Iranian-Linked Hacktivist Group Handala Claims Massive Data-Wiping Attack on Medical Technology Giant Stryker, Triggering Global Disruptions
A sophisticated and destructive cyberattack targeting Stryker, a global leader in medical technology, has caused widespread operational disruptions across the company’s international network, impacting healthcare supply chains and prompting urgent responses from industry stakeholders. The attack, which a hacktivist group known as Handala has claimed responsibility for, appears to be a data-wiping operation leveraging legitimate administrative tools, leading to thousands of employees being sent home and critical medical services being affected worldwide. This incident underscores the escalating threat of state-sponsored cyber warfare extending into critical civilian infrastructure, particularly in the sensitive medical sector.
The immediate fallout from the attack became evident today as news reports from Ireland, home to Stryker’s largest operational hub outside the United States, confirmed that over 5,000 employees were instructed to stay home. Simultaneously, a recorded message at Stryker’s main U.S. headquarters in Kalamazoo, Michigan, informed callers of a "building emergency." These early indicators painted a picture of a company grappling with a significant internal crisis, later revealed to be a far-reaching cyber onslaught. Stryker, a prominent manufacturer of medical and surgical equipment, reported a staggering $25 billion in global sales last year, making it a pivotal player in the healthcare ecosystem. The disruption to such a behemoth carries significant ramifications for hospitals and clinics relying on its products and services globally.
The Claim of Responsibility and Scope of the Attack
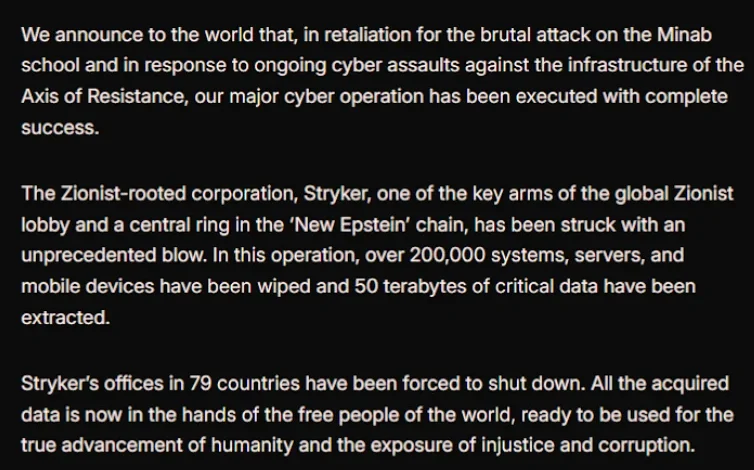
Hours after initial reports of disruptions surfaced, a lengthy statement posted on Telegram by Handala (also known as Handala Hack Team) unequivocally claimed responsibility for the cyberattack. The group, which security experts link to Iran’s intelligence agencies, asserted that Stryker’s offices in 79 countries had been forced to shut down. Their audacious claim included the erasure of data from "more than 200,000 systems, servers and mobile devices," a scale that, if accurate, represents one of the most significant data destruction events against a major corporation in recent memory.
Handala’s manifesto further declared, "All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption." This phraseology is typical of hacktivist groups seeking to justify their actions under a banner of social or political justice, often masking state-sponsored objectives. The group explicitly stated their motivation: the wiper attack was a direct retaliation for a missile strike on February 28 that reportedly hit an Iranian school, resulting in the deaths of at least 175 people, predominantly children. The New York Times today reported an ongoing military investigation had determined the United States was responsible for this deadly Tomahawk missile strike, providing the geopolitical context Handala leveraged for its cyber assault.
Profiling the Perpetrator: Handala’s Links to Iranian Intelligence
Handala is not a new entity in the complex landscape of state-sponsored cyber warfare. Cybersecurity firm Palo Alto Networks recently profiled the group, definitively linking it to Iran’s Ministry of Intelligence and Security (MOIS). According to Palo Alto, Handala emerged in late 2023 and is assessed to be one of several online personas maintained by "Void Manticore," a known MOIS-affiliated actor. This attribution is crucial as it elevates the incident from a mere criminal hack to a state-level cyber operation, indicating a clear intent and strategic deployment of resources.
Palo Alto Networks’ analysis of Handala’s activities reveals a primary focus on Israel, with occasional opportunistic targeting outside this scope when it serves a specific agenda. The security firm noted Handala had previously taken credit for attacks against fuel systems in Jordan and an Israeli energy exploration company. Their modus operandi, as described by Palo Alto researchers, involves "opportunistic and ‘quick and dirty’" tactics, often focusing on supply-chain footholds (such as IT/service providers) to reach downstream victims. These attacks are typically followed by "proof" posts designed to amplify credibility and intimidate targets, aligning perfectly with their public Telegram statement regarding Stryker. The group’s manifesto referred to Stryker as a "Zionist-rooted corporation," likely a reference to Stryker’s 2019 acquisition of the Israeli company OrthoSpace, providing a specific ideological justification for their actions against the medical technology giant.
Technical Execution: A Remote Wipe via Microsoft Intune
While "wiper attacks" typically involve deploying malicious software designed to overwrite existing data on infected devices, the method employed in the Stryker incident appears to have been subtly different, yet equally devastating. A trusted source with knowledge of the attack, who spoke on condition of anonymity, informed KrebsOnSecurity that the perpetrators seemingly leveraged a Microsoft service known as Microsoft Intune to issue a ‘remote wipe’ command against all connected devices.
