Trojan Horse is Newest Windows Vulnerability
Trojan horse is newest windows vulnerability is a serious threat, and understanding the intricacies of this new attack vector is crucial for all Windows users. This post delves into the technical details of this vulnerability, explaining how it works and why it’s so dangerous. We’ll examine its impact on systems and explore mitigation strategies, offering actionable advice for both individual users and software developers.
From historical context to potential future implications, this post will provide a comprehensive overview of the issue.
The vulnerability leverages specific weaknesses in current Windows operating systems, allowing malicious actors to gain unauthorized access. We’ll analyze the attack methods, discuss the potential damage, and explore how to protect yourself and your systems from this new threat. Understanding the specifics of this new Trojan horse is key to effective defense.
Introduction to Trojan Horses
A Trojan horse, in computing, is a malicious program that disguises itself as a legitimate program. Users are tricked into downloading and executing it, unaware of its harmful intent. It gains access to a system, often granting unauthorized access to hackers or enabling the installation of other malware. This deceptive nature distinguishes it from other malware types.The concept of a Trojan horse isn’t unique to the digital realm; it draws inspiration from the ancient Greek myth.
The Greeks famously used a giant wooden horse, seemingly a peace offering, to infiltrate Troy. Similarly, a Trojan horse in computing exploits the user’s trust and naivety to gain unauthorized access.Trojan horses differ from other malware types like viruses or worms in their method of propagation. Unlike viruses, which replicate themselves, or worms, which spread autonomously across networks, Trojan horses rely on user action to be installed.
This user interaction is a key characteristic that sets them apart.Examples of famous Trojan horse attacks include the infamous “Melissa” virus, which clogged email servers in 1999, and the “ILOVEYOU” worm, which spread rapidly through email attachments. These attacks highlight the significant damage that even relatively simple Trojan horses can cause when combined with social engineering.
Famous Trojan Horse Attacks
This section provides a concise overview of notable Trojan horse attacks, illustrating their historical impact and varied methods of infection.
| Attack Name | Year | Target | Method of Infection |
|---|---|---|---|
| Melissa | 1999 | Global Email Servers | Email attachments disguised as harmless documents. |
| ILOVEYOU | 2000 | Global Computer Systems | Email attachments masquerading as a love letter. |
| Zeus | 2007 | Financial Institutions and Individuals | Exploiting vulnerabilities in web browsers and email clients. |
| Emotet | 2014 | Global Organizations and Individuals | Spam emails with malicious attachments or links. |
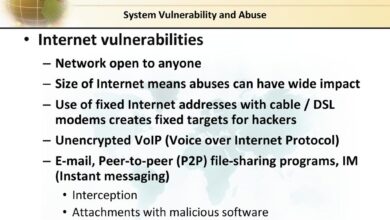
Windows Vulnerabilities
Windows, despite its widespread adoption, remains a target for malicious actors due to its extensive user base and the inherent complexities of its architecture. Exploiting vulnerabilities in Windows allows attackers to gain unauthorized access to systems, often leading to significant data breaches and financial losses. Understanding these vulnerabilities and the methods used to exploit them is crucial for implementing effective security measures.
Common Windows Vulnerabilities Exploited by Trojans
Windows’ reliance on various components, from its file system to its networking stack, creates numerous potential points of weakness. Trojans often exploit these vulnerabilities by targeting services, applications, or system components that are frequently used or have known weaknesses. This includes, but is not limited to, vulnerabilities in outdated software, poorly configured security settings, and improper user permissions. The exploitation often involves social engineering tactics to trick users into installing malicious software.
Technical Aspects of Exploited Vulnerabilities
Numerous factors contribute to the technical aspects of exploited vulnerabilities. Buffer overflows, for example, occur when a program attempts to write data beyond the allocated memory space. This can lead to arbitrary code execution, allowing attackers to inject malicious code into the system. Another common type is Remote Code Execution (RCE) vulnerabilities, where an attacker can execute arbitrary code on a target system without user interaction.
