Daniil Shchukin Unmasked: German Authorities Name Alleged Mastermind Behind GandCrab and REvil Ransomware Empires
German authorities have definitively named Daniil Maksimovich Shchukin, a 31-year-old Russian national, as the elusive cybercriminal known by the handle "UNKN" (a.k.a. UNKNOWN), alleged to be the head of two of the most prolific and damaging ransomware-as-a-service (RaaS) groups in history: GandCrab and REvil. This significant breakthrough, announced by the German Federal Criminal Police (Bundeskriminalamt or BKA), provides a face and identity to the individual accused of orchestrating at least 130 acts of computer sabotage and extortion within Germany alone between 2019 and 2021, leading to economic damages exceeding 35 million euros and nearly 2 million euros in extorted payments. The unmasking of Shchukin, alongside alleged accomplice Anatoly Sergeevitsch Kravchuk, 43, marks a critical step in international law enforcement’s relentless pursuit of high-profile cybercriminals, offering a rare glimpse into the individuals behind the digital curtain of some of the most impactful cyberattacks of the past decade.
Unmasking the Enigma: The Hunt for UNKN
The revelation of Daniil Maksimovich Shchukin’s identity is the culmination of extensive international investigative efforts. For years, the figure known as UNKN or UNKNOWN operated with impunity in the shadowy corners of the internet, leading sophisticated cybercrime syndicates that leveraged advanced ransomware strains to cripple businesses, public institutions, and critical infrastructure worldwide. The BKA’s advisory specifically identifies Shchukin as the architect of these widespread campaigns, which pioneered innovative and devastating extortion tactics. While the BKA currently assumes Shchukin resides abroad, likely in Russia, and acknowledges the possibility of his international travel, the public identification serves as a powerful deterrent and a signal of the increasing capability of global law enforcement to penetrate the anonymity of the cyber underground.
Further supporting the BKA’s claims, Shchukin’s name surfaced in a February 2023 filing by the U.S. Justice Department. This filing sought the seizure of various cryptocurrency accounts linked to the proceeds of REvil’s illicit activities, directly tying a digital wallet containing over $317,000 in ill-gotten cryptocurrency to Shchukin. This financial trail provides concrete evidence of his alleged involvement and the significant financial gains derived from these criminal enterprises. The meticulous tracing of cryptocurrency transactions, often perceived as anonymous, highlights the evolving sophistication of cybercrime investigations.
The Reign of GandCrab: A Pioneer in Ransomware-as-a-Service
GandCrab emerged on the cybercrime landscape in January 2018, quickly establishing itself as a dominant force in the nascent RaaS market. This model allowed aspiring hackers, known as affiliates, to deploy GandCrab’s sophisticated malware against targets in exchange for a substantial share of the ransom payments. The GandCrab team, acting as the developers and operators of the RaaS program, would handle the technical infrastructure, malware development, and payment processing, taking a percentage of each successful extortion. This division of labor democratized ransomware attacks, making them accessible to a wider range of criminals who lacked the technical prowess to develop their own malware.
GandCrab’s success was unprecedented. Its operators constantly refined the malware, releasing five major revisions that incorporated new features, bug fixes, and evasive techniques designed to circumvent detection by cybersecurity firms. This continuous improvement ensured GandCrab remained potent and effective, contributing to its rapid spread and high success rate. The group was particularly adept at expanding initial access gained by affiliates, often siphoning vast quantities of sensitive and internal documents from compromised networks. This data exfiltration laid the groundwork for the "double extortion" tactic that would become a hallmark of its successor.
By May 31, 2019, the GandCrab team publicly announced its retirement, claiming to have extorted over $2 billion from victims globally. Their farewell message, audacious and defiant, famously quipped, "We are a living proof that you can do evil and get off scot-free… We have proved that one can make a lifetime of money in one year. We have proved that you can become number one by general admission, not in your own conceit." This statement, while a display of hubris, also underscored the immense profitability and perceived impunity that characterized the ransomware ecosystem at the time. Their departure, however, was not the end of their operations, but rather a strategic rebranding.
REvil’s Emergence: From Successor to "Big-Game Hunter"
Almost immediately following GandCrab’s announced cessation, the REvil (also known as Sodinokibi) ransomware affiliate program materialized. Fronted by a user identifying as UNKNOWN on a prominent Russian cybercrime forum, the new operation signaled its seriousness by depositing $1 million into the forum’s escrow service, a common practice to establish credibility and trust within the criminal underworld. Cybersecurity experts were quick to draw connections, with many concluding that REvil was largely a reorganization of the GandCrab operation, retaining much of its infrastructure, code, and, most critically, its leadership.
