Day 60: Decoupling State and CloudWatch FinOps
This report details critical operational improvements made to a Serverless AI Financial Agent on Day 60 of its development cycle, focusing on rectifying technical debt related to application state management and cloud cost optimization. The interventions addressed two primary areas: the decoupling of user identity from hardcoded values within AWS Lambda functions and the strategic adjustment of Amazon CloudWatch log retention policies to mitigate escalating storage costs. These enhancements are crucial for preparing the application for scalability and robust handling of a production user base.
Addressing Application State and Identity Collisions
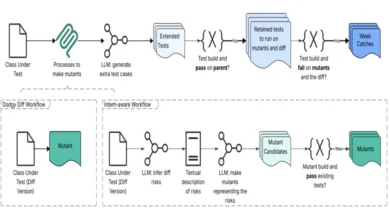
A significant operational challenge identified was the duplication of user reports, leading to the erroneous dispatch of identical email notifications. Initial investigations into the Amazon DynamoDB database confirmed its integrity, revealing that the root cause of the duplicate processing lay within the AWS Lambda execution environment. Specifically, a hardcoded USER_ID variable, implemented as a fallback mechanism during the initial sandbox development phase, was identified as the culprit.
This hardcoded identifier, which did not align with actual Amazon Cognito UUIDs stored in the database, was causing the Lambda function to generate a temporary, in-memory profile. This fabricated profile was then being merged with legitimate user records just prior to processing messages from the Simple Queue Service (SQS) queue. The consequence was a de facto bifurcation of user data processing, resulting in duplicate actions.
The Solution: Embracing Environment Variables for Dynamic Configuration
The resolution involved a fundamental principle of robust application design: decoupling configuration from code. The hardcoded USER_ID was systematically removed from the Python script. In its place, the necessary user identifier is now securely injected into the Lambda execution environment through AWS Lambda Environment Variables.

This architectural shift transforms the application’s behavior. By externalizing the USER_ID, the Lambda function operates in a stateless manner, becoming inherently dynamic. This dynamic configuration is essential for multi-tenancy architectures, preventing identity collisions and ensuring that each user’s data is processed independently and accurately. The principle underscores the critical importance of ensuring that all configuration parameters, especially sensitive or dynamic ones like user identifiers, reside outside the application’s codebase. This practice not only enhances security but also facilitates easier updates and management without requiring code redeployments.
Supporting Data:
- AWS Lambda: A serverless compute service that lets you run code without provisioning or managing servers. Lambda functions are event-driven and can be triggered by a variety of AWS services.
- Amazon DynamoDB: A fully managed NoSQL database service that provides fast and predictable performance with seamless scalability.
- Amazon Cognito: A service that provides user identity and access management for your web and mobile applications.
- Amazon SQS: A fully managed message queuing service that enables you to decouple and scale microservices, distributed systems, and serverless applications.
- Environment Variables: Key-value pairs that can be used to configure Lambda functions. They are accessible within the function code and provide a secure and flexible way to manage configuration settings.
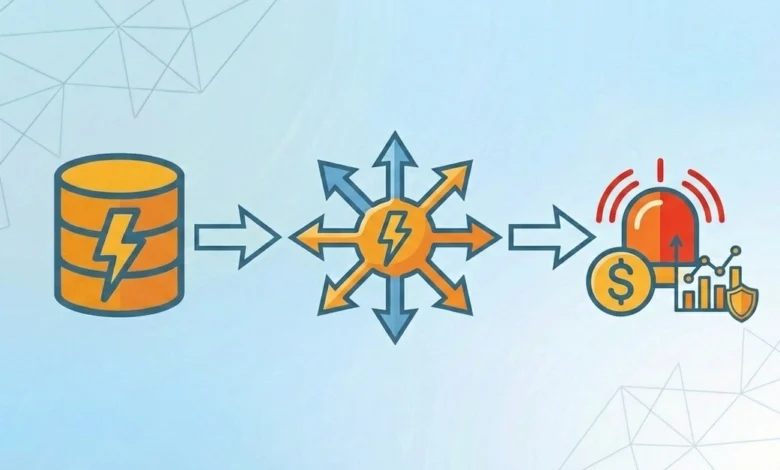
Mitigating Cloud Costs with CloudWatch Log Retention Policies
The second significant operational issue addressed was a silent, yet potent, threat to cloud expenditure, commonly referred to as "FinOps" (Financial Operations). AWS Lambda, by default, automatically streams all execution output, including debug logs, to Amazon CloudWatch Log Groups. A critical oversight in the default configuration is the log retention policy, which is typically set to "Never Expire."
For applications experiencing high traffic volumes, retaining an indefinite history of debug logs can lead to substantial and avoidable storage costs. Over time, the accumulation of these logs can inflate cloud bills significantly without providing commensurate operational value, especially beyond a defined troubleshooting window.
The Intervention: Implementing a Strategic Log Retention Policy
To counter this escalating cost, the development team navigated to the Amazon CloudWatch console. The retention policy for the relevant Lambda functions’ Log Groups was strategically adjusted to a 14-day window.

