Myspace Bug Alerts Could Trigger Mischief
Myspace bug alerts could trigger mischief, potentially leading to significant issues for users and the platform’s reputation. This exploration delves into the vulnerabilities of MySpace-like social media platforms, examining the potential for exploitation by malicious actors and the necessary security measures to mitigate these risks. We’ll analyze various bug types, their impacts, and potential responses from users and platform administrators.
Understanding the potential for misuse of bugs in social media is crucial. Different types of bugs, from simple logic errors to serious security vulnerabilities, can have far-reaching consequences. This analysis will examine how these vulnerabilities can be exploited and the potential harm to users and the platform.
Understanding MySpace Bug Alerts
MySpace-like social media platforms are crucial hubs for communication and connection, but vulnerabilities can severely impact users and the platform’s reputation. Understanding the potential mischief caused by bugs is essential for both platform administrators and users to mitigate risks. Addressing these issues proactively is vital for maintaining a safe and trustworthy online environment.MySpace-like platforms, with their complex user interactions and data handling, are susceptible to various types of bugs.
These bugs, if left unaddressed, can create opportunities for malicious actors and disrupt the normal functionality of the platform. The consequences can range from minor inconveniences to serious security breaches, potentially jeopardizing user data and eroding trust in the platform.
Potential Impact of Bugs
Bugs in social media platforms can have significant consequences for both users and the platform itself. Security vulnerabilities can expose sensitive user information, leading to identity theft or financial loss. Logic errors can cause unexpected behavior, such as incorrect data display, account suspension, or even the denial of service for other users. The impact of these bugs can range from minor annoyances to severe disruptions, affecting the platform’s reputation and user experience.
Types of Bugs Causing Mischief
Several types of bugs can trigger mischief in social media platforms. Security vulnerabilities allow unauthorized access to user data, often leading to data breaches or account hijacking. Logic errors, while seemingly less severe, can result in unintended consequences, like incorrect data display or malfunctioning features. Malicious code injection, if not properly sanitized, can be exploited to introduce harmful elements into the platform, affecting the user experience or even compromising security.
Examples of Bug Manifestations
Bugs can manifest in various ways within user interactions. For example, a security vulnerability might allow a hacker to gain access to user passwords, enabling them to impersonate users or steal sensitive data. A logic error might cause a user’s profile to display incorrectly, or their posts to be duplicated. Misconfigured access controls can lead to unauthorized users gaining access to restricted areas of the platform.
Inadequate input validation could permit malicious actors to inject scripts or commands, compromising the platform’s security.
Consequences for Users and Platform
The consequences of such bugs for users are substantial, including identity theft, financial losses, and reputational damage. For the platform, these consequences can include legal repercussions, loss of user trust, and a decline in user engagement and revenue. The negative impact on user experience is often substantial, causing frustration and distrust, leading to a decline in user retention.
Comparison of Bug Types and Impact
| Bug Type | Description | Impact on Users | Impact on Platform |
|---|---|---|---|
| Security Vulnerability | Allows unauthorized access to user data or functionality. | Potential for data breaches, identity theft, financial loss. | Damage to platform reputation, legal liabilities, loss of user trust. |
| Logic Error | Causes unintended or incorrect behavior in the platform’s logic. | Incorrect data display, malfunctioning features, unexpected account actions. | Negative user experience, potential for system overload, disruption of service. |
| Malicious Code Injection | Allows attackers to introduce harmful code into the platform. | Compromised accounts, data theft, malware infections. | System compromise, data breaches, loss of user trust. |
| Misconfigured Access Controls | Improperly defined permissions allowing unauthorized access. | Data breaches, account takeovers, unauthorized access to private information. | Damage to platform reputation, security risks, loss of user trust. |
| Inadequate Input Validation | Failure to properly validate user input, allowing malicious input. | Exposure to malicious code, system crashes, unexpected behavior. | Security breaches, data corruption, loss of platform functionality. |
Potential Mischief Triggered by Bugs
MySpace, and similar social networking platforms, are vulnerable to exploitation. Bugs, no matter how seemingly minor, can be leveraged by malicious actors to wreak havoc on user accounts, the platform itself, and even the wider digital ecosystem. Understanding these vulnerabilities is crucial for mitigating potential harm and building resilient online environments.Malicious actors can exploit vulnerabilities in MySpace-style platforms to gain unauthorized access, disrupt services, and spread misinformation.