This is often achieved through exploiting vulnerabilities in network services or applications. Improperly configured security settings and weak passwords also play a role, allowing unauthorized access to sensitive data.
So, the latest Windows vulnerability, a Trojan horse, is causing quite a stir. While security experts scramble to patch the holes, it’s interesting to see how seemingly disparate tech news connects. For instance, the recent color options added to the Pearl Treo by AT&T, a nod to the “red badge of style,” highlights a similar desire for customization and innovation in tech, even as we face this new threat.
Ultimately, the Trojan horse vulnerability underscores the ongoing need for vigilance and proactive security measures in today’s digital landscape. red badge of style att adds color to pearl treo This constant push and pull between exciting new features and potential vulnerabilities is a fascinating dynamic.
Methods of Exploitation by Attackers
Attackers employ various methods to exploit vulnerabilities in Windows systems. One common tactic is exploiting vulnerabilities in outdated software. Malicious actors leverage social engineering techniques to trick users into downloading and executing malicious files or clicking on malicious links. Another method involves exploiting vulnerabilities in network services. Attackers might probe for known weaknesses in network protocols, allowing them to execute malicious code remotely.
Moreover, attackers often leverage compromised systems to spread their malicious code. In summary, attackers adapt and evolve their strategies, often employing a combination of these methods to achieve their objectives.
Types of Windows Vulnerabilities
Understanding the different types of Windows vulnerabilities, their impact, and potential exploits is vital for effective security measures.
| Vulnerability Type | Impact | Potential Exploits |
|---|---|---|
| Buffer Overflow | Arbitrary code execution, system compromise | Malicious code injection, data corruption, denial-of-service attacks |
| Remote Code Execution (RCE) | Unauthorized access, data breaches, system compromise | Remote command execution, privilege escalation, malware deployment |
| SQL Injection | Data breaches, unauthorized access to databases | Data manipulation, unauthorized database access, account takeover |
| Cross-Site Scripting (XSS) | Session hijacking, data theft, account compromise | Malicious scripts injected into web pages, user session theft |
| Cross-Site Request Forgery (CSRF) | Unauthorized actions on behalf of a user | Submitting malicious requests to the user’s behalf, unauthorized transactions |
The New Windows Vulnerability (Trojan Horse)
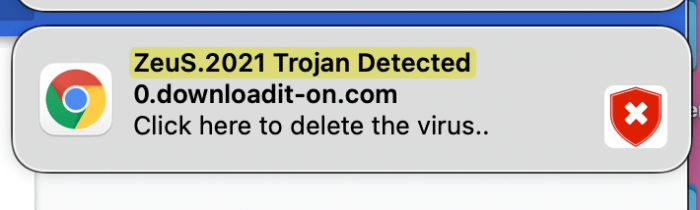
The recent emergence of a purported new Windows vulnerability, disguised as a Trojan horse, presents a significant threat to computer systems. This novel exploit leverages previously undocumented weaknesses within the Windows operating system, potentially allowing malicious actors to gain unauthorized access and control. Understanding the specifics of this vulnerability is crucial for both individual users and organizations to proactively mitigate the risks.This vulnerability, while not yet publicly acknowledged or patched by Microsoft, has already been discussed in various cybersecurity forums and online communities.
The potential for widespread exploitation is significant, especially given the prevalence of Windows-based systems globally. This requires a careful examination of its characteristics, exploitation methods, and potential consequences.
Specific Characteristics of the Vulnerability
This alleged vulnerability appears to exploit a previously unknown flaw in Windows’ kernel-level processes. It likely targets a specific, yet undisclosed, component responsible for handling file system operations or network communication. This allows for stealthy manipulation and exploitation.