This seemingly minor adjustment, reportedly taking approximately 30 seconds to implement, acts as an automated log management system. It provides a sufficient period – a two-week sliding window – for developers and operations teams to investigate and resolve any emergent bugs or anomalies. Post this period, AWS automatically purges the historical log data, thereby eliminating unnecessary storage charges. This proactive measure aligns with best practices in cloud cost management, ensuring that resources are utilized efficiently and expenditures are directly correlated with active operational needs.
Supporting Data:
- Amazon CloudWatch: A monitoring and observability service built for DevOps engineers, developers, site reliability engineers (SREs), and IT managers.
- Log Groups: Collections of log streams that share the same retention, monitoring, and access control settings.
- Log Retention Policy: A setting within CloudWatch that determines how long log data is stored. Options typically include:
- Never Expire (default)
- 1 day, 3 days, 5 days, 7 days, 14 days, 30 days, 60 days, 90 days, 120 days, 150 days, 365 days, 1095 days, 730 days, 2557 days, 3650 days.
- FinOps: A cultural practice that brings financial accountability to the variable spend model of cloud, enabling organizations to make business trade-offs by bringing together teams—finance, technology, and business—to manage cloud costs.
Broader Implications and Best Practices
The recent interventions highlight a critical duality in cloud architecture: it is not solely about the components that are actively built and deployed, but also about the deliberate decisions made regarding resource management and data lifecycle. The principle of "least persistence" should be a guiding factor, where data and logs are retained only for as long as they serve a clear and active purpose.
Key Takeaways for Scalable Cloud Architectures:
-
Never Hardcode State: Application state, particularly dynamic identifiers and configuration parameters, should always be externalized. Utilizing services like AWS Lambda Environment Variables, AWS Systems Manager Parameter Store, or AWS Secrets Manager ensures that applications are flexible, secure, and capable of handling diverse operational scenarios without code modification. This principle is fundamental for building applications that can scale horizontally and support multiple tenants or users seamlessly.
-
Implement Proactive Log Management: The default "Never Expire" setting for CloudWatch Log Groups is a common oversight that can lead to significant, unintended cloud costs. Establishing a well-defined log retention policy, aligned with the organization’s incident response and debugging needs, is a crucial FinOps practice. A balanced approach allows for effective troubleshooting while preventing unnecessary expenditure on historical data that has diminishing value.

-
Prioritize Technical Debt Remediation: The developer’s decision to pause feature development to address these operational issues underscores the importance of prioritizing technical debt. Ignoring such issues, especially in the early stages of an application’s lifecycle, can lead to compounding problems, increased costs, and hindered scalability as the application matures and scales. Proactive refactoring and optimization are essential for long-term success in cloud environments.
The Serverless AI Financial Agent’s development journey on Day 60 serves as a practical case study in the ongoing effort to build resilient, cost-effective, and scalable cloud-native applications. By diligently addressing issues of state management and log retention, the project is better positioned to handle increased user loads and evolving business requirements.