More Threatening Storm Worm on the Loose
More threatening storm worm on the loose, a digital plague poised to wreak havoc on our interconnected world. This isn’t your garden-variety computer virus; we’re talking about a sophisticated, self-replicating threat capable of taking down critical infrastructure, disrupting communication networks, and potentially causing widespread societal disruption. Imagine a scenario where the very fabric of our digital existence is under siege, and the consequences are far-reaching, impacting everything from energy grids to financial systems.
This exploration delves into the multifaceted nature of this digital menace, examining its potential damage, vulnerability analysis, mitigation strategies, predictive modeling, and illustrative case studies. We’ll unpack the defining characteristics of a storm worm, assess its potential impact, and consider the crucial role of cybersecurity in preventing its spread and mitigating its effects. Get ready to dive into a world where a single line of malicious code can trigger a cascading chain of events with potentially catastrophic consequences.
Defining the Threat
A storm worm, a particularly insidious form of malware, exploits vulnerabilities in interconnected systems, often targeting critical infrastructure during periods of heightened environmental instability. Its unique characteristics, combined with the potential for widespread disruption, make it a significant threat to modern society. This analysis delves into the nature of storm worms, their potential variations, and the devastating consequences they can unleash.Storm worms leverage existing network infrastructures, exploiting vulnerabilities in software and hardware to spread rapidly.
They can effectively utilize environmental events, such as storms or power outages, to mask their malicious activities and gain access to critical systems. The consequences can range from simple data breaches to complete system paralysis, depending on the sophistication and target of the attack.
Types of Storm Worms
Storm worms can be categorized by their method of attack, their target systems, and their ultimate objectives. Some storm worms focus on exploiting vulnerabilities in weather forecasting systems, while others target communication networks and critical infrastructure, like power grids or transportation systems. The potential variations are numerous, reflecting the diverse range of interconnected systems and potential attack vectors. Each type of storm worm carries its own unique characteristics, including its speed of propagation, the types of systems it targets, and the degree of damage it can inflict.
Potential Variations and Unique Characteristics
The diversity of storm worms arises from their ability to adapt and evolve to exploit new vulnerabilities. For example, a storm worm designed to target weather forecasting systems could potentially manipulate weather data, leading to incorrect predictions or even causing significant delays in disaster response. Another variation might focus on targeting communication networks, causing widespread disruptions in communication and coordination, hindering efforts to address the storm’s immediate impact.
This new storm worm is seriously scary, potentially wreaking havoc on digital systems. Meanwhile, Samsung’s impressive feat in developing a new hybrid hard drive, like the one detailed in samsung achieves hybrid hard drive milestone , offers a glimmer of hope for robust data storage solutions. But even with these advancements, we still need to be wary of this increasingly dangerous worm.
Historical and Fictional Examples
The potential for widespread damage from storm worms is not purely theoretical. Fictional narratives, such as those featuring advanced cyberattacks, have highlighted the devastating effects of such threats. Historical events, though not involving the precise term “storm worm,” have shown the vulnerability of critical infrastructure to disruption. These examples underscore the potential for widespread damage and the need for proactive security measures.
Potential Damage
The impact of a storm worm can be substantial, affecting various aspects of modern life. Disruptions to communication networks can impede emergency response efforts, hindering coordination between first responders and the affected population. Attacks on power grids can cause widespread blackouts, leading to economic losses and potential safety hazards. The damage to infrastructure, such as transportation networks or water treatment facilities, can further exacerbate the crisis.
Characteristics of Storm Worms
| Type | Severity | Potential Targets |
|---|---|---|
| Weather Forecasting System Targeting Worm | High | Weather forecasting systems, disaster response systems, public safety |
| Communication Network Worm | Medium to High | Communication networks, emergency services, coordination systems |
| Critical Infrastructure Worm | Extremely High | Power grids, transportation networks, water treatment facilities, financial institutions |
Impact Assessment
A storm worm, unlike a conventional virus, possesses a unique and devastating potential for widespread damage. Its ability to exploit vulnerabilities in interconnected systems, coupled with its self-replicating nature, presents a significant threat across multiple sectors. This assessment details the potential economic, social, and human consequences of such an attack.The impact of a storm worm attack extends far beyond the initial infection.
It creates a cascading effect, disrupting critical infrastructure, damaging economies, and causing profound social unrest. Understanding the potential ramifications is crucial for developing effective mitigation strategies.