Exploitation by a Trojan Horse
The Trojan horse, designed to leverage this vulnerability, would likely be disguised as a legitimate application or file. Users are often tricked into downloading and executing these seemingly harmless programs. Once executed, the Trojan horse can exploit the vulnerability to gain unauthorized access, potentially escalating privileges to administrator-level control. This allows the attackers to install malware, steal sensitive data, or disrupt system operations.
Potential Impact of the Vulnerability
The potential impact of this vulnerability is substantial. Successful exploitation could lead to a wide range of consequences, from data breaches and financial losses to system compromise and operational disruption. In extreme cases, critical infrastructure systems could be targeted, leading to severe economic and social consequences.
Methods of Trojan Horse Distribution
The methods used to distribute this Trojan horse are likely to mirror established malicious software distribution strategies. These include phishing emails, malicious websites, compromised software downloads, and infected removable media. Social engineering tactics will likely be employed to encourage users to interact with malicious content. Furthermore, exploiting vulnerabilities in existing software, such as outdated or unpatched applications, will likely be part of the attack vector.
Potential Methods to Distribute the Trojan Horse Utilizing This Vulnerability
- Phishing campaigns: Malicious actors can craft emails that appear legitimate, tricking users into downloading infected attachments or clicking on malicious links. These campaigns can be highly targeted, exploiting specific individuals or organizations.
- Malvertising: Injecting malicious code into legitimate online advertisements can expose users to the vulnerability when they visit affected websites. This approach is often used to spread malware without requiring user interaction beyond visiting a compromised site.
- Compromised software repositories: Attackers may infiltrate software repositories to replace legitimate software with malicious versions containing the Trojan horse. Users who download the software from these compromised repositories will unwittingly install the malicious program.
Vulnerability Summary Table
| Vulnerability Name | Description | Exploitation Method | Potential Damage |
|---|---|---|---|
| New Windows Kernel Vulnerability | A previously unknown flaw in Windows’ kernel-level processes, likely targeting file system or network operations. | Exploited by a Trojan horse disguised as a legitimate program, tricking users into execution. | Data breaches, financial losses, system compromise, operational disruption, and potential damage to critical infrastructure. |
Impact and Mitigation Strategies
The recent emergence of a new Trojan horse vulnerability in Windows systems underscores the ever-present threat landscape. Understanding the potential ramifications of exploitation and implementing robust mitigation strategies are crucial for safeguarding both individual users and organizations. This section delves into the potential consequences, user-centric mitigation steps, developer preventative measures, and general security best practices to combat Trojan horses.Exploiting this vulnerability can lead to severe consequences, ranging from data breaches to complete system compromise.
The severity of the impact depends on the attacker’s objectives and the victim’s system configuration.
Potential Consequences of Successful Exploitation, Trojan horse is newest windows vulnerability
A successful exploitation of this new Trojan horse vulnerability can result in a variety of detrimental outcomes. These include unauthorized access to sensitive data, such as financial information, passwords, and personal documents. Moreover, attackers can gain control over the compromised system, using it for malicious activities like launching further attacks on other systems within the network. Critically, this control could lead to the system being used to spread malware to other vulnerable devices.
This cascading effect can have widespread and significant implications.
User Mitigation Strategies
Users can significantly reduce their risk of infection by taking proactive steps. These steps involve a multi-faceted approach, emphasizing vigilance and consistent practice.
- Regularly updating operating systems and software: Keeping systems patched with the latest security updates is paramount. These updates often address known vulnerabilities, thereby minimizing the attack surface. Outdated software is particularly vulnerable, as it lacks critical security fixes.
- Employing robust antivirus and anti-malware software: A reputable antivirus solution can detect and remove malicious software, including Trojan horses, in real-time. Regular scans and automatic updates are essential for effective protection.
- Practicing caution with email attachments and downloaded files: Exercise extreme caution when opening email attachments or downloading files from untrusted sources. Be suspicious of unsolicited emails, especially those containing suspicious links or attachments. Avoid clicking on links in unknown emails or text messages. Verify the source before downloading files.
