Money Fuels Malware Mayhem
Report money makes malware world go round. This report delves into the dark underbelly of the digital world, exposing how financial incentives drive the creation, distribution, and evolution of malware. From ransomware demanding hefty payouts to sophisticated spyware harvesting data for sale, the motivations behind this malicious activity are complex and often intertwined with criminal organizations.
We’ll explore the intricate ecosystem supporting these operations, the various roles players fill, and the money laundering mechanisms used to hide illicit gains. Furthermore, we’ll analyze how the pursuit of profit shapes malware’s evolution, making it increasingly sophisticated and difficult to detect. Finally, the report concludes with potential countermeasures and predictions for the future of this ever-evolving threat.
Money’s Role in Malware
The digital underworld is driven by the same fundamental force as the physical one: money. Malware, in its various forms, is a lucrative business, fueling a complex ecosystem of creation, distribution, and exploitation. This isn’t just about individual hackers; it’s a sophisticated industry with organized crime groups and state-sponsored actors vying for profits.The motivation behind malware development is multifaceted, ranging from personal gain to national interests.
Financial incentives are a primary driver, attracting individuals and groups with diverse skill sets to this illicit market. The sheer volume of potential victims and the relative ease of entry into the cybercrime landscape further amplify the appeal.
Financial Motivations for Malware Creation
The primary financial motivations behind malware development are often intertwined and multifaceted. Criminals employ diverse strategies to maximize their profit, targeting various sectors and vulnerabilities. The value of stolen data, compromised systems, and extorted funds varies significantly based on the specific target and the malware type used.
- Ransomware is often driven by the immediate potential for large payouts. The attacker gains significant financial rewards by locking down systems and demanding ransom. This is often a direct financial motivation. Secondary motivations include data theft for later sale or use in blackmail operations. The notorious WannaCry ransomware attack, for instance, caused widespread disruption and significant financial losses for organizations.
That report about money fueling the malware world is pretty eye-opening. It highlights how financial incentives drive malicious actors. Interestingly, a recent study, study reveals Cisco’s strengths and weaknesses , sheds light on the cybersecurity landscape, and ultimately, how much money is at stake in the malware game. Ultimately, the financial motivation behind malware remains a key concern.
- Spyware, on the other hand, is motivated by the sale of collected data. This data includes sensitive information such as login credentials, financial details, and personal information. The value of this data depends on the target and the type of information gathered. This can be used to target individuals for phishing or other scams. It can also be used for more sophisticated activities, such as corporate espionage.
- Banking Trojans are designed to steal financial information, often in the form of credentials and transaction details. The motivation is the direct theft of money from victim accounts, and can be used for money laundering or for facilitating fraudulent transactions. Criminals often target high-value accounts, such as those belonging to businesses or wealthy individuals.
- Cryptojacking is a relatively newer form of malware. It leverages victims’ computers to mine cryptocurrency, generating revenue for the attacker. The profitability of this type of malware depends on the availability of computing power and the price of the cryptocurrency. While not as easily measurable as ransom demands, it can generate significant earnings over time.
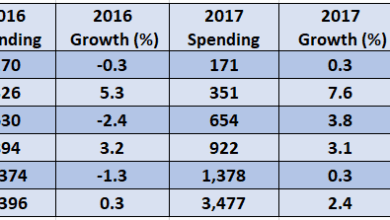
Profitability Comparisons
The profitability of different malware types varies greatly. Factors influencing this include the target market, the sophistication of the malware, and the level of security measures employed by potential victims. The cost of developing and distributing malware is also a crucial factor. For example, a well-crafted and targeted ransomware attack can yield substantial sums, while cryptojacking might require large-scale infection to achieve similar returns.
Malware Business Models
Malware actors employ various business models. Some operate as individual hackers, while others are part of organized criminal groups. These groups may have a dedicated team for development, distribution, and support. These models can vary from simple ransomware campaigns to complex operations with specialized teams and advanced tools.
| Malware Type | Primary Financial Motivation | Secondary Financial Motivation |
|---|---|---|
| Ransomware | Direct payment from victims | Data theft, blackmail |
| Spyware | Sale of stolen data | User harassment, identity theft |
| Banking Trojans | Direct theft of funds from accounts | Money laundering, facilitating fraudulent transactions |
| Cryptojacking | Mining cryptocurrency using victim’s resources | Compromising victim’s system for additional malicious activity |
The Malware Ecosystem
The digital underworld, a shadowy realm beneath the surface of the internet, thrives on a complex network of actors and systems. Malware isn’t created in isolation; it’s a product of a well-oiled, though illicit, economy. This ecosystem, built on interconnectedness and a constant flow of money, fuels the development, distribution, and exploitation of malicious software. Understanding this ecosystem is crucial to combating the growing threat.The malware economy isn’t a single entity; it’s a collection of individuals and groups, each playing a specific role in the overall operation.
