Kyrgyzstan’s Grinex Cryptocurrency Exchange Halts Operations Following $13.7 Million Hack, Blaming "Western Intelligence Agencies"

Grinex, a cryptocurrency exchange operating out of Kyrgyzstan, has announced the suspension of its services following a sophisticated cyberattack that resulted in the theft of approximately $13.7 million. The platform has controversially attributed the breach to "Western intelligence agencies," asserting that the attack was designed to undermine Russia’s financial autonomy. The stolen funds were reportedly siphoned from cryptocurrency wallets primarily belonging to Russian users, impacting a service that facilitated crucial crypto-ruble exchange operations for Russian businesses and individuals.
Background and Context: The Shadow of Sanctions and Illicit Finance
The incident casts a long shadow over the already complex landscape of cryptocurrency exchanges operating in regions subject to international sanctions. Grinex, which commenced operations in early 2025, has long been suspected of being a rebranded iteration of Garantex, a Russian crypto exchange with a history steeped in controversy. Garantex gained notoriety for its alleged involvement in processing over $100 million in illicit transactions and facilitating extensive money laundering schemes. Its administrative personnel faced arrests, and its associated domains were seized by authorities, highlighting the severe regulatory scrutiny it attracted.
The suspicions surrounding Grinex’s true identity were not merely speculative. In August 2025, the U.S. Department of the Treasury officially imposed sanctions against Grinex, citing compelling evidence that the exchange was a direct continuation of Garantex’s activities. The Treasury Department’s assessment concluded that Grinex accepted the same clientele, handled their funds, and performed an identical role as a facilitator of illegal financial operations. This designation underscored the international community’s concerns about the platform’s role in the global financial system, particularly its potential to circumvent established financial regulations and sanctions.
Despite these significant sanctions, Grinex continued to function, positioning itself as a vital conduit for Russia to maintain a degree of financial sovereignty and bypass the array of international sanctions that have heavily impacted its traditional banking and transaction systems. A key mechanism for this was the platform’s adoption of A7A5, a Russian ruble-backed stablecoin directly inherited from Garantex. This stablecoin enabled seamless crypto-ruble exchanges, offering an alternative financial channel for individuals and businesses grappling with the restrictions imposed by global sanctions. The very existence and operational model of Grinex, therefore, represented a direct challenge to the international efforts to isolate Russia financially.
The Attack Details: A Chronology of the Theft