- Using strong passwords and enabling multi-factor authentication: Robust passwords and multi-factor authentication add an extra layer of security. Strong passwords are longer and more complex, using a combination of uppercase and lowercase letters, numbers, and symbols. Multi-factor authentication requires additional verification steps beyond a password, such as a code sent to a mobile phone.
Developer Preventative Measures
Software developers can proactively mitigate the risk of such vulnerabilities by adhering to stringent security practices throughout the development lifecycle.
- Employing secure coding practices: Incorporating secure coding practices from the initial design phase helps minimize vulnerabilities. This includes validating user inputs, sanitizing data, and implementing secure algorithms. Thorough code reviews can help identify potential security flaws.
- Conducting regular security assessments: Performing regular security assessments, including penetration testing, can identify potential weaknesses in the system architecture and code. This proactive approach can uncover vulnerabilities before they are exploited.
- Implementing robust input validation: Thorough validation of user inputs prevents malicious code injection. This is a critical step in preventing exploitation. Always validate the data coming from external sources, and limit the access that external data has to internal resources.
- Staying updated on security best practices: Staying informed about the latest security vulnerabilities and best practices is essential. This knowledge allows developers to proactively incorporate defenses into their applications and systems.
Security Best Practices
Adhering to security best practices helps to protect against various cyber threats, including Trojan horses.
- Maintaining a strong firewall: A robust firewall acts as a barrier, controlling network traffic and preventing unauthorized access. This is a crucial component of a layered security approach.
- Utilizing intrusion detection and prevention systems: These systems can detect malicious activity and block intrusions in real time. These systems are particularly helpful for detecting anomalous network traffic.
- Implementing regular security awareness training for employees: Education is crucial. Regular training can help employees recognize and avoid phishing attempts, social engineering tactics, and other security threats. Training on recognizing suspicious emails and links is particularly important.
Comparison of Security Measures
| Security Measure | Effectiveness | Limitations |
|---|---|---|
| Firewalls | Effective at blocking unauthorized network access. | Cannot prevent attacks that bypass the firewall, such as social engineering. |
| Antivirus Software | Useful for detecting and removing known malware. | May not detect zero-day exploits or new malware variants. |
| Patching | Addresses known vulnerabilities. | Requires timely updates and user cooperation to be effective. |
Comparison with Other Threats: Trojan Horse Is Newest Windows Vulnerability
This new Trojan horse vulnerability, while novel in its specific implementation, shares similarities and differences with other established threats targeting Windows systems. Understanding these parallels allows for more effective defense strategies and highlights the ongoing evolution of malicious software techniques. A comprehensive comparison illuminates the critical factors driving the success of this particular attack vector and the importance of adapting security measures to evolving threats.
Similarities and Differences in Attack Vectors
This new Trojan horse, like many others, leverages social engineering and exploits known vulnerabilities in Windows systems. The core similarity lies in the deceptive nature of the attack, tricking users into executing malicious code. However, the specific attack vector, the method used to deliver the payload, can vary greatly. Some threats rely on phishing emails, others exploit vulnerabilities in web browsers or applications.
The latest Trojan horse vulnerability affecting Windows systems is definitely a cause for concern. While companies like Sony Ericsson are proactively updating their smartphone software, like in their recent update sony ericsson updates smartphone , it highlights the ongoing need for vigilance in protecting against these kinds of attacks. This means that staying updated on security patches for Windows is crucial to prevent falling victim to these threats.
This new Trojan horse, for instance, may leverage a seemingly legitimate software update or download to gain initial access. The key difference lies in the sophistication of the attack vector, its ability to evade existing security measures, and the specific vulnerabilities targeted.
