Technology Quiz How Does Email Disappear?
Technology quiz how does e mail disappear – Technology quiz: How does email disappear? This exploration delves into the surprising ways emails vanish, from accidental deletions to more sinister scenarios. We’ll dissect different email deletion methods, examine the likelihood of recovery, and analyze the role of email providers in securing our digital correspondence. Understanding these processes is crucial for safeguarding our important messages and preventing data loss.
From simple user errors to complex technical issues, this deep dive will cover a variety of situations where email messages vanish. We will look at how different email clients handle deletion, compare the approaches of major providers, and highlight the potential challenges of recovering lost emails. We’ll also examine the security implications of various deletion methods and discuss best practices for email privacy.
Email Deletion Methods

Email deletion, while seemingly straightforward, involves nuances that impact storage and data recovery. Understanding the different methods of deleting emails, the implications on storage, and the variations between email providers is crucial for managing your inbox effectively. Email providers employ various approaches to handling deleted items, from temporary storage in a trash folder to permanent removal from your account.Email deletion isn’t a simple “erase” function; it often involves several steps and considerations.
Different email clients and services offer different options and procedures, requiring a degree of understanding to ensure complete and secure removal of unwanted messages.
Email Deletion Methods: A Deep Dive
Email providers utilize distinct methods for handling email deletion. These vary from temporary storage in a “trash” or “deleted items” folder to immediate, irreversible removal. Permanent deletion, while often desired, involves an additional step of emptying the designated trash or deleted items folder.
Email Deletion Steps: Emptying the Trash
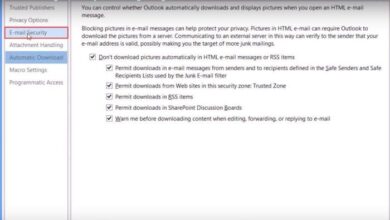
Different email clients and services utilize different trash or deleted items folders. These folders are designed for temporary storage of deleted emails, allowing for recovery if needed. Emptying these folders permanently removes the emails from the system, freeing up storage space and preventing accidental recovery. Steps for emptying the trash vary based on the client. For instance, in Gmail, you’d find the trash folder in your inbox and can select the “Empty Trash” option.
In Outlook, the “Empty Deleted Items” command is typically found in the Deleted Items folder’s menu.
Permanently Deleting Emails and Storage Implications
“Permanently deleting” emails doesn’t mean immediate erasure from all servers. It typically means removal from your accessible folders and the user’s temporary storage. Email providers maintain data backups and redundancy for a certain period for recovery purposes. While the email is unavailable to the user, it might still exist in backups for a specified time, depending on the service provider’s policies.
The implications for storage depend on the provider’s policies, the size of the deleted emails, and the user’s storage plan.
Email Service Provider Approaches to Deletion
Email service providers differ in their approach to email deletion. Gmail, for example, utilizes a “trash” folder where deleted emails are temporarily stored, allowing for retrieval. Outlook and Yahoo Mail, on the other hand, use a “deleted items” folder with similar functionality. These differences are often reflected in the available options within the email client’s interface.
Ever wondered how an email vanishes? It’s a fascinating tech quiz question, right? While we ponder the digital mysteries of email deletion, it’s worth noting that Microsoft’s Vista, set to sail here , is bringing a whole new wave of operating system features. But back to our email mystery: what happens to those deleted messages?
They’re often just marked as gone, not truly erased, leaving the question of email disappearance quite intriguing.
User Settings and Email Deletion
User settings often play a significant role in how emails are deleted and managed. These settings may include the ability to set specific deletion times, preferences for automatic archiving, and the frequency for emptying the trash or deleted items folder. By adjusting these settings, users can tailor their email management experience to meet their specific needs.
Comparison of Email Client Deletion Methods
| Email Client | Deletion Methods | Permanent Deletion | Trash/Deleted Items |
|---|---|---|---|
| Gmail | Delete, Move to Archive | Empty Trash | Trash Folder |
| Outlook | Delete, Move to Archive | Empty Deleted Items | Deleted Items Folder |
| Yahoo Mail | Delete, Move to Archive | Empty Deleted Items | Deleted Items Folder |
Data Recovery After Email Deletion
Recovering deleted emails is a common concern for many users. While complete recovery is not always guaranteed, understanding the factors that influence recovery chances can be crucial. This section delves into the potential for retrieving lost messages and the challenges involved.Email providers and operating systems employ various methods for handling email deletion. These methods, along with user actions, significantly impact the likelihood of data recovery.
The effectiveness of recovery tools also plays a crucial role, but it’s essential to acknowledge that no tool guarantees a perfect outcome.
Likelihood of Recovering Deleted Emails
The chances of recovering deleted emails depend heavily on the specific deletion method and the actions taken after deletion. Immediate actions, like emptying the trash or permanently deleting messages, significantly reduce the chances of retrieval. Conversely, actions that retain data for a longer period, such as moving emails to an archive, offer a higher likelihood of recovery.