Economic Consequences
The economic fallout from a storm worm attack could be catastrophic. Disruptions to financial markets, power grids, and transportation networks could lead to massive losses. Companies could face significant operational downtime, lost revenue, and potential bankruptcy. The global financial system, already facing uncertainties, could experience severe instability. Furthermore, the cost of recovery, including repairs, data restoration, and system upgrades, would be substantial and potentially exceed the capacity of many affected entities.
Speaking of things that feel a bit unsettling, this more threatening storm worm on the loose is definitely giving me the creeps. It’s got me wondering about other tech-related anxieties, like the future of high-definition video. Apparently, Disney is backing Blu-ray, but won’t rule out HD DVD, which is a bit of a head-scratcher, to be honest. This whole situation makes me think that maybe the real threat isn’t just this creepy storm worm, but the uncertainty of future technology.
Still, back to the worm… It’s definitely causing me some serious tech-related nightmares.
A real-world example is the 2017 NotPetya attack, which caused significant disruption to global supply chains and businesses, demonstrating the potential for widespread economic damage.
Social Disruption
A storm worm attack would cause profound social disruption. Essential services like healthcare, communication, and emergency response systems could be severely compromised. This would exacerbate existing social inequalities and create hardship for vulnerable populations. Loss of essential utilities, such as electricity and water, would lead to widespread panic and disruption of daily life. The social impact would be felt globally.
Loss of Human Life
While direct loss of human life from a storm worm attack itself might be minimal, the ripple effect could have devastating consequences. Disruptions to healthcare systems, food supplies, and transportation could lead to preventable deaths, particularly among vulnerable populations. This would have long-term impacts on society, causing social unrest and creating a humanitarian crisis. The 2021 Colonial Pipeline attack, while not a storm worm, highlights how disruptions to critical infrastructure can create significant social consequences.
Comparison with Other Natural Disasters
| Disaster Type | Damage Characteristics | Storm Worm Comparison |
|---|---|---|
| Hurricane | Localized, concentrated damage; infrastructure damage; potential loss of life | Widespread, interconnected damage; global impact; disruption of critical infrastructure |
| Earthquake | Localized, sudden damage; infrastructure damage; potential loss of life | Widespread, sustained damage; global impact; potential for cascading failures |
| Pandemic | Global health crisis; economic disruption; social isolation | Global digital crisis; economic disruption; social disruption; potential for humanitarian crisis |
The table above demonstrates a comparative assessment. A storm worm attack has the potential to cause damage across sectors, impacting individuals and communities in ways comparable to or exceeding other natural disasters.
Ripple Effect Across Sectors
A storm worm attack would have a devastating ripple effect across various sectors of society. Financial institutions, healthcare providers, energy companies, and transportation networks would all be affected. The attack would disrupt supply chains, damage critical infrastructure, and cause widespread economic instability. The interconnected nature of modern society means that a storm worm attack would have a far-reaching impact, affecting individuals and communities globally.
The impact would be like a chain reaction, one sector affecting another, leading to a global crisis.
This emphasizes the need for robust preventative measures and effective incident response plans.
Vulnerability Analysis
Unraveling the potential devastation of a sophisticated storm worm necessitates a deep dive into the vulnerabilities it can exploit. This analysis identifies critical infrastructure weaknesses, examines communication network vulnerabilities, and explores the human factor in susceptibility. Understanding these aspects is crucial for developing robust mitigation strategies and minimizing the damage a storm worm can inflict.Identifying and prioritizing these weaknesses is vital to crafting effective defense mechanisms.
A methodical approach to assessing potential harm, combined with proactive measures, can greatly reduce the impact of such an attack.
Critical Infrastructure Vulnerabilities, More threatening storm worm on the loose
Critical infrastructure sectors, including energy, finance, and transportation, hold significant vulnerabilities to a storm worm attack. These sectors often rely on interconnected systems and automated processes, making them particularly susceptible to widespread disruptions. A compromised control system in a power grid, for example, could trigger cascading failures throughout the entire system.
This more threatening storm worm is causing quite a stir, and frankly, it’s a bit unnerving. Thankfully, amidst all the tech anxieties, Lenovo launched the ThinkPad X41, a fantastic addition to the laptop market, offering impressive performance and durability for a great price. Hopefully, with innovations like this lenovo launches thinkpad x41 , we can find solutions to keep our data safe from this persistent worm.
It’s a worrying situation, though.