Factors Influencing Success Rate
Several factors influence the success rate of this Trojan horse. These include the prevalence of the targeted vulnerabilities, the sophistication of the malware, the effectiveness of social engineering tactics, and the user’s level of security awareness. Exploiting widely used and frequently updated software is crucial for attackers, as this maximizes the potential victim pool. A sophisticated malware implementation can bypass traditional security measures, making detection challenging.
A persuasive social engineering campaign can easily deceive users into clicking on malicious links or downloading infected files. Conversely, a high level of user awareness and robust security practices can significantly reduce the success rate of such attacks. Ultimately, a multi-layered approach to security, combining technical measures with user education, is essential for mitigating the risk.
The latest Windows vulnerability, a sneaky Trojan horse, is causing a stir. Switching to digital SLR photography can be daunting, but the Nikon D40, for example, like the Nikon D40 eases transition to the digital SLR world , made it much easier. This new threat is definitely something to watch out for, though.
Evolution of Trojan Horse Techniques
Trojan horse techniques have evolved significantly over time. Initially, Trojans relied on simple, easily detectable methods to gain access to systems. However, modern Trojans often employ sophisticated evasion techniques to bypass traditional security measures. This evolution includes obfuscation techniques, polymorphic code, and the use of advanced encryption methods to obscure the malicious nature of the code. The sophistication of these techniques is continuously increasing, demanding a corresponding advancement in security measures.
This arms race necessitates a dynamic approach to threat detection and response.
Comparison Table
| Threat Type | Attack Vector | Target | Defense Strategies |
|---|---|---|---|
| Traditional Trojan Horse | Malicious email attachments, infected downloads | Operating system, applications | Antivirus software, email filtering, user awareness training |
| Advanced Persistent Threat (APT) Trojan | Compromised legitimate software updates, sophisticated phishing campaigns | Critical infrastructure, financial institutions | Intrusion detection systems, network monitoring, threat intelligence sharing |
| This New Trojan Horse | Exploiting newly discovered vulnerability in a widely used Windows component; disguised as a legitimate software update | Vulnerable Windows systems | Patching vulnerabilities, robust endpoint security, advanced threat detection, enhanced user awareness |
Technical Details and Analysis
The newly discovered Trojan horse vulnerability exploits a previously undocumented weakness in the Windows kernel, specifically targeting the file system handling routines. This allows malicious actors to gain unauthorized access and control over affected systems. Understanding the technical intricacies of this vulnerability is crucial for effective mitigation and future prevention. This analysis delves into the exploitation process, code execution mechanisms, potential root causes, and provides a detailed breakdown of the involved code snippets.This vulnerability leverages a sophisticated technique to bypass security measures and ultimately achieve remote code execution.
The attack vector is subtle, relying on seemingly benign file operations, which makes detection and prevention challenging. The vulnerability is critical, given its potential impact on a broad range of Windows systems.
Code Execution Mechanisms
The Trojan horse exploits a buffer overflow vulnerability in a specific kernel function responsible for handling file path parsing. This function is crucial for the proper operation of the Windows file system, allowing the loading and execution of arbitrary files. The exploit meticulously crafts malicious input data that triggers the overflow, leading to the execution of attacker-controlled code. This controlled code is loaded into the system’s memory space, allowing for complete control of the affected system.
Potential Root Causes
The vulnerability originates from a lack of proper input validation in the kernel’s file path parsing routine. Insufficient bounds checking in the code allows attackers to provide input data that exceeds the allocated buffer size. This leads to the overflow condition, which can be exploited to inject malicious code. Furthermore, the use of a deprecated API, not updated with modern security considerations, might have contributed to the vulnerability.
Exploitation Process
The exploitation process begins with the attacker creating a specially crafted file. This file contains malicious code designed to exploit the buffer overflow vulnerability. The attacker then attempts to open or interact with this file, triggering the overflow condition. This leads to the execution of the attacker’s code within the kernel’s memory space. The attacker’s code then establishes persistence and potentially further malicious activity.