Impact of Deletion Methods on Data Recovery
Different email deletion methods affect recovery potential in varying degrees. For instance, emptying the trash often marks data for immediate overwrite, drastically reducing the possibility of retrieval. Moving emails to an archive folder, on the other hand, might still leave the data accessible under certain circumstances, provided the user has the necessary tools or the archive system has not overwritten the files.
Email Recovery Tools and Their Effectiveness
Email recovery tools are software applications designed to help retrieve deleted emails. These tools can sometimes access data that the user’s system or email provider has not overwritten. Their effectiveness depends on the specific tool, the deletion method used, and the time elapsed since deletion. Tools often work best when used promptly after the deletion. They may not be able to recover data that has been permanently overwritten.
Common Data Recovery Strategies
Various strategies can be employed for recovering deleted emails. One common approach involves checking the trash or deleted items folder. Another involves using email recovery tools. These tools often employ specialized techniques to access and retrieve data from various storage locations. It is important to remember that data recovery is not a foolproof process.
Potential Challenges in Recovering Deleted Emails
| Deletion Method | Recovery Likelihood | Challenges |
|---|---|---|
| Emptying Trash | Low | Data is often irrecoverable, as it’s typically overwritten quickly. |
| Moving to Archive | Medium | Recovery might depend on the archive’s settings and the email provider’s policies. Specific tools might be necessary. |
| Using Delete Function | Medium | Data might still be recoverable for a limited time, depending on the system’s storage mechanisms. The chance of recovery decreases as time passes. |
Email Privacy and Security in Deletion
Email deletion, while seemingly straightforward, carries significant security implications. Understanding these nuances is crucial for maintaining the privacy of your data and preventing unauthorized access. This section delves into the security considerations surrounding email deletion methods, the role of email service providers, and best practices for protecting your emails.Email service providers employ various strategies for managing and deleting emails.
These strategies directly impact the security and recoverability of data. The methods employed vary, and understanding these methods is critical for managing your data security effectively.
Security Implications of Deletion Methods, Technology quiz how does e mail disappear
Different email deletion methods have varying security implications. Permanent deletion, for example, often involves overwriting the data multiple times to ensure it cannot be recovered. Soft deletion, on the other hand, typically moves the email to an archive or trash folder, making it retrievable for a specified period. The security implications are linked to the potential for data recovery, whether intentional or accidental.
Ever wondered how an email vanishes? It’s a fascinating tech quiz question, right? Modern anti-spyware solutions, like those available on the new enterprise marketplace for anti spyware protection, enterprise new marketplace for anti spyware protection , are increasingly important in safeguarding data. Knowing how these programs work gives a good insight into the complex ways digital messages can be managed and, ultimately, disappear.
So, the next time you tackle that technology quiz, you’ll have a more informed answer about email disappearance.
The risk of unauthorized access and the potential for data breaches increase when recovery options are available.
Role of Email Service Providers in Data Security
Email service providers (ESPs) play a crucial role in data security during the deletion process. They implement security measures to protect user data, including encryption and access controls. Robust encryption protocols ensure data confidentiality during transit and storage. Access controls limit user access to specific data sets, minimizing the risk of unauthorized access. ESPs should clearly communicate their data handling policies and deletion procedures.
Ensuring Secure Deletion Practices
Implementing secure deletion practices is essential to minimize the risk of data breaches. Users should be aware of the different deletion options offered by their ESP and choose the method best suited to their needs. Regularly reviewing and updating security settings, including account recovery options, is recommended. Using strong passwords and enabling two-factor authentication adds another layer of protection.
Comparison of Security Features for Email Accounts
Different email accounts offer varying security features. Some accounts include features like data encryption, while others may emphasize robust spam filters. The features and capabilities of the email account should be carefully considered in relation to the user’s specific security needs. A comprehensive security strategy should include both the features provided by the ESP and the user’s personal security measures.
Best Practices for Protecting Emails from Unauthorized Access
Protecting emails from unauthorized access involves a multi-faceted approach. Strong passwords, enabled two-factor authentication, and regularly updated security settings are essential. Users should also be vigilant about phishing attempts and suspicious links or attachments. Implementing these measures helps maintain data security and integrity.
Measures for Ensuring Email Privacy During Deletion
Maintaining email privacy during deletion requires a comprehensive approach. Regularly reviewing and understanding the deletion policies of your email provider is crucial. Choosing appropriate deletion methods based on your data sensitivity is essential. Using strong passwords and enabled two-factor authentication adds another layer of security to your email account. Adhering to these measures minimizes the risk of unauthorized access and data breaches.
Email Storage and Deletion Policies: Technology Quiz How Does E Mail Disappear
Email providers are constantly evolving their services, and understanding how they manage storage and delete emails is crucial for responsible email usage. This section dives into the specifics of how different platforms handle email storage, the role of policies in this process, and the mechanisms they use for deletion.Email providers have different strategies for managing user data, especially in the realm of email.
This is a reflection of the vast spectrum of storage capabilities and business models within the industry. Different storage policies are employed to maintain efficiency and meet diverse user needs. These policies are not arbitrary; they’re carefully designed to balance the need for accessibility and security with the realities of data management.
