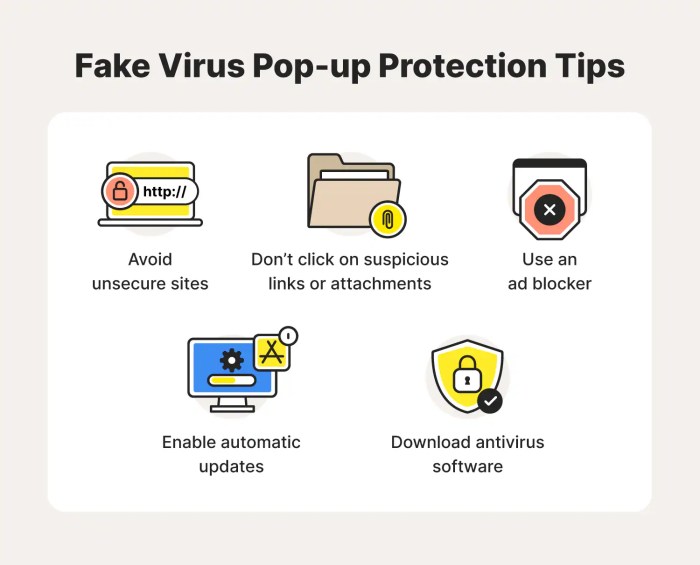
Proactive Measures for Prevention
Implementing robust security measures is critical to prevent virus infections. These include regularly updating software, using strong passwords, and practicing safe browsing habits. Regular security awareness training for employees is also crucial to prevent human error. A comprehensive security strategy should include multiple layers of defense, from strong passwords to robust antivirus software.
Security Measures
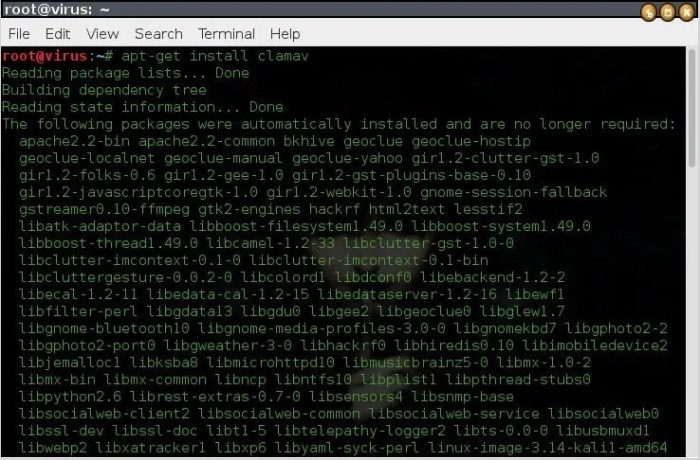
Protecting software systems from vulnerabilities is crucial in today’s digital landscape. A comprehensive security strategy must encompass proactive measures to prevent infections and minimize the impact of potential breaches. This involves understanding the unique security needs of diverse operating systems, such as Microsoft’s Unix-like systems, Dell’s Linux distributions, and other software platforms. Ignoring security precautions can lead to significant financial losses, reputational damage, and legal liabilities.A robust security plan goes beyond simple reactive measures like antivirus software.
So, Microsoft’s Unix, Dell’s Linux, and a virus warning – it’s all getting infected and people are getting fired, right? It’s a pretty serious situation, and it highlights the growing role of advertisers in the tech world. Check out this fascinating look at how advertisers are stepping up their game, literally, here. But in the end, the security breaches and resulting job losses are still a major concern for everyone, aren’t they?
It necessitates a proactive approach that incorporates multiple layers of defense, ensuring continuous monitoring and adaptation to emerging threats. This proactive stance is essential for safeguarding sensitive data and maintaining the integrity of software systems.
Best Practices for Securing Software Systems
Effective security measures require a multifaceted approach. This includes not only the installation of antivirus software, but also the implementation of strong passwords, regular updates, and firewalls. Consistent vigilance and adaptability to evolving threats are critical to maintaining a secure environment.
- Regular Software Updates: Software updates often contain critical security patches addressing vulnerabilities discovered by researchers. These patches are essential for mitigating the risks associated with known exploits. Failing to apply these updates leaves systems exposed to potential attacks. For example, a critical security flaw in a web browser might allow hackers to steal user credentials or execute malicious code.
Applying the update promptly eliminates this vulnerability.