From developers crafting sophisticated viruses to distributors spreading them, and money launderers masking the illicit profits, each element is essential to the ongoing cycle of malicious activity. This intricate web is sustained by a shared goal: to profit from the exploitation of vulnerabilities in the digital world.
Interconnectedness of Actors and Systems
The malware ecosystem is characterized by a high degree of interconnectedness. Developers, often located in various parts of the world, collaborate to create new malware strains, exploiting vulnerabilities and weaknesses in software. These strains are then distributed through compromised systems or malicious websites, further enabling the spread. Money laundering mechanisms are intricately woven into the process, enabling criminals to conceal their ill-gotten gains and reinvest in future attacks.
Malware Supply Chain
The supply chain supporting malware operations is surprisingly complex and sophisticated. This involves a network of actors responsible for different stages, from development and distribution to the ultimate exploitation. The following components are crucial:
- Malware Developers: These individuals or groups are responsible for crafting the malicious code, often leveraging vulnerabilities in existing software. Their expertise in programming and knowledge of cybersecurity weaknesses are critical to the success of the malware.
- Malware Distributors: These actors spread the malware to vulnerable systems, often through phishing emails, malicious websites, or compromised software. Their tactics frequently target individuals and organizations, exploiting their lack of security awareness.
- Infrastructure Providers: Malicious actors often rely on compromised servers and networks for distribution and control of the malware. These providers may not be aware of the illicit activity they are facilitating, adding another layer of complexity to the problem.
- Money Launderers: The proceeds from malware campaigns need to be laundered to appear legitimate. Money laundering networks employ various techniques, often involving complex financial transactions and multiple intermediaries, to conceal the origins of the money.
Roles in the Malware Ecosystem
The malware ecosystem encompasses a diverse range of roles. Each actor, from the initial developer to the final victim, plays a part in the overall process:
- Malware Developers: The architects and programmers behind the malicious code. They are often highly skilled and knowledgeable in cybersecurity, using their expertise to create sophisticated and evasive threats.
- Distributors: The individuals or groups who spread the malware to victims. Their techniques can range from simple spam campaigns to highly targeted attacks.
- Compromised System Owners: Unwittingly, owners of compromised systems become part of the infrastructure used to spread malware. These systems are frequently used as launching pads for further attacks.
- Money Launderers: They conceal the illicit proceeds of malware campaigns, making it difficult for law enforcement to trace the origin of the funds.
Money Laundering Mechanisms
Money laundering for malware proceeds frequently involves complex financial transactions and multiple intermediaries. These schemes aim to disguise the origin of the funds, making them appear legitimate. Cryptocurrencies are increasingly used due to their anonymity and decentralized nature. Methods include:
- Cryptocurrency Transactions: The use of cryptocurrencies allows for greater anonymity, making it harder to trace the flow of funds.
- Complex Financial Networks: Sophisticated financial networks are often employed, involving numerous accounts and transactions to obscure the trail of money.
- Shell Companies: The use of shell companies, or other anonymous entities, can mask the true owners of the money.
Anonymity and Privacy
Anonymity and privacy are crucial components of the malware ecosystem. They allow actors to operate with relative impunity, making it difficult to trace their activities. The use of proxy servers, encrypted communication channels, and anonymity networks, like Tor, are key components in maintaining this anonymity.
Diagram of the Malware Ecosystem
A diagram illustrating the malware ecosystem would visually represent the interconnectedness of the actors and systems. The diagram would include developers, distributors, infrastructure providers, compromised systems, and money launderers, connected by arrows indicating the flow of malware and money. A crucial aspect of the diagram would be highlighting the various stages of the malware lifecycle, from creation to distribution to exploitation.
Further, the diagram would emphasize the anonymity networks used to conceal the actors’ identities.
The Impact of Money on Malware Evolution: Report Money Makes Malware World Go Round
The relentless pursuit of profit fuels the continuous evolution of malware. Malware authors, driven by financial incentives, are constantly adapting their creations to stay ahead of security measures. This relentless cycle of adaptation and counter-adaptation shapes the ever-changing threat landscape. Understanding the financial motivations behind malware development is crucial to effectively combating this evolving threat.The financial incentives driving malware development are multifaceted.
From ransomware demanding cryptocurrency payments to botnets generating revenue through spam campaigns, profit motivates the creation and maintenance of malicious software. The profitability of different malware types fluctuates depending on factors like market demand, security response, and technological advancements.
Reports consistently show that money fuels the malware world. It’s a sad truth, but the development and distribution of malicious software are often driven by profit. This is a stark contrast to the innovation in the tech world, like AMD’s groundbreaking move with their first chipset featuring ATI graphics, amd launches first chipset with ati graphics.
