Russia Hacked Routers to Steal Microsoft Office Tokens
Hackers linked to Russia’s military intelligence units, operating under the designation "Forest Blizzard," have been observed leveraging known vulnerabilities in outdated Internet routers to conduct a sophisticated, large-scale campaign aimed at harvesting authentication tokens from Microsoft Office users. This revelation, brought to light by security experts at Microsoft, Lumen’s Black Lotus Labs, and the U.K.’s National Cyber Security Centre (NCSC) in a flurry of advisories, underscores a concerning evolution in state-sponsored cyber espionage tactics. The spying operation enabled state-backed Russian hackers to silently siphon authentication tokens from users across more than 18,000 networks, achieving their objective without deploying traditional malicious software or code on victim endpoints.
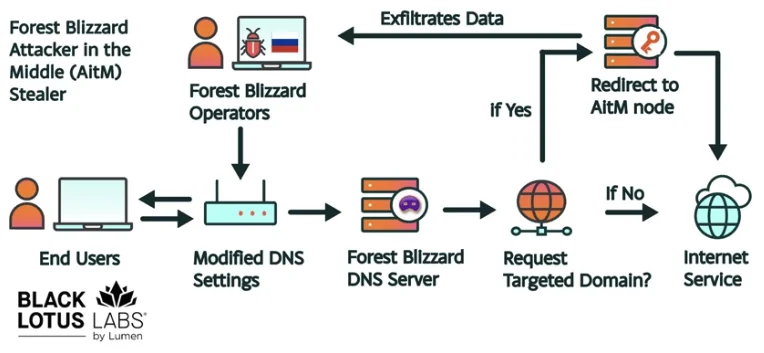
The campaign represents a strategic shift by the threat actor, also known as APT28 or Fancy Bear, towards "old-school" yet highly effective methods that bypass many modern endpoint detection and response systems. By exploiting unpatched or end-of-life Small Office/Home Office (SOHO) routers, Forest Blizzard managed to hijack Domain Name System (DNS) settings, rerouting traffic through attacker-controlled servers to facilitate Adversary-in-the-Middle (AiTM) attacks against Transport Layer Security (TLS) connections. This allowed them to intercept sensitive OAuth authentication tokens, granting direct access to victim accounts without needing to overcome multi-factor authentication (MFA) prompts.
Understanding the Threat: Forest Blizzard and Its Modus Operandi
Forest Blizzard, consistently attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU), has a notorious history of engaging in disruptive and espionage-focused cyber operations. The group gained international infamy for its interference in the 2016 U.S. presidential election, famously compromising the Democratic National Committee (DNC), the Democratic Congressional Campaign Committee (DCCC), and the Hillary Clinton campaign. Their operational sophistication and willingness to adapt to defensive measures make them one of the most persistent and dangerous state-sponsored threat actors.
In this latest campaign, Forest Blizzard demonstrated a remarkable pivot in tactics. Researchers at Black Lotus Labs, the security division of Internet backbone provider Lumen, discovered that at its peak in December 2025, the surveillance dragnet encompassed over 18,000 Internet routers. The vast majority of these compromised devices were unsupported, end-of-life models, or severely lagging on critical security updates. Ryan English, a Black Lotus Security Engineer, highlighted the elegance of the attack: "These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done."
The primary targets for this operation were governmental agencies, including ministries of foreign affairs, law enforcement entities, and third-party email providers. This strategic targeting underscores the espionage motivation behind the campaign, aiming to gather intelligence and maintain persistent access to sensitive communications.
The Technical Deep Dive: DNS Hijacking and OAuth Token Theft
The core of Forest Blizzard’s success lies in its exploitation of SOHO routers, predominantly older Mikrotik and TP-Link devices. These devices, often deployed without adequate security oversight in smaller organizations or home offices, present a "soft underbelly" for sophisticated attackers. Instead of deploying complex malware, the GRU hackers capitalized on known vulnerabilities to simply alter the DNS settings of these routers.
DNS, or the Domain Name System, acts as the internet’s phonebook, translating human-readable website addresses (like "microsoft.com") into machine-readable IP addresses. In a DNS hijacking attack, malicious actors interfere with this crucial process. By modifying a router’s DNS configuration, Forest Blizzard redirected legitimate DNS queries to their own controlled servers. The NCSC’s advisory elaborates on this, explaining that such interference covertly sends users to malicious websites or, in this case, allows the interception of network traffic.
Once the DNS settings were altered, all users connected to the compromised local network would inadvertently use the attacker-controlled DNS servers. This critical step enabled the adversary to perform AiTM attacks on TLS connections, particularly those destined for Microsoft Outlook on the web domains. Microsoft’s blog post confirmed this, stating, "While targeting SOHO devices isn’t a new tactic, this is the first time Microsoft has seen Forest Blizzard using DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices."
The significance of this approach lies in the interception of OAuth authentication tokens. OAuth tokens are digital credentials typically issued after a user successfully logs in and often completes multi-factor authentication. By capturing these tokens, the attackers could gain direct, unauthorized access to victim accounts, effectively bypassing the need to phish for credentials or one-time codes. This method is incredibly potent as it circumvents one of the most effective modern security controls—MFA—without requiring any direct interaction from the user or the installation of malicious software on their device. The simplicity and effectiveness of this token-based access highlight a critical vulnerability in how many modern web services manage user sessions.