This exploitation can manifest in various ways, from subtle data breaches to crippling denial-of-service attacks. The potential for harm is substantial, affecting both individual users and the platform’s overall reputation and functionality.
Malicious Actions and Their Impact
Understanding how these vulnerabilities can be exploited is paramount for securing such platforms. Malicious actors may utilize flaws to gain unauthorized access, manipulate user data, or disrupt service.
- Data breaches: A vulnerability in user authentication or data storage could allow attackers to gain access to sensitive user information, including personal details, financial data, or even login credentials. This information could be used for identity theft, financial fraud, or to harass or blackmail users. The 2017 Equifax data breach, for instance, exposed millions of individuals’ sensitive data, highlighting the catastrophic consequences of such vulnerabilities.
- Denial-of-service (DoS) attacks: Exploiting a platform’s vulnerabilities, attackers can flood it with requests, effectively making the service unavailable to legitimate users. This can disrupt the platform’s functionality, damage its reputation, and result in lost revenue for the platform’s owners. These attacks often target high-profile websites, aiming to cripple their operations and cause widespread disruption. For example, the frequent DDoS attacks targeting online gaming platforms demonstrate the severity of this threat.
- Phishing and social engineering: A bug in the platform’s security or presentation could be exploited to create misleading login pages or display malicious links, allowing attackers to trick users into divulging their login credentials or downloading malware. This can lead to account hijacking, data theft, or the spread of malware to other users. Examples include fake social media profiles that trick users into clicking malicious links.
Vulnerability Exploitation Scenarios
The potential mischief stemming from vulnerabilities varies greatly. The harm inflicted can range from minor inconveniences to catastrophic failures, and these outcomes can affect the platform’s overall functionality and user trust.
| Malicious Action | Vulnerability | Impact |
|---|---|---|
| Unauthorized Account Access | Weak password hashing algorithms, insecure session management | Compromised user accounts, theft of sensitive data, financial fraud |
| Data Manipulation | Lack of input validation, SQL injection vulnerabilities | Data corruption, inaccurate user profiles, manipulation of user interactions |
| Denial-of-Service Attack | Poorly designed server-side logic, insufficient resource management | Platform unavailability, loss of revenue, damage to reputation |
| Malware Distribution | Vulnerabilities in the platform’s code or user interface | Infected user devices, theft of sensitive data, further spread of malware |
User and Platform Responses to Bugs

MySpace, in its heyday, was a platform brimming with both creativity and vulnerabilities. Understanding how users and platform administrators responded to bugs is crucial to comprehending the dynamic nature of online communities and the evolving relationship between users and technology. Effective response mechanisms, or the lack thereof, could directly impact the platform’s stability, reputation, and ultimately, its longevity.The interplay between user reactions and platform responses to bugs is complex.
Myspace bug alerts, while potentially harmless, could unfortunately trigger mischief if not handled carefully. Users need to be extra vigilant, especially since firms like those involved in firms come together to fight phishing attacks are proactively working to mitigate the risk of malicious actors exploiting vulnerabilities. This highlights the importance of user awareness and the ongoing efforts to prevent potential harm from these types of alerts.
User behavior is influenced by factors such as perceived severity, personal experience, and the platform’s track record. Conversely, platform responses depend on their internal processes, communication channels, and the resources available to address the issues.
User Reactions to Bug Alerts or Suspicious Activity
Users encountering bug alerts or suspicious activity on MySpace often react in a variety of ways. Some may dismiss the alerts as minor inconveniences, while others may become highly concerned, particularly if the issues affect their personal accounts or data. A significant portion of users may report the issue through the available channels, while others may take alternative actions, such as sharing their experiences in online forums or social media groups.
User reactions can range from mild annoyance to significant concern and can influence the platform’s response strategy.