While advancements like these improve computing capabilities, the dark side of the tech world continues to be fueled by financial incentives, unfortunately.
Profit-Driven Development and Adaptation
Malware authors are motivated by financial gain. This drives constant development and adaptation, often mirroring the software development lifecycle. New features, enhanced evasion techniques, and targeted attacks are developed to exploit vulnerabilities in the latest security measures. The goal is to maximize profits, and this fuels the ongoing arms race between malware authors and security researchers.
Methods for Staying Ahead of Security
Malware authors employ various methods to circumvent security measures. These include obfuscation techniques to complicate code analysis, polymorphism to change the malware’s structure, and metamorphic techniques to drastically alter the malware’s appearance with each infection. Furthermore, using advanced techniques like steganography to hide malware within seemingly innocuous files adds an additional layer of complexity. This constant adaptation ensures that the malware remains undetected for as long as possible.
Examples of Evasion Techniques
Malware authors frequently utilize techniques that evade detection by antivirus software. One example is the use of packers to obscure the malware’s code, making it difficult for analysis tools to understand its functionality. Another tactic involves encrypting the malware’s code, rendering it unreadable to traditional analysis methods. Polymorphic malware, capable of altering its code structure with each infection, further complicates detection efforts.
Advanced evasion techniques make it harder to identify malware, prolonging the infection period and maximizing profit.
Reports consistently show how much money fuels the malware world. It’s a vicious cycle, and the drive for profit often pushes developers to create new ways to exploit vulnerabilities. This is clearly illustrated by how Kazaa pulls Skype voice into p2p sharing, kazaa pulls skype voice into p2p , demonstrating how ingenious hackers can leverage existing technology for malicious gain.
Ultimately, the constant push for profit keeps the malware industry alive and well.
Impact on the Malware Landscape
Financial pressures shape the malware landscape in significant ways. The profitability of specific malware types influences the resources allocated to their development and deployment. For instance, ransomware’s high profitability attracts more authors and resources, leading to a surge in ransomware attacks. The financial rewards also drive the creation of new and more sophisticated malware types. Competition among malware authors pushes the boundaries of sophistication, requiring continuous innovation in both malware development and security countermeasures.
Regional Variations in Malware Evolution, Report money makes malware world go round
The evolution of malware varies across different regions. Factors such as regulatory environments, technological infrastructure, and cultural norms play a role in shaping the types of malware prevalent in specific regions. For instance, regions with less robust cybersecurity infrastructure may see a higher prevalence of ransomware and other types of destructive malware. Additionally, the prevalence of specific payment methods or targeted user demographics can influence the malware types used.
In summary, understanding the specific context and dynamics of different regions is crucial for developing effective regional strategies against malware.
Techniques to Improve Malware Profitability
- Targeted attacks: Focusing on specific vulnerabilities within particular industries or organizations allows malware authors to maximize the impact of their attacks and the potential for financial gain.
- Advanced evasion techniques: Developing sophisticated methods to evade detection by security software is crucial for prolonging the infection period and increasing the likelihood of successful data breaches or financial exploitation.
- Improved payload delivery: Effective delivery mechanisms ensure that the malware reaches its target, maximizing the chance of successful infection and subsequent exploitation.
- Advanced encryption techniques: Employing strong encryption methods helps to conceal the malware’s activity, protecting it from analysis and ensuring data remains encrypted until payment is received.
- Cryptocurrency integration: Using cryptocurrency makes transactions more difficult to trace, enhancing the anonymity and profitability of the attacks.
Countermeasures to Financial Malware Incentives
Financial malware thrives on the lucrative ecosystem it creates. Disrupting these financial flows is crucial to weakening the entire operation. This involves a multi-pronged approach targeting the malware’s financial incentives, the individuals behind it, and the infrastructure that supports it. Ultimately, the goal is to make malicious activity less profitable, thereby reducing the appeal of this criminal enterprise.The key to combating financial malware is understanding its motivations and then attacking those motivations.
This means focusing on disrupting the financial mechanisms that support malware operations, enhancing cybersecurity practices, engaging international cooperation, and leveraging the power of law enforcement. Stronger countermeasures can make the risks associated with financial malware significantly higher than the rewards.
Disrupting Financial Flows
Disrupting the financial flows supporting malware operations is a complex but vital strategy. This includes tracing and freezing the assets of individuals and organizations involved in the creation, distribution, and use of malware. Cryptocurrency mixing services, anonymization tools, and other financial mechanisms that facilitate illicit transactions are also critical targets. Effective strategies will require close cooperation between law enforcement agencies and financial institutions.
The recent rise of ransomware attacks, for instance, highlights the need for sophisticated tools to identify and track the illicit financial flows behind these attacks.
