Amazon Simple Email Service Increasingly Abused in Sophisticated Phishing Campaigns, Evading Traditional Security Measures

The Amazon Simple Email Service (SES), a robust cloud-based email sending platform, is experiencing a significant surge in malicious exploitation by threat actors, who are leveraging its inherent legitimacy to dispatch highly convincing phishing emails. These sophisticated attacks are adept at bypassing conventional security filters and rendering reputation-based blocking mechanisms largely ineffective, posing a substantial and growing threat to individuals and organizations worldwide.
This escalating abuse of a trusted cloud resource has been brought to light by cybersecurity researchers, with Kaspersky noting a marked "uptick in phishing attacks leveraging Amazon SES" to deliver malicious links. While Amazon SES has been previously implicated in similar nefarious activities—such as the incident involving a stolen Kaspersky SES token used in Office 365 phishing campaigns—the current spike is believed to be primarily driven by the widespread exposure of AWS Identity and Access Management (IAM) access keys across various public repositories and assets.
Understanding Amazon SES and Its Appeal to Threat Actors
Amazon SES is a core component of Amazon Web Services (AWS), designed to allow developers and businesses to send emails programmatically. It offers a highly scalable, reliable, and cost-effective solution for sending transactional emails, marketing communications, and other types of messages. Its infrastructure is built for high deliverability, ensuring that legitimate emails reach their intended recipients without being flagged as spam. This reliability is precisely what makes it an attractive target for cybercriminals.
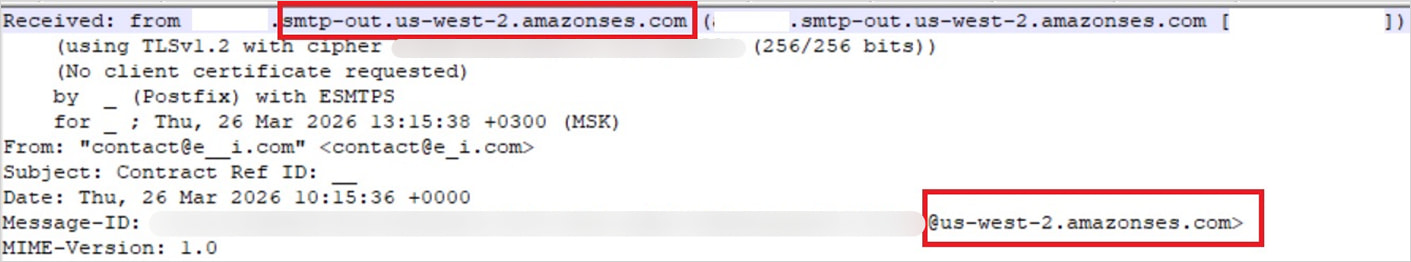
When threat actors gain unauthorized access to valid AWS SES credentials, they effectively inherit the reputation and trusted infrastructure of AWS. This allows their phishing emails to pass critical authentication checks, including Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC) protocols. These protocols are fundamental to verifying the legitimacy of an email’s sender and are a primary line of defense against email spoofing. By originating from SES, the malicious emails appear to be genuinely sent from a legitimate, trusted service, thereby circumventing these vital security layers.
The Root Cause: Proliferation of Exposed AWS Credentials

Kaspersky researchers pinpoint the increasing exposure of AWS credentials as the main driver behind this surge in SES abuse. These sensitive access keys are inadvertently leaked in a variety of public locations, including GitHub repositories, .ENV configuration files, Docker images, unsecured backups, and publicly accessible Amazon S3 buckets. The sheer volume of public code and data repositories makes the task of discovering these exposed secrets feasible for automated tools.
AWS IAM provides granular control over who can access AWS resources and under what conditions. IAM access keys consist of an access key ID and a secret access key, which function much like a username and password for programmatic access to AWS services. When these keys are exposed, attackers can use them to impersonate the legitimate owner and access the associated AWS services, including SES, depending on the permissions granted to the compromised key. The problem of credential leakage is not new, but its scale continues to grow with the proliferation of cloud development and DevOps practices, where misconfigurations or oversights can lead to severe security vulnerabilities. Industry reports frequently highlight that thousands of sensitive credentials, including API keys and cloud access tokens, are inadvertently pushed to public code repositories annually.