Communication Network Weaknesses
Communication networks, the lifeblood of modern operations, are prime targets for a storm worm. The reliance on open protocols, legacy systems, and weak security practices creates avenues for exploitation. Outdated firewalls, insufficient intrusion detection systems, and unpatched software create gaping holes for malicious actors to infiltrate and disrupt communications. Furthermore, the interconnected nature of these networks means that a single compromised node can potentially disrupt entire segments of the system.
For instance, a compromised router in a financial network could disrupt trading activity across multiple institutions.
Human Element in Susceptibility
The human element plays a significant role in the susceptibility of systems to a storm worm. Lack of awareness, poor security practices, and insufficient training create openings for exploitation. A compromised employee clicking on a malicious link or failing to follow established security protocols can inadvertently introduce a storm worm into the network. Social engineering tactics targeting employees, designed to gain access to sensitive information or manipulate system controls, pose another critical vulnerability.
Furthermore, inadequate response protocols and delayed incident reporting can exacerbate the impact of an attack.
Vulnerability Categorization by Sector
| Sector | Vulnerable Components | Potential Impact |
|---|---|---|
| Energy | Power grids, smart meters, control systems | Widespread power outages, disruption of essential services, cascading failures |
| Finance | Online banking platforms, payment systems, trading networks | Disruption of financial transactions, loss of data, reputational damage |
| Transportation | Traffic management systems, railway signaling, air traffic control | Disruption of transportation networks, delays, accidents |
| Water | Water treatment facilities, distribution systems, monitoring equipment | Contaminated water supplies, water shortages, public health crisis |
Vulnerability Identification and Prioritization
A structured approach is essential for identifying and prioritizing vulnerabilities to a storm worm. This involves a multi-stage process. Firstly, a comprehensive inventory of critical infrastructure components and their interconnectedness must be established. Secondly, a risk assessment should be performed to evaluate the likelihood and potential impact of each vulnerability. Thirdly, prioritize vulnerabilities based on the combined risk factors.
A scoring system, for example, can assign weights to likelihood and impact, allowing for a ranked list of vulnerabilities that require immediate attention. The use of threat intelligence feeds and industry best practices can also significantly enhance this process.
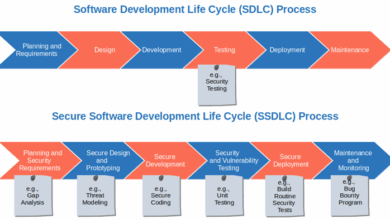
Mitigation Strategies: More Threatening Storm Worm On The Loose

Storm worms, with their ability to rapidly propagate and disrupt critical infrastructure, demand proactive mitigation strategies. Failure to implement robust preventative measures can lead to widespread devastation. This section delves into the key approaches for containing the spread of a storm worm and safeguarding vital systems.The effectiveness of mitigation hinges on a multi-layered approach that combines preventative measures, proactive security protocols, and swift incident response capabilities.
A comprehensive strategy must anticipate potential vulnerabilities and adapt to the evolving nature of these threats.
Preventative Strategies to Limit Worm Spread
Early detection and rapid containment are crucial to limiting the spread of a storm worm. Strategies for prevention include network segmentation, limiting exposure, and robust access controls.
- Network Segmentation: Dividing the network into smaller, isolated segments limits the impact of a breach. This approach isolates the affected segment, preventing the worm from spreading throughout the entire network.
- Limited Exposure: Minimizing external access points and employing strong firewalls reduces the worm’s potential entry points and infection vectors. Restricting access to specific systems, especially those that are critical, helps contain the threat.
- Robust Access Controls: Implementing multi-factor authentication (MFA) and stringent authorization policies limit unauthorized access, crucial for preventing initial compromise. Strong passwords, frequent updates, and enforced security protocols are critical in this area.
Security Measures for Critical Infrastructure Protection
Critical infrastructure, such as power grids, financial institutions, and healthcare systems, requires enhanced security measures to withstand a storm worm attack. These systems are often the primary targets due to their significant societal impact.
- Redundancy and Failover Systems: Implementing redundant systems and failover mechanisms for critical infrastructure ensures continuous operation even in the event of a disruption. This redundancy is essential to minimize downtime and maintain essential services.
- Intrusion Detection and Prevention Systems (IDPS): Employing advanced IDPS solutions monitors network traffic for malicious patterns and activities, immediately alerting administrators to potential threats. IDPS is an essential tool in identifying and blocking storm worm activity before it can spread.
- Regular Vulnerability Assessments: Proactively identifying and addressing potential vulnerabilities within critical infrastructure systems through regular assessments. This proactive approach reduces the potential impact of a storm worm attack. Patches and updates must be applied promptly.
