Cybersecurity Firm Aims for Obsolescence by Eliminating Code Vulnerabilities

In a paradoxical yet compelling vision for the future of cybersecurity, the company AISLE is actively working towards a future where its core services become redundant. The ambitious goal, as articulated by co-founder Jaya Baloo, is the complete eradication of vulnerabilities within software code. This stands in contrast to the industry’s long-standing practice of identifying and mitigating these weaknesses, a process that has often proven to be a race against time with inconsistent success.
The cybersecurity landscape has long grappled with the challenge of not only discovering but also effectively remediating security flaws. A stark illustration of this persistent issue is the repeated presence of cross-site scripting (XSS) vulnerabilities within the OWASP Top 10 list of critical security risks for over a decade. This enduring presence underscores a systemic challenge in translating vulnerability discovery into tangible security improvements.
Recent advancements in artificial intelligence (AI) have further amplified this discussion. Anthropic’s unveiling of its Claude Mythos Preview project demonstrated the remarkable capacity of AI to uncover a vast number of vulnerabilities. Simultaneously, Anthropic’s Project Glasswing, a collaborative effort involving a select group of industry leaders, aims to develop advanced defensive mechanisms. However, these initiatives have not been without scrutiny. Critics have raised concerns that the sharing of exploit details, even in a controlled environment, could inadvertently empower malicious actors more than it aids defenders. They question whether such research should be confined to a limited circle of participants or if it poses a broader risk to the digital ecosystem.
"The ability to find vulnerabilities was never the primary question for us," stated Jaya Baloo, co-founder of AISLE. "We can discover vulnerabilities with AI. The significant point here is that Anthropic is not merely identifying vulnerabilities; their claim is that they are actively progressing through the exploit chain and delivering functional exploits. If one can engineer exploitability and discover newly emergent vulnerabilities, then an exploit chain can be constructed, potentially leading to the compromise of new entities."
Baloo posits that the broader industry, which was already struggling to keep pace with vulnerability remediation prior to the advent of sophisticated AI tools like those demonstrated by Anthropic, might be tempted to leverage the sheer volume of AI-discovered vulnerabilities as a convenient scapegoat for their inability to resolve these persistent issues. "And that is not true," she asserted. "Because we already face significant difficulties in identifying critical assets within our infrastructure. This complexity complicates our defense efforts, irrespective of the sheer volume of vulnerabilities that might be present."
The Evolution of AISLE’s Strategy: From Remediation to Reliable Detection
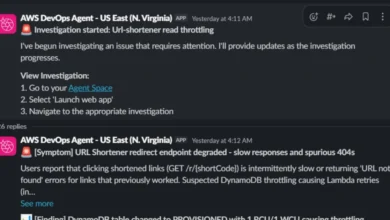
Initially, AISLE’s strategic focus was squarely on remediation, aiming to assist organizations in rectifying security flaws across their codebases, cloud environments, and broader infrastructure. This approach was predicated on leveraging existing scanning technologies. However, the company soon encountered a significant hurdle: these established scanners frequently generated a high volume of false positives, leading to wasted effort and misdirected resources, alongside critical false negatives that left genuine threats undetected. Recognizing this unreliability as a fundamental flaw in the foundational layer of vulnerability identification, AISLE pivoted its strategy.
The company then undertook the development of its own proprietary scanner, aptly named "Open Analyzer." This tool was designed to serve as a dependable source of initial truth for vulnerability findings, crucially operating without the need for proprietary, "gated" frontier models that often come with licensing restrictions and limited accessibility. While AISLE integrates with other scanning solutions, its primary emphasis remains on refining and improving the flawed detection processes that plague the industry.
Contextualizing Vulnerabilities: The Key to Effective Defense
A cornerstone of AISLE’s philosophy is the paramount importance of context in security scanning. Baloo elaborated that a vulnerability’s potential reachability from external sources is a critical factor, but it represents only one facet of the complete picture. True context enrichment involves a comprehensive understanding of an asset’s criticality, its architectural placement within the broader system, and its intricate dependencies across various repositories. This multi-layered contextual awareness significantly enhances the accuracy of scanner results, streamlines the triage process for identified issues, and ultimately leads to more effective and targeted remediation propositions.
Open-Source Power and Systemic Strength
AISLE operates on the conviction that the efficacy of a security solution hinges on the surrounding system rather than solely on the sophistication of the underlying AI model. The company’s rationale is that AI models will continue to evolve and improve at a rapid pace, and therefore, healthy competition should be centered on the robustness and intelligence of the framework that orchestrates these models, rather than the models themselves.
To underscore this point, AISLE successfully demonstrated that vulnerability discovery could be achieved using readily available, open-source, smaller language models (LLMs) operating in parallel. The results, the company claims, were comparable to those achieved by more advanced, proprietary models. Furthermore, AISLE’s own analyzer has demonstrated its capability to identify novel vulnerabilities that remained undetected by closed-source models, serving as empirical evidence for the superiority of their systems-based approach. In line with their commitment to open innovation, the company shares the Open Analyzer tool, focusing on proving the existence of vulnerabilities without providing the associated exploit chains.
The Ultimate Goal: A Vulnerability-Free Future
The overarching aspiration of AISLE is to render its own vulnerability finding and fixing services obsolete. This ambitious vision paints a future where secure coding practices are so deeply embedded that vulnerabilities are virtually eradicated. The company draws a parallel to the evolution of word processing, where spell-check functionality has largely eliminated common spelling errors, transforming it from a specialized service into an expected feature. Similarly, AISLE envisions a future where secure coding agents proactively prevent vulnerabilities from entering software from the outset.
The Urgent Need: Securing Cyber-Physical Systems and the Rise of Autonomous Agents
This imperative for heightened security is amplified by the rapid proliferation of cyber-physical systems, a category that now prominently includes advanced robotics, such as humanoid robots. Real-world security incidents underscore the urgency of addressing these vulnerabilities. The recent remote exploitation of Unitree robots serves as a potent case study.
Jaya Baloo recounted a disturbing incident: "Last year, around April, the robot dogs that are ubiquitous at every conference, the dogs that walk around everywhere – those are Unitree dogs. Those dogs were remotely exploitable. Then, a couple of months later, Unitree lost their encryption keys, and they wound up on the internet. But it gets even more concerning. Unitree also manufactures a humanoid robot. It turns out that if you obtain the encryption keys and transmit them over Bluetooth Low Energy to the humanoid robot, you gain root access on that robot. Subsequently, that robot can conduct local scans for all other devices within Bluetooth range, identifying and compromising all other robots, effectively creating your own robot army. We absolutely must fix these vulnerabilities because I do not want to find ourselves in an ‘I, Robot’ scenario."
The implications of such vulnerabilities are far-reaching. The ability to remotely commandeer and weaponize robots, especially interconnected ones, presents a significant threat to public safety and national security. The scenario described by Baloo highlights a chilling potential for cascading failures and widespread disruption, emphasizing that the race to secure these advanced systems is not merely an academic exercise but a critical necessity.
Baloo concluded with a stark warning: "Correcting these flaws is essential to safeguarding this increasingly interconnected world." The development of robust security protocols and the proactive elimination of vulnerabilities in cyber-physical systems are paramount to preventing a future where autonomous agents, intended for beneficial purposes, could be turned into instruments of chaos or control. The industry’s collective ability to meet this challenge will determine the safety and reliability of the increasingly automated and integrated world we are building.