Tentacles of ‘0ktapus’ Threat Group Victimize 130 Firms

A sophisticated and widespread phishing campaign, dubbed "0ktapus" by cybersecurity researchers, has ensnared over 130 organizations, compromising 9,931 user accounts by meticulously spoofing multi-factor authentication (MFA) systems. The campaign, which specifically targeted the identity and access management firm Okta, has been linked to high-profile breaches affecting major technology companies such as Twilio and Cloudflare, underscoring the escalating threat landscape for digital identities and the pervasive risk of supply chain attacks.
The 0ktapus campaign represents a significant escalation in phishing tactics, moving beyond simple credential theft to actively bypass robust MFA protections. Cybersecurity firm Group-IB, which first identified and detailed the campaign in a comprehensive report, highlighted the attackers’ primary objective: to illicitly obtain Okta identity credentials and corresponding MFA codes from unsuspecting users. These users were targeted via expertly crafted text messages, known as SMS phishing or smishing, containing malicious links that redirected them to deceptive websites meticulously designed to mimic their organization’s legitimate Okta authentication page.
The sheer scale of the operation is staggering, with 114 U.S.-based firms among the victims, alongside additional organizations scattered across 68 other countries. Roberto Martinez, a senior threat intelligence analyst at Group-IB, emphasized the potentially far-reaching consequences of the campaign, stating, "The 0ktapus campaign has been incredibly successful, and the full scale of it may not be known for some time." This statement hints at the possibility of a larger, as-yet-undiscovered impact, a common characteristic of advanced persistent threats that often lay dormant or operate covertly for extended periods.
Unpacking the 0ktapus Modus Operandi: A Multi-Phase Attack
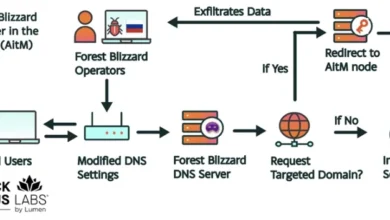
The 0ktapus campaign was not a simplistic, one-off phishing attempt but a multi-phased, well-orchestrated operation demonstrating a deep understanding of corporate identity management systems and human psychology. Researchers believe the attackers initiated their campaign by strategically targeting telecommunications companies. While the precise method by which threat actors acquired lists of phone numbers for their MFA-related attacks remains under investigation, one prevailing theory posits that the initial breach of mobile operators and telecom firms served as a crucial reconnaissance phase. By gaining access to these entities, the attackers could potentially harvest phone numbers, internal directories, or even leverage network access to facilitate their smishing campaign more effectively.
"According to the compromised data analyzed by Group-IB, the threat actors started their attacks by targeting mobile operators and telecommunications companies and could have collected the numbers from those initial attacks," Group-IB researchers elaborated in their report. This initial targeting of infrastructure providers is a classic pre-attack maneuver, allowing threat actors to build a robust foundation for subsequent, more targeted assaults.
Once equipped with relevant phone numbers, the attackers progressed to the second phase: direct engagement with targets. They dispatched phishing links via text messages, meticulously crafted to appear legitimate. These links led to cloned webpages that replicated the Okta authentication portal used by the victim’s employer. On these fake pages, users were prompted to submit their Okta identity credentials—username and password—along with the crucial multi-factor authentication (MFA) code, typically a one-time password (OTP) or a push notification approval. By tricking users into entering both sets of credentials on the malicious site, the attackers effectively bypassed the MFA layer, gaining unauthorized access to corporate accounts.
The Ultimate Goal: Enabling Supply Chain Attacks
Beyond mere credential theft, Group-IB’s accompanying technical blog post revealed a more sinister long-term objective for the 0ktapus attackers. The initial compromises, predominantly of software-as-a-service (SaaS) firms, were identified as "phase-one" in a broader, multi-pronged attack strategy. The ultimate goal of 0ktapus was to gain access to company mailing lists or customer-facing systems. This access would then serve as a springboard for facilitating more damaging supply-chain attacks.