Chronology of Discovery and Adaptive Tactics

The timeline of Forest Blizzard’s activities reveals a highly adaptive and responsive threat actor. The group’s tactical evolution became particularly evident following an NCSC report in August 2025. Prior to this report, Forest Blizzard had been observed using malware to control a smaller, more targeted group of compromised routers. This approach was effective but limited in scale.
However, according to Danny Adamitis, another engineer at Black Lotus Labs, the day after the NCSC report was released, Forest Blizzard quickly abandoned its malware-centric strategy. Instead, it pivoted to mass-altering DNS settings on thousands of vulnerable routers. Adamitis noted, "Before the last NCSC report came out they used this capability in very limited instances. After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable." This rapid and large-scale adaptation demonstrates the GRU’s capacity to swiftly retool and expand operations in response to public disclosures, turning a limited capability into a widespread espionage tool.
The peak of this widespread DNS hijacking campaign occurred in December 2025, ensnaring more than 18,000 routers. The subsequent public disclosures by Microsoft, Lumen, and the NCSC in April 2026 serve as a coordinated effort to alert the global cybersecurity community and prompt immediate defensive actions. The expectation from experts like Adamitis is that Forest Blizzard will likely respond to this renewed attention by once again evolving its tactics, underscoring the perpetual cat-and-mouse game in the cybersecurity realm.
Official Responses and Broader Implications
The concerted effort by multiple cybersecurity entities to disclose and detail this campaign highlights its severity. Microsoft, a primary target due to its ubiquitous Office suite, issued a detailed blog post outlining the compromise and providing mitigation strategies. Their analysis confirms the novelty of Forest Blizzard’s large-scale DNS hijacking for AiTM attacks against edge devices, marking a significant development in the threat landscape.
Lumen’s Black Lotus Labs provided the granular detail on the scale of the compromise and the types of devices affected, reinforcing the critical need for better SOHO router security. Their findings serve as a stark reminder that even seemingly innocuous network hardware can be weaponized with devastating effect.
The NCSC, as the UK’s authority on cyber security, also published an advisory, contextualizing the threat within the broader landscape of Russian state-sponsored activity and providing actionable advice for individuals and organizations. Their consistent monitoring and reporting on APT28’s activities have been instrumental in tracking the group’s evolving methodologies.
Beyond the immediate technical responses, this incident feeds into a broader global conversation about supply chain security and the vulnerability of consumer-grade networking equipment. The U.S. Federal Communications Commission (FCC) recently took a significant step in this direction. On March 23, the FCC announced a much broader approach to national security, stating it would no longer certify consumer-grade Internet routers produced outside of the United States. This policy, which effectively broadens a previous ban aimed at specific companies like TP-Link, stems from warnings that foreign-made routers pose "a severe cybersecurity risk that could be leveraged to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
While the FCC’s policy isn’t a direct response to this specific Forest Blizzard campaign, it underscores the systemic vulnerabilities exploited by such attacks. Experts have noted the profound implications of this FCC policy, suggesting it could severely limit the availability of new consumer-grade routers, with exceptions potentially requiring "conditional approval" from the Department of War or Department of Homeland Security. This regulatory shift reflects a growing recognition at the highest levels of government that the integrity of basic network infrastructure is a national security imperative. The policy does not retroactively affect previously purchased routers, leaving millions of existing, potentially vulnerable devices in circulation—precisely the kind of devices Forest Blizzard exploited.
Recommendations and Path Forward
The Forest Blizzard campaign serves as a critical wake-up call for individuals, organizations, and governments alike. The simplicity yet effectiveness of the "old-school" DNS hijacking tactic demonstrates that attackers don’t always need zero-day exploits or complex malware to achieve their objectives. Often, basic security hygiene failures are sufficient.
For organizations and individual users, immediate actions are imperative:
- Update Router Firmware: Ensure all SOHO and enterprise-grade routers are running the latest firmware. Many of the exploited vulnerabilities are well-known and patched in newer versions.
- Replace End-of-Life Devices: Routers that are no longer supported by manufacturers will not receive security updates and should be replaced.
- Change Default Credentials: Always change default usernames and passwords on routers and other network devices.
- Monitor DNS Settings: Regularly verify that router DNS settings point to legitimate, trusted DNS servers. Organizations should implement network monitoring to detect unauthorized DNS changes.
- Implement DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT): Where possible, use encrypted DNS protocols to prevent DNS hijacking and snooping.
- Network Segmentation: For businesses, segmenting networks can limit the lateral movement of attackers and contain the impact of a compromise.
- Employee Training: Educate users about the risks of phishing and the importance of reporting suspicious activities, even though this attack bypassed traditional phishing.
- Enhanced Logging and Monitoring: Implement robust logging and monitoring solutions for network devices to detect anomalous behavior, including unexpected DNS queries or configuration changes.
The adaptability of groups like Forest Blizzard means that the cybersecurity landscape is in constant flux. The shift from targeted malware to mass DNS hijacking highlights the need for a holistic security strategy that not only focuses on endpoint protection but also critically assesses the security posture of foundational network infrastructure. As digital transformation accelerates, the integrity of every network component, no matter how small or seemingly insignificant, becomes a potential vector for sophisticated state-sponsored attacks, demanding unwavering vigilance and proactive defense.