- Robust Firewall Configuration: Firewalls act as a barrier between a network and external threats. A properly configured firewall controls network traffic, preventing unauthorized access and blocking malicious connections. Without a firewall, a system is vulnerable to intrusion attempts, potentially exposing sensitive data or allowing malware to propagate.
- Antivirus and Anti-malware Software: Antivirus and anti-malware programs are crucial for detecting and neutralizing malicious software. These programs scan files and processes, identifying and quarantining known threats. Implementing up-to-date anti-malware software is an important preventative measure against ransomware attacks, where malicious actors encrypt files and demand payment for decryption.
- Strong Password Policies: Strong passwords are the first line of defense against unauthorized access. Implementing strong password policies, including regular password changes and the use of complex passwords, is essential. This can significantly reduce the risk of account compromises, especially in environments with sensitive data.
Comprehensive Security Plan
A comprehensive security plan must address potential vulnerabilities proactively. This necessitates a systematic approach that integrates various security measures, including software updates, firewalls, and anti-virus software. Regular security audits are crucial to identify weaknesses and ensure that security controls are effective.
A comprehensive security plan should be regularly reviewed and updated to reflect evolving threats and vulnerabilities.
A thorough security plan should also incorporate incident response procedures. This involves having a clear plan for dealing with security breaches, including steps for containment, eradication, and recovery. A detailed plan for data backup and recovery is also critical to minimizing data loss in the event of a breach.
Importance of Regular Security Audits and Software Patching
Regular security audits and software patching are vital for maintaining a secure environment. They identify vulnerabilities before they are exploited. This proactive approach minimizes the risk of breaches and mitigates the impact of attacks.
| Aspect | Importance |
|---|---|
| Regular Security Audits | Identifying weaknesses and misconfigurations before they are exploited. |
| Software Patching | Addressing vulnerabilities as soon as they are discovered, preventing exploitation. |
Regular security audits and software patching are critical components of a robust security posture. They proactively identify and address potential vulnerabilities before they are exploited by malicious actors. This proactive approach ensures the continued integrity and safety of the system.
Employee Responsibility and Consequences
Protecting sensitive company data and systems is not solely the responsibility of IT departments. Every employee plays a crucial role in maintaining a secure digital environment. A strong security culture requires active participation from all personnel, understanding their responsibilities, and accepting accountability for their actions. Failure to adhere to security protocols can have severe consequences, impacting not only the individual but also the entire organization.Employee negligence can lead to significant security breaches, impacting data integrity, operational efficiency, and potentially causing irreparable harm.
A proactive approach to security, emphasizing employee training and awareness, is vital in mitigating these risks.
Employee Roles in System Security
Employees have a crucial role in safeguarding company systems. This includes adhering to established security protocols, promptly reporting any suspicious activity, and being vigilant in recognizing potential threats. A strong security culture relies on every employee understanding and practicing these responsibilities. By acting as the first line of defense, employees can significantly reduce the risk of security incidents.
Consequences of Non-Compliance with Security Protocols
Failure to adhere to security protocols can have significant repercussions for employees. These consequences can range from disciplinary actions to legal ramifications. It is essential to establish clear policies and procedures, coupled with consistent enforcement, to ensure a secure environment.
Employee Training and Awareness Programs
Effective employee training and awareness programs are vital for building a robust security culture. These programs should cover topics such as identifying phishing attempts, recognizing malware, and understanding password management best practices. Training should be ongoing, adapting to emerging threats and evolving security technologies.
Hearing about Microsoft’s Unix, Dell’s Linux, and a virus warning causing widespread infections and firings is pretty concerning. But, thankfully, advancements in tech like Broadcom chipsets expanding WiFi coverage areas broadcom chipsets expand wifi coverage areas could help mitigate some of the issues surrounding connectivity. Hopefully, this will ultimately make systems more secure and resilient against future attacks, and hopefully the virus warning won’t lead to more job losses.