Role of Cybersecurity Protocols
Cybersecurity protocols play a pivotal role in mitigating the effects of a storm worm. They establish a standardized approach to security and provide a framework for effective incident response.
- Security Information and Event Management (SIEM): SIEM systems centralize security logs from various sources, providing a comprehensive view of network activity. This consolidated view allows for early detection and analysis of suspicious patterns, including storm worm activity.
- Incident Response Plans: A well-defined incident response plan Artikels the steps to take when a storm worm attack occurs. This plan should be regularly reviewed and updated to address emerging threats and best practices.
- Regular Security Awareness Training: Educating personnel about potential threats, such as storm worms, and best practices for cybersecurity awareness is essential. Training helps to prevent human error, a common vector for these attacks.
Comparative Analysis of Mitigation Approaches
Different approaches to mitigating storm worm attacks offer varying levels of effectiveness. Understanding the strengths and weaknesses of each approach is crucial for tailoring a comprehensive strategy.
- Proactive vs. Reactive: Proactive measures, such as preventative strategies and vulnerability assessments, are more effective than reactive measures, like emergency response. A proactive approach is more cost-effective in the long run.
- Centralized vs. Decentralized Security: A centralized security approach allows for consistent security policies and better monitoring across the organization. However, a decentralized approach might be more flexible for highly specialized systems.
- Technology vs. Human Factors: While technology plays a crucial role in mitigation, human factors remain significant. Security awareness training is vital to ensure employees are aware of the threat and can respond appropriately.
Lessons Learned from Similar Incidents
Examining past incidents involving similar threats offers valuable lessons for developing effective mitigation strategies.
- Example: The 2017 NotPetya ransomware attack demonstrated the devastating impact of a rapidly spreading worm on global supply chains. Lessons learned include the importance of robust backup and recovery plans and the need for regular patching.
Predictive Modeling
Storm worms, with their ability to rapidly spread across networks, pose a significant threat. Predictive modeling is crucial for understanding and mitigating these attacks. By analyzing historical data, identifying patterns, and developing models, we can better anticipate future threats and prepare for potential impacts. This approach allows us to proactively develop countermeasures and safeguard critical infrastructure.
Framework for Predicting Likelihood and Impact
A comprehensive framework for predicting storm worm attacks considers several key factors. These include network topology, known vulnerabilities in software, the presence of botnets, and the behavior of the worm itself. Sophisticated algorithms can analyze these factors to estimate the likelihood of an attack, considering factors like the worm’s propagation rate, target systems, and the effectiveness of security measures.
Modeling Worm Propagation Paths
Visualizing the potential paths a storm worm might take to spread across a network is essential for targeted defense. This model involves creating a graph-based representation of the network, with nodes representing systems and edges representing connections. The worm’s propagation path can be modeled as a sequence of node traversals, taking into account factors like firewall rules, intrusion detection systems, and the worm’s infection logic.
For instance, a worm might exploit known vulnerabilities in web servers, then propagate to vulnerable database servers on the same network segment, before spreading further through the network. Understanding these pathways allows for proactive defenses, such as isolating vulnerable systems or patching known weaknesses.
Estimating Potential Attack Costs
Estimating the potential cost of a storm worm attack requires considering direct and indirect losses. Direct costs encompass system downtime, data recovery, security software upgrades, and the cost of incident response teams. Indirect costs include loss of productivity, damage to reputation, regulatory fines, and potential legal liabilities. For example, a large financial institution could experience millions in losses due to fraudulent transactions, system outages, and reputational damage if a storm worm attack disrupts their operations.
Developing precise cost estimates often involves scenario analysis and financial modeling, accounting for different attack vectors and the severity of the impact.
Factors Influencing Storm Worm Attack Success
The success of a storm worm attack hinges on several crucial factors. These factors include the worm’s design, the presence of vulnerable systems, the network’s topology, the effectiveness of security measures, and the actions taken by security teams. For instance, a sophisticated worm exploiting previously unknown vulnerabilities could have a higher chance of success than one relying on widely known exploits.
The density of the network, the number of vulnerable systems, and the worm’s propagation rate also play significant roles. Similarly, the speed and efficiency of security responses are critical in mitigating the impact of an attack.