REvil took the "double extortion" model, pioneered by GandCrab, to new heights. This tactic involved not only encrypting a victim’s data and demanding payment for a decryption key but also stealing sensitive information and threatening to publish it publicly if a second, separate ransom was not paid. This added layer of pressure significantly increased the likelihood of victims paying, as the reputational damage and legal consequences of data exposure often outweighed the cost of the ransom.
Under UNKNOWN’s alleged leadership, REvil evolved into a feared "big-game-hunting" machine. The group strategically shifted its focus from smaller targets to large organizations with annual revenues exceeding $100 million, particularly those known to possess robust cyber insurance policies. These larger targets offered the promise of significantly higher payouts, transforming REvil into one of the most profitable and destructive cybercrime enterprises globally. Their meticulous targeting and sophisticated negotiation tactics cemented their reputation as a formidable adversary.
The Global Scourge of Ransomware: A Broader Context
The rise of GandCrab and REvil coincided with a dramatic escalation in ransomware attacks worldwide. Ransomware, which began as relatively unsophisticated "locker-ware" in the late 1980s, evolved into a pervasive and economically devastating threat by the 2010s. The adoption of cryptocurrencies for ransom payments provided a pseudo-anonymous transaction method, further fueling its growth. By 2021, the global cost of ransomware attacks was estimated to be in the tens of billions of dollars, affecting every sector from healthcare and education to critical national infrastructure.
The RaaS model, perfected by groups like GandCrab and REvil, transformed ransomware into a highly scalable criminal industry. It created a hierarchical ecosystem where developers, affiliates, initial access brokers (IABs), cryptor providers, and money launderers all played specialized roles. IABs would compromise networks and sell access to ransomware operators, while cryptor services ensured the malware remained undetected by antivirus software. Bitcoin "tumblers" or mixers were then used to obscure the origins of ransom payments, making them harder for law enforcement to trace. This professionalization of cybercrime mirrored legitimate business practices, with groups reinvesting profits into research, development, and talent acquisition to improve their operational success.

Law Enforcement’s Long Arm: International Cooperation and Digital Forensics
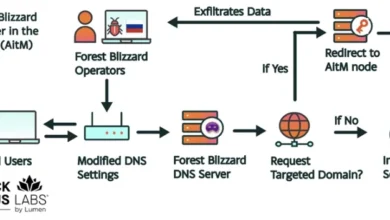
The unmasking of Shchukin underscores the increasing effectiveness of international law enforcement cooperation in combating sophisticated cybercrime. Despite the challenges posed by jurisdictional boundaries and the often-anonymous nature of online criminal activity, agencies like the BKA, in collaboration with partners such as the U.S. Justice Department and other global entities, have made significant strides. The ability to trace cryptocurrency, correlate online pseudonyms with real-world identities, and leverage intelligence from various sources has proven crucial.
A prime example of this concerted effort was the response to the infamous REvil attack on Kaseya over the U.S. July 4th weekend in 2021. Kaseya, a company providing IT management software to over 1,500 businesses, non-profits, and government agencies, became a conduit for a massive supply-chain ransomware attack. This incident highlighted REvil’s capability to cause widespread disruption. Crucially, the FBI later revealed they had infiltrated REvil’s servers prior to the Kaseya attack but chose not to reveal their presence to avoid tipping off the criminals and to gather more intelligence. This strategic compromise ultimately led to the release of a free decryption key for REvil victims, severely undermining the group’s operations and signaling a major blow to its credibility and profitability. REvil never fully recovered from this core compromise, demonstrating the profound impact of well-executed law enforcement interventions.
The ongoing investigation by the BKA, as detailed in their advisory, indicates a focus on the specific impact within Germany, where Shchukin and Kravchuk are accused of causing millions in damages and extorting substantial sums across dozens of attacks. This localized focus, combined with international intelligence sharing, is vital for building robust cases against globally operating cybercriminals.
The Anatomy of a Cybercrime Enterprise
The business model perfected by groups like GandCrab and REvil, as documented in works such as "The Ransomware Hunting Team" by Renee Dudley and Daniel Golden, illustrates a highly organized and adaptive criminal enterprise. These groups operated with a professionalism that mimicked legitimate businesses, outsourcing specialized tasks to a network of ancillary service providers.
- Ransomware Developers: Focused on improving the core malware, ensuring it was robust, difficult to decrypt, and resistant to security defenses.
- Initial Access Brokers (IABs): Specialized in infiltrating target networks, often by exploiting vulnerabilities or purchasing stolen credentials, and then selling this access to ransomware operators.
- Cryptor Providers: Developed custom loaders and packers to make the ransomware undetectable by standard anti-malware scanners, ensuring successful deployment.
- Money Launderers: Utilized services like Bitcoin tumblers or complex multi-hop transactions to obscure the flow of illicit funds, making them harder for authorities to trace.