Microsoft Intune is a cloud-based solution specifically designed for IT teams to enforce security and data compliance policies. It offers a single, web-based administrative console for monitoring and controlling devices, irrespective of their physical location. The ability of attackers to commandeer such a powerful, legitimate administrative tool highlights a severe security breach, potentially at the identity or credential level. This method could bypass traditional endpoint detection systems that look for known malicious executables, instead utilizing authorized system functions for destructive purposes. Further corroboration for this theory emerged from a Reddit discussion on the Stryker outage, where several users claiming to be Stryker employees reported being urgently instructed to uninstall Intune, suggesting the company was actively trying to mitigate the damage caused by the compromised service. The Irish Examiner also reported that "anyone with Microsoft Outlook on their personal phones had their devices wiped," and that login pages on company devices were defaced with the Handala logo, further indicating a broad, destructive sweep.
Stryker’s Global Footprint and the Ripple Effect on Healthcare
With 56,000 employees spread across 61 countries, Stryker is not merely a vendor but an integral component of the global healthcare infrastructure. Its diverse portfolio includes surgical instruments, implants, medical and surgical equipment, and neurotechnology products that are vital for a vast array of medical procedures, from routine surgeries to emergency interventions. The attack, therefore, is not just a corporate headache; it represents a direct threat to patient care and public health globally.
The implications of such a widespread disruption are profound. A healthcare professional at a major university medical system in the United States, who requested anonymity due to not being authorized to speak to the press, confirmed immediate difficulties. "This is a real-world supply chain attack," the expert stated. "Pretty much every hospital in the U.S. that performs surgeries uses their supplies." This dependency means that even a temporary halt in Stryker’s operations can have cascading effects, potentially delaying critical surgeries, impacting inventory management, and forcing healthcare providers to scramble for alternative suppliers in an already strained global supply chain.
Industry Response and Emerging Concerns
The American Hospital Association (AHA), a national organization that represents and serves all types of hospitals, quickly acknowledged the severity of the situation. John Riggi, national advisor for the AHA, commented, "We are aware of reports of the cyber attack against Stryker and are actively exchanging information with the hospital field and the federal government to understand the nature of the threat and assess any impact to hospital operations." While Riggi initially noted that the AHA was "not aware of any direct impacts or disruptions to U.S. hospitals as a result of this attack" as of that moment, he cautioned that this assessment "may change as hospitals evaluate services, technology and supply chain related to Stryker and if the duration of the attack extends." This cautious optimism reflects the lag often seen in reporting and confirming supply chain disruptions, especially in a sector as complex as healthcare.
More specific concerns began to surface through official channels. A March 11 memo from the state of Maryland’s Institute for Emergency Medical Services Systems revealed that Stryker had indicated some of its computer systems were impacted by a "global network disruption." In response, several hospitals opted to disconnect from Stryker’s various online services as a precaution. One particularly critical service affected is LifeNet, which paramedics utilize to transmit EKGs (electrocardiograms) to emergency physicians. This allows for rapid diagnosis and expedited treatment for heart attack patients (STEMI) upon their arrival at the hospital. Timothy Chizmar, Maryland’s EMS medical director, acknowledged the disruption, stating, "As a precaution, some hospitals have temporarily suspended their connection to Stryker systems, including LIFENET, while others have maintained the connection." He advised that while Maryland Medical Protocols for EMS require ECG transmission for acute coronary syndrome patients, if transmission is impossible, paramedics "should initiate radio consultation and describe the findings on the ECG." This workaround, while functional, highlights the increased operational burden and potential for delays in critical care that such cyberattacks impose.
Broader Implications: Cybersecurity in Critical Infrastructure and Geopolitical Tensions
The Stryker cyberattack serves as a stark reminder of the inherent vulnerabilities within critical infrastructure, particularly when geopolitical tensions spill over into the digital realm. The healthcare sector, with its reliance on interconnected systems, sensitive patient data, and intricate supply chains, presents a lucrative and impactful target for state-sponsored actors. The use of a data-wiping attack, designed for maximum destruction rather than data theft, signifies an intent to inflict operational paralysis and economic damage, rather than financial gain or espionage. This escalation underscores a growing trend where cyberattacks are being used as instruments of foreign policy, capable of inflicting real-world consequences without traditional military engagement.
The incident also raises serious questions about the security posture of global enterprises, especially those operating across numerous jurisdictions and managing complex IT environments. The alleged exploitation of Microsoft Intune, a widely used cloud management tool, suggests that even robust enterprise solutions can be turned against an organization if fundamental security principles, such as identity and access management, are compromised. Companies must not only defend against sophisticated malware but also ensure the integrity of their administrative tools and the credentials that control them.
As this developing story unfolds, the full extent of the damage to Stryker’s operations, its financial impact, and the long-term consequences for healthcare providers and patients worldwide remain to be seen. The incident highlights the urgent need for enhanced cybersecurity resilience across all critical sectors, robust intelligence sharing between government and industry, and a concerted international effort to de-escalate cyber warfare that increasingly threatens global stability and human well-being. The attack on Stryker stands as a potent symbol of the complex, interconnected threats that define the modern geopolitical and technological landscape.