Strengthening Cybersecurity Practices
Strong cybersecurity practices are paramount in preventing malware infections. These practices include regular software updates, robust antivirus protection, employee training on phishing and social engineering tactics, and multi-factor authentication. Companies and individuals should adopt a proactive security posture, not just reacting to attacks. A culture of cybersecurity awareness and vigilance within organizations is critical to mitigate risks.
Implementing security information and event management (SIEM) systems can enhance the detection and response capabilities to malicious activities.
Role of Law Enforcement
Law enforcement plays a critical role in disrupting malware operations. This includes investigations into the developers, distributors, and users of malware, as well as the seizure of infrastructure and assets used in the attacks. International cooperation is essential in tracking and apprehending perpetrators across borders. Law enforcement agencies must stay ahead of evolving malware tactics and adapt their investigative strategies accordingly.
The successful prosecution of cybercriminals serves as a deterrent to future attacks.
Importance of International Cooperation
International cooperation is crucial in combating malware. This involves sharing information about malware threats, coordinating investigations across borders, and establishing international legal frameworks to prosecute cybercriminals. Global collaboration is essential to disrupt the complex networks that support malware operations. The global nature of the internet demands a global response to address the global problem of malware.
Table of Countermeasures
| Countermeasure | Description | Effectiveness |
|---|---|---|
| Law Enforcement | Investigations, asset seizures, prosecutions, international cooperation | High, but dependent on resources and international coordination |
| Security Practices | Regular updates, robust antivirus, employee training, multi-factor authentication | High, but only as effective as the level of implementation |
| Financial Sanctions | Freezing assets of individuals and organizations involved in malware activities | High potential, but requires international coordination |
| Cybersecurity Information Sharing | Sharing threat intelligence between organizations and governments | High, facilitating proactive threat detection and response |
| International Legal Frameworks | Developing and enforcing international laws against cybercrime | High, but requires global consensus and enforcement |
The Future of Money-Driven Malware

The digital landscape is constantly evolving, and with it, so too are the tactics and techniques employed by malicious actors seeking financial gain. Understanding the trajectory of money-driven malware requires an examination of emerging technologies and their potential for exploitation. This exploration will delve into predicted trends, the influence of emerging technologies, potential vulnerabilities, and forecasts for future financial incentives.The future of malware is inextricably linked to the ongoing development and adoption of new technologies.
Financial incentives for malicious actors will continue to be a powerful driver, leading to the adaptation of these technologies to create increasingly sophisticated and effective attacks.
Potential Trends in Malware Development and Distribution
The rise of decentralized finance (DeFi) and the growing popularity of cryptocurrency have opened new avenues for malicious actors. Ransomware targeting DeFi platforms or smart contracts could become more prevalent, potentially disrupting entire financial ecosystems. Sophisticated phishing campaigns designed to exploit vulnerabilities in decentralized applications (dApps) could also proliferate, tricking users into divulging sensitive financial information.
Role of Emerging Technologies in Shaping Malware
Artificial intelligence (AI) and machine learning (ML) are transforming malware development. AI-powered malware can adapt more quickly to evolving security measures, making detection and prevention more challenging. The use of AI for automating malicious activities, like phishing campaigns and DDoS attacks, could significantly increase the scale and impact of these attacks.
Potential Vulnerabilities in Emerging Financial Technologies
Decentralized finance (DeFi) protocols often rely on complex smart contracts, which are vulnerable to vulnerabilities known as exploits. Malicious actors could potentially exploit these vulnerabilities to steal cryptocurrency or manipulate financial markets. A lack of regulatory oversight in the rapidly growing DeFi space presents a significant vulnerability. The lack of centralized control and auditing mechanisms makes identifying and addressing these vulnerabilities difficult.
Examples of Exploitation of New Technologies
One example of exploitation is the use of AI-powered chatbots to conduct elaborate phishing attacks. These bots can mimic human conversation, making them incredibly effective at tricking users into revealing sensitive information. Another example is the use of deepfakes to create convincing impersonations for fraudulent activities, such as accessing accounts or initiating transactions.
Forecast for Future Financial Incentives Driving Malware
The financial incentives driving malware will likely continue to evolve alongside the development of new technologies. The value of cryptocurrency, and the potential for financial gain through illicit activities like theft and manipulation, will remain a powerful motivator for attackers. Additionally, the rise of the gig economy and remote work could lead to targeted attacks against individuals’ financial accounts and sensitive information.
Ending Remarks

In conclusion, the report money makes malware world go round highlights the critical link between financial gain and malicious software. The intricate interplay of actors, motivations, and evolving techniques makes combating this threat a complex and multifaceted challenge. Understanding the financial drivers is crucial to developing effective countermeasures, ranging from enhanced cybersecurity practices to international cooperation and law enforcement efforts.
The future of malware will likely be shaped by emerging technologies, making it essential to stay ahead of the curve in the fight against this persistent threat.