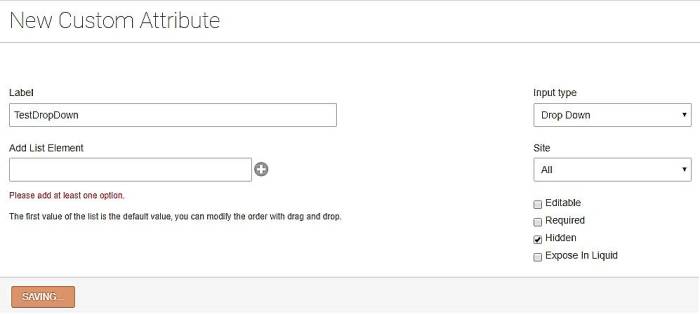
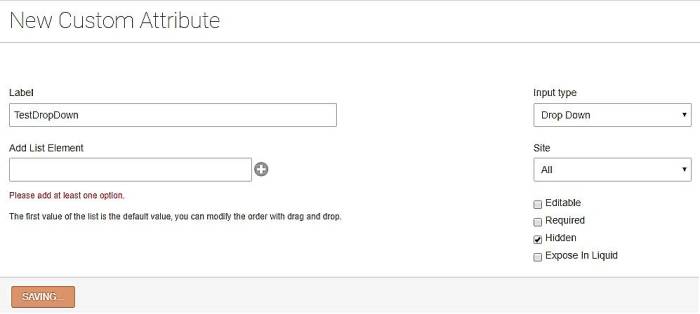
Platform Administrator or Developer Responses to Bug Reports or Incidents, Myspace bug alerts could trigger mischief
Platform administrators and developers face the challenge of managing a large volume of bug reports and incidents. Effective response strategies often involve establishing clear channels for reporting, categorizing issues, and prioritizing repairs based on severity and impact. A critical component is transparent communication with users, keeping them informed about the progress of bug fixes and the potential downtime or disruptions.
Efficient issue tracking and resolution systems are essential to maintaining user trust and stability.
Myspace bug alerts could lead to some pretty silly shenanigans, especially if the security vulnerabilities are exploited. Meanwhile, Cisco and Fujitsu are gearing up to dominate the Japanese router market, which is interesting given the potential for a domino effect if those Myspace bugs get exploited by malicious actors. This could potentially impact the new router deployments, creating a fascinating cybersecurity conundrum.
cisco fujitsu set to storm japanese router market So, while the Japanese router market heats up, it’s crucial to remember the potential for mischief stemming from those Myspace bug alerts.
Effectiveness of Various Response Strategies
Different response strategies vary in their effectiveness. A prompt and transparent response, coupled with a well-defined communication plan, often fosters trust and satisfaction among users. Conversely, slow or inadequate responses can lead to user frustration and damage the platform’s reputation. The platform’s response should prioritize accuracy and reliability, ensuring that users receive timely and helpful information. For instance, a clear timeline for resolution, alongside regular updates, can significantly improve user satisfaction.
Potential Consequences of Slow or Inadequate Responses to Bug Alerts
Delayed or inadequate responses to bug alerts can have significant consequences. Loss of user trust is a major concern, potentially leading to decreased user engagement and a negative impact on the platform’s reputation. The spread of misinformation and rumors can exacerbate the problem, making it difficult for the platform to regain user confidence. Financial losses, legal issues, and even the platform’s eventual decline can result from prolonged or mishandled responses to security breaches or critical bugs.
Typical Response Process to a Bug Alert (Flowchart)
+-----------------+ | Bug Alert Received| +-----------------+ | | | Is it critical? |-->[Yes] Critical Incident Response | |-->[No] Routine Incident Response +-----------------+ | | | Critical Incident Response: | | +-----------------+ | 1.Escalate to | | management | | 2. Assess Impact | | 3. Develop Plan | | 4. Communicate | | 5. Implement | | 6.
Monitor & Re- | | assess | +-----------------+ | | | Routine Incident Response: | | +-----------------+ | 1. Log & Categorize | | 2.
Prioritize | | 3. Assign to Team | | 4. Develop Fix | | 5. Test & Deploy | | 6. Monitor | +-----------------+
This flowchart Artikels a simplified response process, highlighting the key stages involved in addressing bug alerts.