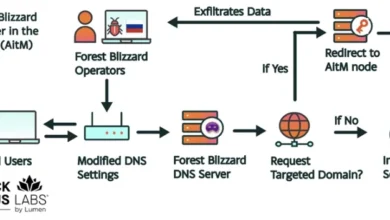
The cyberattack, as reported by blockchain analysis firm Elliptic, occurred on a Wednesday at precisely 12:00 UTC. The perpetrators executed a swift and coordinated theft, moving the pilfered funds to various TRON and Ethereum addresses. Following the initial transfer, the stolen assets were quickly converted into TRX (TRON’s native cryptocurrency) and ETH (Ethereum’s native cryptocurrency) through the SunSwap decentralized trading protocol. This rapid conversion and dispersion across different blockchain networks are common tactics employed by attackers to obscure the trail of stolen funds and complicate recovery efforts.
Further investigations by TRM Labs, another prominent blockchain analysis firm, revealed additional layers to the sophisticated operation. TRM Labs identified a total of 70 distinct attacker addresses involved in the Grinex breach. Moreover, their analysis uncovered a parallel cyberattack targeting TokenSpot, another cryptocurrency exchange also based in Kyrgyzstan and reportedly possessing direct ties to Grinex. The proximity of these two attacks, both geographically and operationally, suggests a potentially interconnected network of illicit financial activities.
Grinex’s Allegations and Lack of External Validation
In the aftermath of the hack, Grinex issued a strongly worded statement, directly accusing "foreign intelligence agencies" of orchestrating the attack. The exchange asserted that the nature of the attack, coupled with the digital footprint left behind, pointed to a threat actor possessing "an unprecedented level of resources and technology, accessible only to entities of hostile states." Grinex further claimed that, according to preliminary data, the attack was "coordinated with the aim of directly harming Russia’s financial sovereignty."
However, these grave accusations have yet to be substantiated by independent third-party analysis. Neither Grinex’s official announcement nor the subsequent reports from reputable blockchain intelligence firms like Elliptic and TRM Labs have provided any concrete technical evidence or indicators to support the exchange’s specific attribution to "Western intelligence services." Elliptic’s report, while detailing the movement and conversion of the stolen funds, refrained from speculating on the perpetrator’s identity. Similarly, TRM Labs’ findings focused on identifying attacker addresses and the link to the TokenSpot hack, without endorsing or refuting Grinex’s politically charged claims. The absence of verifiable proof leaves Grinex’s attribution highly contentious and open to skepticism within the cybersecurity and geopolitical communities. BleepingComputer’s attempts to solicit a response from Grinex regarding the attribution prior to publication did not yield any immediate answers.
The Broader Network: TokenSpot and Links to Illicit Activities
The discovery of a concurrent hack at TokenSpot, and its alleged connections to Grinex, adds another layer of complexity and concern to the situation. TRM Labs’ investigation into TokenSpot revealed alarming ties to a spectrum of illicit financial activities. These include laundering operations linked to Houthi groups, involvement in weapons procurement networks, and a connection to the "InfoLider" influence operation in Moldova. Significantly, TRM Labs noted that these activities collectively align with broader Russian strategic goals, suggesting a deeper, more intertwined web of financial malfeasance and geopolitical objectives.

The implication here is profound: if Grinex and TokenSpot are indeed linked, and both are embroiled in activities that facilitate sanction evasion and support destabilizing influence operations, then the entire ecosystem becomes a focal point for national security concerns. The alleged connections to Houthi financing, for instance, would place these exchanges squarely in the crosshairs of counter-terrorism financing efforts, amplifying the severity of their operations far beyond simple sanction circumvention.
Implications and Future Outlook
The Grinex hack, regardless of the veracity of its attribution claims, carries significant implications for various stakeholders. For Russian users, it represents a direct financial loss and a blow to the perceived reliability of alternative financial channels. The incident highlights the inherent risks associated with using platforms that operate in defiance of international sanctions, often outside the purview of traditional regulatory safeguards. The collapse or prolonged suspension of Grinex could severely impact the ability of Russian entities to conduct crypto-ruble transactions, further constricting their access to global finance.
From a broader perspective, the incident underscores the ongoing challenge of enforcing financial sanctions in the age of decentralized finance. Cryptocurrency exchanges, especially those operating in less regulated jurisdictions, can become critical nodes for bypassing traditional financial controls. The Grinex case exemplifies the "cat-and-mouse" game between sanction enforcers and those seeking to exploit the pseudonymous and borderless nature of cryptocurrencies.
The lack of concrete evidence for Grinex’s "Western intelligence" attribution also poses a challenge to objective reporting and analysis. Such claims, when unverified, can be used to deflect blame, generate political narratives, or obscure the true nature of an attack, potentially hindering effective incident response and accountability. It also raises questions about the internal security postures of such exchanges, particularly given their history of alleged illicit activities.
The involvement of platforms like TokenSpot in a wider network of illicit finance, including Houthi-linked laundering and influence operations, signals an escalating concern for global security agencies. This incident will likely intensify scrutiny on all "shadow" crypto platforms and their operators, prompting further investigations and potentially leading to more aggressive enforcement actions. As the digital economy evolves, the line between legitimate financial innovation and tools for illicit activity continues to blur, making the role of blockchain analysis firms and international regulatory bodies more critical than ever in uncovering and dismantling these complex networks. The Grinex hack serves as a stark reminder of the volatile intersection of cybersecurity, geopolitics, and the evolving world of digital assets.