Code Snippets and Impact
| Code Snippet | Purpose | Potential Impact |
|---|---|---|
strcpy(buffer, malicious_input); |
Attempts to copy malicious input into a fixed-size buffer. | Leads to buffer overflow if the input exceeds the buffer size. |
system("cmd /c attacker_command"); |
Executes attacker’s command string. | Allows the attacker to execute arbitrary commands on the system. |
write_file("persistence_file", payload); |
Writes malicious payload to a file. | Creates persistence for the attacker, allowing them to re-execute the payload later. |
(kernel function) vulnerable_function(malicious_input); |
The vulnerable kernel function that is the core of the attack. | The exploit takes advantage of a flaw in this function. |
The table above illustrates the key code snippets used in the attack and their corresponding roles. Understanding these snippets is crucial for analyzing the vulnerability and implementing mitigation strategies.
Real-World Scenarios and Case Studies
Real-world examples of Trojan horse attacks are crucial for understanding the methods employed, the impact they have, and the strategies used for mitigation. Analyzing past incidents allows for proactive measures to be taken to protect against similar future threats. Studying the aftermath and recovery processes in these cases provides valuable lessons for improving incident response and minimizing damage.
Illustrative Examples of Trojan Horse Attacks
Past and present examples demonstrate the pervasive nature of Trojan horse attacks. The sophistication and variety of attack vectors, combined with the evolving landscape of Windows vulnerabilities, highlight the importance of constant vigilance and robust security practices. These attacks have demonstrated that no system, regardless of its sophistication, is entirely immune to this type of threat.
Case Studies of Attacks Targeting Specific Windows Versions
Numerous attacks have targeted specific Windows versions, leveraging vulnerabilities in operating systems or applications. These attacks exploit weaknesses in the system’s architecture or software components. The success of these attacks often depends on the attacker’s ability to identify and exploit these vulnerabilities. By analyzing these vulnerabilities, security professionals can develop more effective defensive strategies and enhance overall security posture.
Attack Methods and Techniques
Understanding the methods used in these attacks provides valuable insights into the tactics and procedures of attackers. Attackers frequently use social engineering techniques to gain initial access, often disguised as legitimate programs or updates. This manipulation of users into compromising their systems is a common factor in many successful Trojan horse attacks. Moreover, attackers often leverage malicious code hidden within seemingly harmless files or programs.
Aftermath and Recovery Processes
The aftermath of a Trojan horse attack can be devastating, encompassing significant financial losses, reputational damage, and legal ramifications. The recovery process involves identifying the affected systems, containing the spread of the malware, and restoring data. The complexity of the recovery process depends heavily on the scope of the attack and the resources available to the affected party.
Table of Real-World Attacks, Impact, and Responses
| Attack Name | Impact (Estimated) | Response from Affected Parties |
|---|---|---|
| WannaCry ransomware (2017) | Millions of dollars in damages globally, widespread disruption of services. | Patch deployment and emergency response measures were implemented, but not all systems were protected. Increased focus on patching and security awareness training followed. |
| NotPetya (2017) | Estimated billions in damages, disrupting global supply chains and manufacturing. | Affected parties had to contend with significant data loss and recovery challenges. Focus on robust backup and disaster recovery plans emerged as a crucial component of security strategies. |
| Emotet (ongoing) | Ongoing financial losses and disruption of services due to its use in various cyberattacks. | Continued efforts to identify and disrupt the Emotet network are ongoing. International cooperation and collaborative efforts among security organizations are crucial. |
Closing Summary
In conclusion, the new Trojan horse vulnerability poses a significant risk to Windows users. Understanding its technical aspects, the potential impact, and the mitigation strategies is crucial for protecting systems. We’ve explored the historical context, analyzed the attack methods, and examined the potential damage. By implementing the preventative measures Artikeld, users and developers can better safeguard their systems against this evolving threat.
This vulnerability serves as a stark reminder of the ever-present need for vigilance and proactive security measures in the digital realm.