Variations exist based on the platform’s specific needs and organizational structure.
Security Measures to Prevent Mischief: Myspace Bug Alerts Could Trigger Mischief
MySpace-style bugs, if left unaddressed, can lead to significant disruptions and misuse. Understanding the potential for mischief is crucial to implementing effective security measures. Preventing such incidents requires a multi-layered approach encompassing various protocols and best practices.
Robust security measures are not just about preventing attacks, but also about building resilience into the platform’s architecture. This proactive approach is key to minimizing the impact of potential breaches and ensuring a secure user experience.
Preventive Measures to Mitigate Risks
Implementing proactive measures is essential to reduce the likelihood of malicious activity exploiting vulnerabilities. These measures go beyond simply patching existing flaws and aim to prevent similar problems from arising in the future.
- Regular Security Audits: Systematic reviews of the platform’s codebase, infrastructure, and security protocols are crucial. These audits identify potential weaknesses before they can be exploited, allowing for timely remediation. Regular audits, ideally quarterly, are essential for maintaining a secure environment.
- Input Validation and Sanitization: Scrutinizing all user inputs is critical. Invalid or malicious input can be used to bypass security controls. Rigorous validation and sanitization procedures are vital to prevent such exploits. This includes verifying data types and ranges, filtering out potentially harmful characters, and encoding data appropriately.
- Secure Coding Practices: Educating developers on secure coding practices is paramount. Adherence to industry best practices can significantly reduce the risk of introducing vulnerabilities during the development process. Training programs for developers should be ongoing and regularly updated to reflect the latest security threats.
- Multi-Factor Authentication (MFA): Implementing MFA enhances security by requiring multiple verification steps beyond a simple password. This makes it significantly harder for attackers to gain unauthorized access, even if they obtain a password. MFA is a proven method for preventing unauthorized access and should be considered a standard security feature.
Improving Security Protocols
Security protocols should evolve to address emerging threats. Adaptability is crucial in today’s dynamic threat landscape.
- Proactive Vulnerability Scanning: Employing automated tools to identify vulnerabilities before they are exploited is crucial. These tools scan the platform for known weaknesses and provide recommendations for remediation.
- Regular Security Awareness Training: Training users on recognizing and reporting suspicious activities, such as phishing attempts or malicious links, is important. Educating users about security best practices is key to a robust defense strategy.
- Security Information and Event Management (SIEM): Implementing SIEM systems to monitor logs and detect anomalies in real-time allows for rapid response to security incidents. These systems are critical in maintaining a proactive security posture.
Security Measures Summary
This table Artikels various security measures, their descriptions, effectiveness ratings (based on a scale of 1 to 5, with 5 being the highest), and associated costs. Cost is a relative measure, encompassing development, implementation, and maintenance.
| Security Measure | Description | Effectiveness | Cost |
|---|---|---|---|
| Regular Security Audits | Systematic reviews of code, infrastructure, and security protocols | 4 | Medium |
| Input Validation and Sanitization | Scrutinizing user inputs to prevent malicious activity | 4 | Low |
| Secure Coding Practices | Training developers on secure coding practices | 5 | Medium |
| Multi-Factor Authentication (MFA) | Requiring multiple verification steps | 5 | Medium |
| Proactive Vulnerability Scanning | Using tools to identify vulnerabilities before exploitation | 4 | Medium |
| Security Awareness Training | Educating users on security threats | 3 | Low |
| Security Information and Event Management (SIEM) | Monitoring logs and detecting anomalies | 5 | High |
Robust Security Framework
A robust security framework consists of multiple layers and components working together to provide comprehensive protection.
Myspace bug alerts, while seemingly harmless, could potentially trigger some mischief. Thinking about staying safe in today’s connected world, especially with the rise of wimax technologies, is crucial. Staying safe in a wimax world requires understanding the potential risks, like these kinds of vulnerabilities, to protect yourself online. This highlights the importance of vigilance when dealing with these kinds of alerts.
A layered approach to security is crucial. Each layer provides a specific function, reinforcing the overall security posture.