Automated Reconnaissance and Exploitation Workflow
The process by which threat actors exploit these exposed credentials is highly automated and efficient. Bots, often built leveraging open-source utilities like TruffleHog—a tool originally designed to scan for leaked secrets in code—are deployed to continuously monitor public assets for AWS access keys.
Once a key is discovered, the attackers do not immediately launch their campaigns. Instead, they follow a systematic workflow:
- Secret Scanning: Automated bots tirelessly scour vast datasets, including GitHub, for strings resembling AWS access keys.
- Permission Validation: Upon discovery, the attackers validate the key’s permissions. This involves testing what AWS services the key can access and what actions it can perform. For SES abuse, they specifically look for keys with
ses:SendEmailorses:SendRawEmailpermissions. - Email Sending Limit Verification: Attackers also determine the email sending limits associated with the compromised SES account. This allows them to gauge the potential scale of their phishing operation.
- Mass Distribution: After verifying permissions and limits, attackers are equipped to orchestrate the distribution of a massive volume of phishing messages. This streamlined process, from discovery to deployment, enables unprecedented levels of abuse, allowing threat actors to launch widespread campaigns rapidly and effectively.
Anatomy of a Sophisticated Phishing Attack
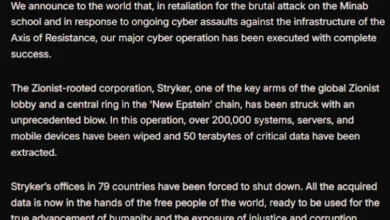
The quality and sophistication of the phishing campaigns leveraging Amazon SES are remarkably high, as observed by Kaspersky. Attackers are employing custom HTML templates that meticulously mimic legitimate services, coupled with realistic login flows designed to deceive even vigilant users.
One prominent example includes fake document-signing notifications that imitate services like DocuSign. These emails lead unsuspecting victims to AWS-hosted phishing pages, which are meticulously crafted to harvest credentials or deploy malware. The use of AWS infrastructure for hosting these malicious pages further enhances their legitimacy in the eyes of automated scanners and users alike, as the URLs often appear to belong to a trusted cloud provider.
Beyond simple credential harvesting, threat actors are also engaging in more advanced Business Email Compromise (BEC) attacks. BEC, a form of cybercrime involving social engineering to defraud organizations, is particularly potent when delivered via SES. Attackers fabricate entire email threads, often impersonating senior executives or trusted business partners, to create a compelling narrative. These fabricated exchanges can include fake invoices, payment requests, or urgent financial transactions, all designed to trick finance departments into making unauthorized payments. The seamless delivery of these highly personalized and contextually relevant emails, devoid of typical spam indicators, significantly increases their success rate and the potential financial damage to businesses. The FBI’s Internet Crime Complaint Center (IC3) reported that BEC schemes accounted for over $2.7 billion in losses in 2022, underscoring the devastating impact of such attacks.
The Ineffectiveness of Traditional Defenses
The exploitation of Amazon SES presents a unique challenge for cybersecurity professionals because traditional email security measures are largely rendered ineffective.
- Email Authentication Protocols (SPF, DKIM, DMARC): As previously mentioned, emails sent through a compromised SES account will inherently pass these authentication checks. SPF records verify the sender’s IP address, DKIM adds a digital signature to emails, and DMARC builds upon these to provide policy enforcement. Since the emails are originating from AWS’s legitimate mail servers, correctly configured for SES, these protocols validate the emails as authentic, despite their malicious content.
- Reputation-Based Blocking: Email security gateways and spam filters often rely on the sender’s IP address and domain reputation to identify and block malicious emails. However, blocking the IP addresses associated with Amazon SES is not a viable solution. AWS operates vast ranges of IP addresses, and blocking them would inevitably prevent all legitimate emails sent through SES from reaching their recipients, crippling countless businesses that rely on the service for their critical communications. This presents a critical dilemma for defenders, as the very infrastructure designed for trust and reliability is being weaponized.