Email Storage Space Management
Email providers employ various strategies to manage storage space. Some providers offer unlimited storage, while others impose limits and charge for additional space. These limits can be flexible or fixed, depending on the specific provider and the chosen plan. This approach to storage is essential for maintaining system performance and scalability, as it directly impacts the infrastructure requirements for managing and retrieving user data.
The strategies employed for storage space management are also influenced by factors like user growth projections, anticipated data volume, and technical constraints.
Ever wondered how an email vanishes? It’s a fascinating tech quiz question, right? Well, similarly, the demise of the PC industry is a fascinating case study, like how Jack and Steve at Apple, how Jack er Steve killed the giant before exiting the PC business , changed the game. Ultimately, understanding the complexities of digital disappearance, like deleted emails, is linked to understanding these historical shifts in technology.
So, next time you ponder the fate of an email, think about how entire industries can fade away.
Role of Storage Policies in Email Management
Storage policies play a vital role in email management. They dictate how emails are stored, organized, and potentially archived. This structured approach helps to optimize storage space and ensure efficient retrieval of information. Clear storage policies enable seamless access to emails, reducing the risk of data loss and improving the overall user experience. These policies also help to manage user expectations regarding the longevity and accessibility of their data.
Furthermore, they contribute to the provider’s overall business strategy and profitability.
Email Provider Deletion Policies
Email providers utilize a range of mechanisms for implementing deletion policies. These policies typically involve a combination of temporary storage, scheduled purging, and permanent removal. Temporary storage allows for a specific retention period, enabling users to retrieve deleted emails within a defined timeframe. Scheduled purging refers to the automatic removal of emails after a certain period. Permanent removal, on the other hand, signifies the complete and irreversible deletion of emails from the system.
Providers often offer user-controlled options for managing their deletion preferences, allowing for more personalized management of email data.
Storage Policies for Different Email Providers
Unfortunately, a comprehensive list of storage policies for all email providers is not readily available in a standardized format. Each provider’s policy is usually detailed in their terms of service or help documentation. This makes a universally accessible table difficult to create. However, users can typically find information about storage limits, retention periods, and deletion options on the provider’s support pages.
Comparison of Storage and Deletion Policies
Comparing and contrasting the storage and deletion policies of different email providers is complex, given the diversity of offerings. Some providers might offer generous storage allowances, while others might charge for exceeding a certain limit. Retention periods vary significantly, with some providers allowing for a relatively long time before automatically deleting emails, and others having very short retention periods.
The specific mechanisms for email deletion also differ. Ultimately, users need to carefully review the policies of the providers they choose to use to make informed decisions about their email management needs.
Case Studies on Email Disappearance
Email disappearance, whether due to user error, technical glitches, or malicious intent, can have significant consequences. Understanding these cases helps us identify potential vulnerabilities and develop better strategies for email management and security. This section delves into various scenarios of email loss and highlights the importance of proactive measures to prevent such incidents.
Examples of Email Disappearance Incidents
Several instances of email disappearance have been reported, often involving significant data loss. While specific details are omitted to protect privacy, these cases underscore the need for robust email management practices. These cases demonstrate the vulnerability of email systems to a variety of factors, from accidental deletion to sophisticated cyberattacks.
Email Loss Due to User Error
User error is a frequent cause of email loss. Accidental deletions, misconfigured settings, and failing to properly archive important correspondence can lead to significant repercussions. For example, a project manager losing crucial client communication can result in delays, financial losses, and damage to professional relationships. The consequences of such errors are often far-reaching and can be avoided with careful attention to detail and the use of backup systems.
Consequences of Improper Email Management
Improper email management practices can have profound effects on individuals and organizations. This includes not only the loss of important information but also the disruption of workflows, damage to reputations, and even legal repercussions. For example, a company losing customer records due to poor email organization could face significant fines or lawsuits. Effective email management, therefore, is critical for maintaining productivity, security, and compliance.
Different Scenarios of Email Disappearance and Their Implications
Email disappearance can manifest in various forms, each with its own implications. These scenarios range from simple accidental deletions to more complex incidents involving server issues, malicious activity, or even data breaches. The implications can be as varied as temporary inconvenience to irreversible data loss, affecting individuals and businesses alike.
Table Summarizing Case Studies
| Scenario | Cause | Effect |
|---|---|---|
| Accidental Deletion of Client Contracts | User error (misplaced folder, mistaken delete command) | Loss of vital contractual information, potential legal issues, disruption of project timelines, and reputational damage. |
| Temporary Email Unavailability Due to Server Maintenance | Technical problem (scheduled server maintenance) | Interruption of communication, potential delays in project completion, and customer service disruptions. |
| Email Account Compromise Leading to Data Breach | Malicious activity (phishing, malware infection) | Exposure of sensitive information (personal or corporate), financial losses, reputational damage, and potential legal action. |
Final Summary

In conclusion, email disappearance, whether intentional or accidental, highlights the need for careful email management. Understanding how emails are deleted, the potential for recovery, and the security implications is key to protecting our digital archives. By understanding these complexities, we can better protect our valuable information and avoid costly mistakes. This technology quiz has provided a comprehensive overview of the topic, leaving you with a deeper understanding of how emails vanish and how to safeguard your digital correspondence.