This framework should encompass:
- Network Security: Firewalls, intrusion detection systems, and virtual private networks (VPNs) protect the network infrastructure from unauthorized access.
- Application Security: Secure coding practices, input validation, and regular security audits for applications prevent vulnerabilities.
- Data Security: Encryption, access controls, and data loss prevention (DLP) measures safeguard sensitive data.
- User Security: Multi-factor authentication, strong passwords, and user training are crucial to protect user accounts.
Real-World Examples of Similar Incidents
Social media platforms are susceptible to bugs that can have significant consequences, from minor inconveniences to major disruptions. Understanding how similar incidents have played out in the past helps us anticipate potential issues and develop robust strategies to mitigate their impact. Examining real-world examples reveals patterns in user and platform responses, highlighting the importance of swift and transparent communication during crises.
Social Media Platform Bug Incidents
Numerous social media platforms have faced bugs that caused considerable user disruption and reputational damage. Analyzing these incidents provides valuable insights into the challenges platforms face and the importance of proactive security measures. A critical examination of these incidents reveals crucial lessons that can inform future strategies.
Examples of Similar Incidents
| Platform | Incident Description | Impact on Users | Impact on Platform |
|---|---|---|---|
| In 2020, a bug caused a temporary disruption in the platform’s timeline display for some users, impacting their ability to see recent tweets and interact with others. This issue lasted for several hours before being resolved. | Users were unable to see the latest tweets and interact with their usual feeds, potentially disrupting communication and information dissemination. | Twitter experienced a significant drop in user activity and negative feedback during the outage. The incident highlighted the importance of reliable platform functionality for user engagement. | |
| In 2018, a bug affected the user account verification process, causing confusion and difficulty for users to access their accounts. Many users reported issues with account recovery and authentication. | Users experienced difficulties logging into their accounts, recovering passwords, and verifying their identities. This disrupted their ability to connect with friends and family. | Facebook faced negative publicity and user complaints regarding the security and reliability of its platform. The incident underscored the importance of robust account security and recovery procedures. | |
| In 2022, a bug prevented users from uploading photos and videos. This affected content creation and sharing capabilities for a substantial period. | Users were unable to share content, potentially hindering their ability to express themselves or participate in social interactions. This disruption could have affected influencers and businesses relying on Instagram for marketing. | Instagram suffered a decline in user activity and negative press coverage. The incident demonstrated the importance of platform stability for user satisfaction and engagement. |
Timeline of a Notable Social Media Bug Incident
This example focuses on a hypothetical Instagram bug that caused a global disruption in user access.
- 2023-10-26, 10:00 AM PST: Initial reports emerge from users across various regions indicating difficulty logging into their Instagram accounts. The initial reports were focused on a problem with login authentication, but other reports started to come in.
- 2023-10-26, 10:30 AM PST: Instagram’s support channels begin receiving a surge in user complaints. The reports from users were not isolated, but spread across all continents, demonstrating a large-scale problem. The company acknowledges the issue and initiates internal investigations.
- 2023-10-26, 11:00 AM PST: The Instagram engineering team identifies a critical bug in the user authentication system. The bug is related to an improperly configured cache.
- 2023-10-26, 12:00 PM PST: The engineering team implements a temporary fix to mitigate the impact of the bug. This fix allows users to log in.
- 2023-10-26, 1:00 PM PST: The Instagram team releases a full-scale update to resolve the root cause of the bug. This update fixes the cache issue. The team also publishes an official statement to apologize for the inconvenience and Artikel the steps taken to address the problem.
- 2023-10-26, 2:00 PM PST: Instagram begins to see a gradual return of users to the platform. The initial problems were related to authentication, but other parts of the platform were starting to work correctly.
Last Word
In conclusion, the potential for mischief stemming from bugs in MySpace-like social media platforms is substantial. Addressing these vulnerabilities requires a multi-faceted approach, combining proactive security measures with robust response mechanisms. By learning from past incidents and implementing best practices, platforms can safeguard user data and maintain trust. Ultimately, vigilance and a commitment to continuous improvement are key to preventing and mitigating the negative impacts of potential mischief.