Predicting Future Attacks Using Historical Data
Historical data on previous storm worm attacks provides valuable insights for predicting future outbreaks. Analyzing the characteristics of past attacks, such as the vulnerabilities exploited, the propagation patterns, and the geographical distribution, allows us to identify trends and develop predictive models. For example, if a particular type of vulnerability is consistently exploited in storm worm attacks, security teams can focus on patching those vulnerabilities to prevent future attacks.
Machine learning algorithms can be used to analyze large datasets of historical data to identify patterns and anomalies, enabling more accurate predictions. These patterns often reveal common attack vectors, allowing for the proactive implementation of security measures and the development of more resilient systems.
Case Studies
Storm worms, unlike traditional viruses, pose a unique and escalating threat to modern infrastructure. Their ability to rapidly propagate and exploit vulnerabilities across interconnected systems necessitates a thorough understanding of potential impacts and effective mitigation strategies. Analyzing historical events and hypothetical scenarios allows us to anticipate and prepare for the devastating consequences of such an attack.This section delves into fictional and historical case studies, drawing parallels to the emerging threat of storm worms, focusing on their impact on specific sectors and the lessons learned from response and recovery efforts.
Fictional Case Study: “The Meridian Maelstrom”
In a fictional scenario, a newly discovered storm worm, dubbed “Meridian Maelstrom,” exploited vulnerabilities in the city’s critical infrastructure. The attack initiated with a targeted phishing campaign, compromising employee accounts across various city departments. This initial breach allowed the worm to rapidly spread through the city’s network, infecting critical systems like traffic management, water purification, and power grids.
The worm’s primary function was to disrupt services by overwhelming systems with false data and commands. The attack resulted in widespread power outages, traffic gridlock, and contamination of the city’s water supply. City services were paralyzed, and emergency response efforts were hampered. Recovery involved extensive system remediation, rebuilding trust with the public, and implementing stringent security protocols.
This case study highlights the interconnected nature of modern infrastructure and the cascading effects of a storm worm attack.
Historical Event Parallel: The 2010 Power Grid Blackout
The 2010 Northeast blackout, while not a direct storm worm attack, serves as a valuable historical parallel. The event highlighted the vulnerability of power grids to cascading failures. Although triggered by a different mechanism, the cascading nature of the blackout echoes the potential for a storm worm to exploit vulnerabilities in interconnected systems. The rapid spread of the disturbance through the grid demonstrates how a targeted attack could overwhelm and disable crucial infrastructure, leading to widespread disruptions.
Storm Worm Targeting Specific Sectors
A storm worm’s targeting of specific sectors can be highly impactful. In the financial industry, the worm could manipulate stock trading algorithms, leading to market crashes and massive financial losses. In the energy sector, the worm could disrupt power grids, causing widespread blackouts and halting industrial operations. The worm’s targeting could even extend to transportation systems, disrupting air, rail, and road networks, causing major societal disruption.
For instance, a storm worm could manipulate traffic signals, causing significant traffic jams and delays.
Response and Recovery Measures
The fictional “Meridian Maelstrom” case study, along with the 2010 blackout, emphasizes the critical need for proactive security measures. Response measures focused on isolating affected systems, containing the spread of the worm, and restoring critical services. Recovery efforts involved significant system remediation, replacing infected hardware, and implementing security enhancements. Crucially, lessons learned involved the creation of a dedicated incident response team, proactive vulnerability management, and enhancing communication protocols.
Similarities and Differences Table
| Feature | Fictional “Meridian Maelstrom” | 2010 Northeast Blackout | Potential Storm Worm Impact |
|---|---|---|---|
| Triggering Mechanism | Sophisticated storm worm exploiting network vulnerabilities | Equipment malfunction, cascading failures | Sophisticated storm worm exploiting network vulnerabilities |
| Impact Scope | City-wide disruption of critical services | Regional power grid disruption | Potential global impact on interconnected systems |
| Speed of Propagation | Rapid, exploiting network connections | Gradual, cascading | Rapid, exploiting network connections |
| Recovery Time | Days to weeks | Days to weeks | Potentially longer, depending on scale and remediation efforts |
Last Point

In conclusion, the threat of a storm worm is undeniably real and potentially devastating. We’ve explored the various facets of this digital plague, from its definition and impact assessment to vulnerability analysis and mitigation strategies. This analysis highlights the importance of proactive cybersecurity measures, robust infrastructure protection, and a collective understanding of the risks involved. By understanding the potential pathways of a storm worm, the impact of its actions, and the crucial measures for prevention and mitigation, we can better safeguard our digital future and ensure the resilience of our interconnected world.