Disciplinary Actions for Security Protocol Negligence
Maintaining a secure environment requires consistent enforcement of security policies. The following table Artikels potential disciplinary actions for employees who fail to comply with established security protocols. These actions aim to deter future occurrences and ensure accountability.
| Level of Negligence | Potential Disciplinary Actions |
|---|---|
| Minor violation (e.g., forgetting to log off, weak password usage) | Verbal warning, mandatory security training, and password policy reinforcement. |
| Moderate violation (e.g., clicking on suspicious links, failing to report suspicious activity) | Written warning, suspension of certain privileges (e.g., access to specific systems), additional security training. |
| Serious violation (e.g., intentional data breaches, malicious insider activity) | Suspension, termination of employment, and possible legal action. Depending on the extent of the breach, criminal charges may be filed. |
Response to a Virus Outbreak
A virus outbreak on a network can wreak havoc, impacting productivity, data integrity, and even the reputation of an organization. A swift and well-orchestrated response is crucial to minimize damage and restore normalcy. This section details a comprehensive procedure for containing a virus outbreak, isolating infected systems, restoring affected systems, and outlining preventative measures.
Containing a Virus Outbreak
A proactive approach to a virus outbreak involves swift action to limit the spread. The first step is to identify and isolate the infected systems immediately to prevent further contamination. Network segmentation, if possible, should be implemented to restrict the virus’s movement to isolated parts of the network. This should be done carefully, prioritizing minimal disruption to legitimate operations.
Immediately disable infected systems, and disconnect them from the network, to prevent the spread.
Isolating Infected Systems
Effective isolation is critical in preventing the virus from spreading further. This involves identifying infected systems and disconnecting them from the network as quickly as possible. This could include isolating workstations, servers, and network devices. The infected systems should be quarantined in a secure area, ideally separate from the rest of the network infrastructure, and handled with extreme care to avoid further spreading.
If the virus is highly contagious, consider using specialized tools for quarantine. This prevents the infection from spreading to other healthy systems.
Restoring Affected Systems
Restoring affected systems is a crucial aspect of recovery. The process involves careful analysis to identify the extent of the damage and appropriate remediation methods. A thorough investigation of the infection source is needed, along with steps to prevent a similar outbreak in the future. The most common approach involves reinstalling the operating system and applications on infected systems.
This should be performed using a clean backup image. This is essential to avoid any residual malware that might still be present on the system. It is vital to implement robust security measures to prevent future infections.
Steps to Take When a Virus Infection is Suspected
A well-structured response plan is crucial to mitigate the impact of a virus infection. The following table Artikels the steps to take when a virus infection is suspected, ensuring a rapid and effective response.
| Step | Action | Responsible Party |
|---|---|---|
| 1. Detection | Identify symptoms of infection on a system. | IT staff, Network administrators |
| 2. Isolation | Disconnect infected system(s) from the network. | IT staff, Network administrators |
| 3. Containment | Implement network segmentation to limit the spread. | Network administrators |
| 4. Analysis | Identify the type of virus and its scope of infection. | Security analysts |
| 5. Remediation | Clean infected systems and restore data from backups. | IT staff, Data recovery specialists |
| 6. Prevention | Implement enhanced security measures to prevent future infections. | Security team |
| 7. Reporting | Document the incident, actions taken, and lessons learned. | IT management |
Case Studies of Similar Incidents
Navigating the digital landscape requires constant vigilance against evolving threats. Learning from past incidents is crucial in strengthening our defenses and mitigating future risks. This section delves into specific examples of virus outbreaks affecting similar systems, analyzing their causes, impacts, and responses to glean valuable lessons.
Historical Virus Outbreaks in Multi-Platform Environments
Understanding past incidents provides valuable context for evaluating present and future risks. Similar vulnerabilities and attack vectors can be exploited across diverse operating systems, including Windows, macOS, Linux, and Unix-based systems. The shared characteristics of these platforms and the methodologies used in attacks highlight the need for comprehensive security measures.
So, Microsoft’s Unix, Dell’s Linux, and a virus warning – all getting infected and resulting in firings? It’s a bit like the MPAA’s approach to combating film swapping with lawsuits and software solutions, as seen in this article. It’s all about controlling the digital landscape, but it raises questions about the future of innovation and accessibility.
Ultimately, these tech-related battles seem to just lead to more infection and firing. A cycle of control and reaction.
The Impact of the “WORM-T33” Outbreak
In 2015, the WORM-T33 worm targeted a variety of operating systems, including Linux and Unix systems. This worm exploited vulnerabilities in system services, leading to widespread infections and significant disruptions. The impact extended beyond direct damage, encompassing substantial recovery costs and reputational harm for affected organizations. The incident underscored the necessity of timely patching and robust security protocols.
Its spread highlighted how quickly malicious code can propagate across interconnected networks.