- Negotiators/Support Staff: Some groups even hired individuals to handle negotiations with victims and provide "customer support" for decryption, further professionalizing the extortion process.
This ecosystem allowed ransomware gangs to scale rapidly, adapt to new defenses, and maintain a high success rate, driving the "monumental payments" that enabled them to reinvest in their operations. The criminal underworld became a marketplace for specialized services, with some contractors working exclusively with top-tier gangs, while others offered their services more broadly. This intricate network of collaborators highlights the complexity of dismantling these operations.
The Personal Behind the Pseudonym: Glimpses into UNKN’s Identity
While the BKA’s statement explicitly names Daniil Shchukin as UNKN, connecting his real-world identity to the online persona has been a complex process involving digital forensics and open-source intelligence. UNKNOWN, the frontman for REvil, famously gave an interview to Dmitry Smilyanets of Recorded Future, portraying a rags-to-riches narrative devoid of ethical constraints. "As a child, I scrounged through the trash heaps and smoked cigarette butts," UNKNOWN recounted. "I walked 10 km one way to the school. I wore the same clothes for six months. In my youth, in a communal apartment, I didn’t eat for two or even three days. Now I am a millionaire." This personal anecdote, while perhaps exaggerated for effect, painted a picture of a criminal motivated by extreme poverty and a desire for wealth, reflecting a common narrative among some cybercriminals.
Further investigation by cyber intelligence firm Intel 471, referenced in the original reporting, indicates connections between Shchukin and an earlier hacker identity known as "Ger0in." Active between 2010 and 2011, Ger0in operated large botnets and sold "installs"—a service allowing other cybercriminals to rapidly deploy their malware to thousands of compromised PCs. While Ger0in’s activity predates UNKNOWN’s appearance as the REvil frontman by several years, this potential earlier involvement suggests a longer history of sophisticated cybercrime activities for Shchukin, indicating a career trajectory within the criminal underworld that evolved from botnet operations to leading major ransomware syndicates.
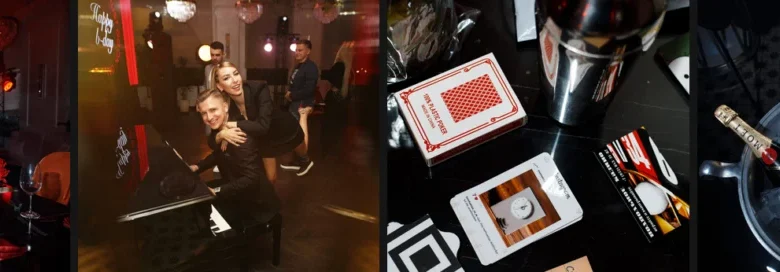
Adding another layer to the identification, mugshots released by the BKA were cross-referenced using image comparison sites, yielding a match to a birthday celebration from 2023. This event featured a young man named Daniel wearing a distinctive watch identical to the one seen in the BKA photos, providing a tangible link between the alleged cybercriminal and his public life in Krasnodar, Russia. Moreover, a 2023 conference talk in Germany (37C3) included an English-dubbed audio recording that previously outed Shchukin as the REvil leader, indicating that intelligence on his identity had been circulating within security circles prior to the BKA’s official announcement.
Implications and the Future of Cybercrime
The official unmasking of Daniil Maksimovich Shchukin as UNKN is a significant victory for law enforcement in the ongoing battle against ransomware. It demonstrates that even the most elusive and successful cybercriminals are not beyond the reach of justice, especially when international cooperation is robust. This identification serves as a powerful message to other high-profile ransomware operators that their anonymity is increasingly fragile.
However, the fight is far from over. While the public identification of key figures like Shchukin can disrupt existing operations and deter some individuals, the adaptable nature of cybercrime means that new groups and leaders will inevitably emerge. The underlying RaaS model, the availability of specialized services, and the global reach of the internet ensure that ransomware will continue to be a significant threat. The challenges of extradition and prosecution, particularly when alleged criminals reside in countries that do not cooperate with international law enforcement requests, remain substantial. Shchukin’s presumed residence in Russia highlights this ongoing geopolitical hurdle.
The continuous evolution of ransomware tactics, from double extortion to more recent trends like triple extortion (adding DDoS attacks or direct victim shaming), demands constant vigilance and adaptation from cybersecurity professionals and law enforcement alike. The case of Daniil Shchukin represents a critical milestone, offering valuable insights into the structure, motivation, and operational methods of top-tier ransomware groups, and reinforcing the commitment of global authorities to dismantle these destructive criminal networks. It underscores that while the digital realm may offer a cloak of anonymity, persistent investigative work, bolstered by digital forensics and international collaboration, can ultimately bring the faces behind the pseudonyms into the light.