- Content-Based Analysis: While advanced content analysis can detect some phishing attempts, the high quality of the custom HTML templates and realistic login flows used by attackers makes it increasingly difficult for automated systems to differentiate between legitimate and malicious content, especially when the emails are contextually relevant (as in BEC attacks).
This scenario underscores the inherent complexities of the "shared responsibility model" in cloud security, where AWS is responsible for the security of the cloud, and the customer is responsible for security in the cloud. In this case, the customer’s responsibility to secure their IAM credentials directly impacts the security of email recipients globally.
Expert Recommendations and the Path Forward
In light of these findings, Kaspersky has issued a series of critical recommendations for organizations to mitigate the risk of Amazon SES abuse and enhance their overall cloud security posture:
- Restrict IAM Permissions based on the Principle of Least Privilege: This fundamental security principle dictates that users and services should only be granted the minimum permissions necessary to perform their intended functions. For SES, this means ensuring that IAM users or roles only have
ses:SendEmailorses:SendRawEmailpermissions if absolutely required, and these should be as narrowly scoped as possible (e.g., restricted to specific sender identities or IP ranges). Over-privileged credentials significantly amplify the impact of a compromise. - Enable Multi-Factor Authentication (MFA): MFA adds an essential layer of security by requiring users to provide two or more verification factors to gain access. Even if an attacker obtains an access key, MFA would prevent them from using it without the second factor (e.g., a code from a mobile app or a hardware token). This should be mandated for all AWS accounts and IAM users.
- Regularly Rotate Keys: Access keys should be rotated periodically, typically every 90 days. This practice minimizes the window of opportunity for attackers to exploit compromised keys. If a key is leaked, its utility to an attacker is limited by its lifespan. Automated key rotation mechanisms can help enforce this policy.
- Apply IP-Based Access Restrictions: For IAM users accessing AWS management console or API, implementing IP-based access restrictions ensures that credentials can only be used from trusted networks or specific IP addresses. While this doesn’t directly prevent SES emails from being sent if a key is compromised, it significantly limits an attacker’s ability to use the compromised key from an unauthorized location.
- Implement Encryption Controls: While not directly related to preventing email sending, strong encryption for data at rest and in transit (where applicable) is a critical component of overall cloud security, protecting sensitive data that might be associated with IAM credentials or other AWS resources.
Beyond these specific recommendations, broader industry best practices for cloud security are paramount. This includes continuous monitoring for exposed credentials, regular security audits of AWS configurations, developer education on secure coding practices and credential management, and implementing robust security information and event management (SIEM) systems to detect anomalous activity within AWS environments. Cloud security posture management (CSPM) tools can also play a vital role in identifying misconfigurations and potential vulnerabilities proactively.
Broader Implications for Cloud Security and Trust
The increasing abuse of Amazon SES for phishing campaigns highlights a critical evolution in the threat landscape. It underscores the challenges posed by the sophistication of modern cybercriminals who continually adapt their tactics to exploit legitimate infrastructure. The reliance on trusted cloud services like AWS, while offering immense benefits in terms of scalability and reliability, also presents a double-edged sword when these services are weaponized.
This trend has significant implications for enterprise security posture, necessitating a shift from perimeter-focused defenses to a more identity-centric and layered security approach. Organizations must assume that credentials will be compromised and build their defenses accordingly, focusing on detection, response, and containment. For cybersecurity vendors, this presents an ongoing challenge to develop more intelligent and adaptive solutions that can detect subtle anomalies in email traffic and content, even when originating from highly reputable sources.
Ultimately, the erosion of trust in email as a communication channel is a worrying consequence. As phishing attacks become more sophisticated and harder to detect, users may become more skeptical of all digital communications, impacting legitimate business processes and user experience. The ongoing cat-and-mouse game between attackers and defenders in the cloud era continues, demanding constant vigilance, adaptation, and a proactive commitment to robust security practices across the entire digital ecosystem.