Lessons Learned from the “Linux.Blaster” Incident
The Linux.Blaster worm, in 2003, demonstrated the potential for worms to exploit vulnerabilities in seemingly secure systems. Its rapid propagation across networks stressed the importance of proactive security measures and timely patching. This incident emphasized the critical need for regular security audits and vulnerability assessments. It also revealed the interconnected nature of systems and the cascading effects of security breaches.
Furthermore, it underscored the importance of incident response plans and the need for collaboration between affected organizations and security experts.
Comparative Analysis of Case Studies
| Incident | Operating Systems Affected | Primary Cause | Impact | Response | Key Lessons Learned |
|---|---|---|---|---|---|
| WORM-T33 | Windows, Linux, Unix | Vulnerabilities in system services | Widespread infections, network disruptions, recovery costs | Patching, security protocol improvements | Importance of timely patching, robust security protocols, incident response plans. |
| Linux.Blaster | Linux | Vulnerabilities in system services | Network congestion, service disruptions, financial losses | Proactive security measures, vulnerability assessments | Critical need for regular security audits and vulnerability assessments. |
Proactive Security Strategies
Staying ahead of the curve in the ever-evolving threat landscape requires a proactive security strategy. This involves more than just reacting to incidents; it necessitates a proactive approach to identify and mitigate potential vulnerabilities before they can be exploited. A robust security posture depends heavily on anticipating and preventing future attacks.A proactive approach to cybersecurity is akin to a well-maintained home.
Just as a homeowner regularly inspects their home for potential hazards (like loose wiring or faulty plumbing), organizations must regularly assess their systems for vulnerabilities. This proactive approach significantly reduces the risk of costly security breaches and reputational damage.
Strategies for Identifying and Mitigating Vulnerabilities
Proactive vulnerability identification involves employing various strategies, including regular security assessments and penetration testing. These measures help organizations identify weaknesses in their systems before malicious actors can exploit them. The aim is to understand the vulnerabilities present in the system and to put safeguards in place to prevent their exploitation.
Importance of Regular Security Assessments and Penetration Testing
Regular security assessments are crucial for identifying potential weaknesses in software and systems. These assessments involve a systematic review of the security posture, including the identification of potential vulnerabilities in applications, networks, and data storage systems. Penetration testing, a simulated attack, allows organizations to evaluate the effectiveness of their security controls. This involves attempting to exploit identified vulnerabilities to determine the potential impact of a real attack.
The insights gained from these tests inform security improvements and enhance overall resilience.
Use of Threat Intelligence to Anticipate and Prevent Future Attacks
Threat intelligence is invaluable in anticipating and preventing future attacks. By analyzing information about emerging threats, vulnerabilities, and attack patterns, organizations can adapt their security measures proactively. This involves staying updated on the latest malware, techniques used by cybercriminals, and the evolving threat landscape. Leveraging publicly available information, threat feeds, and threat intelligence platforms allows for a more informed and proactive approach to cybersecurity.
For instance, observing a surge in ransomware attacks against a specific type of software can alert organizations to potential vulnerabilities and necessitate proactive measures to prevent infections.
Flowchart Illustrating a Proactive Security Strategy, Microsofts unix dells linux and a virus warning get infected get fired

The flowchart (though not an actual image) depicts a proactive security strategy. It starts with a vulnerability assessment to identify weaknesses, which then triggers a remediation process. Threat intelligence feeds are used to update and enhance the security posture. Regular penetration testing is conducted to validate security measures and identify any gaps. This cyclical process ensures continuous improvement in security practices.
- Vulnerability Assessment: Identify potential weaknesses in software and systems through automated scans, manual reviews, and security assessments.
- Threat Intelligence Analysis: Track and analyze emerging threats, vulnerabilities, and attack patterns to anticipate potential attacks.
- Mitigation and Remediation: Address identified vulnerabilities through patching, configuration changes, and implementing security controls.
- Penetration Testing: Conduct simulated attacks to validate the effectiveness of security controls and identify any weaknesses.
- Monitoring and Reporting: Continuously monitor security logs, detect anomalies, and report on the effectiveness of the proactive security strategy.
Final Wrap-Up
In conclusion, the security of Microsoft’s Unix, Dell’s Linux, and other software systems hinges on a multi-faceted approach. Proactive measures, employee awareness, and robust response plans are essential to safeguard against virus infections. This post highlights the critical importance of security protocols, emphasizing that vigilance and preparedness are paramount in the digital age. The interconnected nature of these systems requires a comprehensive understanding of the vulnerabilities, consequences, and preventative measures.