Supply chain attacks are particularly insidious because they leverage the trust relationship between an organization and its vendors, partners, or customers. By compromising a trusted entity, attackers can then distribute malware, launch further phishing campaigns, or gain access to downstream targets, creating a ripple effect of breaches across an interconnected ecosystem. For instance, gaining control of a company’s mailing list could allow the attackers to send highly convincing phishing emails from a seemingly legitimate source, targeting the company’s clients or partners. Similarly, access to customer-facing systems could enable data exfiltration or the injection of malicious code into products or services. This sophisticated objective elevates the 0ktapus campaign from a simple data breach to a strategic threat against the digital economy’s interconnected fabric.
High-Profile Casualties: Twilio, Cloudflare, and DoorDash
The widespread nature of the 0ktapus campaign became acutely clear with the revelation that several prominent technology companies had fallen victim. Twilio, a major cloud communications platform, and Cloudflare, a leading web infrastructure and security company, both confirmed breaches tied to this campaign. While the specific details of the impact on each company varied, the common thread was the exploitation of employee credentials and MFA codes through the Okta spoofing technique.
In a stark example of the campaign’s immediate impact, the food delivery service DoorDash revealed it was targeted in an attack bearing all the hallmarks of an 0ktapus-style operation, mere hours after Group-IB published its initial report. In a blog post, DoorDash confirmed that an "unauthorized party used the stolen credentials of vendor employees to gain access to some of our internal tools." This access allowed the attackers to steal personal information, including names, phone numbers, email addresses, and delivery addresses, from both customers and delivery personnel. The incident at DoorDash serves as a tangible illustration of the direct consequences of such credential compromise, leading to sensitive customer data exposure and potential reputational damage.
The Group-IB report also specified that the attackers compromised 5,441 MFA codes during the course of their campaign. This statistic highlights the effectiveness of their phishing methodology in circumventing a security measure widely considered a robust defense against unauthorized access.
The Vulnerability of MFA: A Critical Reassessment
The success of the 0ktapus campaign forces a critical re-evaluation of the efficacy of traditional MFA methods, particularly those relying on SMS-based one-time passwords or push notifications that can be phished. While MFA is undeniably a significant improvement over password-only authentication, the campaign demonstrates that it is not an impenetrable shield.
"Security measures such as MFA can appear secure… but it is clear that attackers can overcome them with relatively simple tools," Group-IB researchers noted. This sentiment was echoed by Roger Grimes, a data-driven defense evangelist at KnowBe4, who commented via email, "This is yet another phishing attack showing how easy it is for adversaries to bypass supposedly secure multifactor authentication. It simply does no good to move users from easily phish-able passwords to easily phish-able MFA. It’s a lot of hard work, resources, time, and money, not to get any benefit."
Grimes’s pointed critique underscores a growing concern within the cybersecurity community: not all MFA is created equal. While FIDO2-compliant security keys, which rely on cryptographic hardware and are resistant to phishing, offer a superior level of protection, many organizations still rely on less secure, phish-able forms of MFA. The convenience of SMS OTPs or app-based push notifications often comes at the cost of vulnerability to sophisticated social engineering and phishing attacks that trick users into approving or entering codes on malicious sites.
Broader Implications and Industry Response
The 0ktapus campaign is part of a larger, evolving threat landscape where identity providers and authentication systems have become prime targets for cybercriminals. In early 2022, the Lapsus$ hacking group also targeted Okta, compromising a third-party contractor and gaining access to internal systems, further illustrating the persistent threat to these critical identity infrastructure components. The interconnectedness of modern IT environments means that a breach at one foundational service provider like Okta can have cascading effects across hundreds, if not thousands, of downstream organizations.
Beyond the immediate technical implications, such large-scale breaches carry significant regulatory and financial repercussions. Companies face potential fines under data protection regulations like GDPR or CCPA, the cost of incident response, legal fees, reputational damage, and potential customer churn. The average cost of a data breach has steadily risen over the years, with recent industry reports indicating figures well into the millions of dollars per incident, depending on the scale and nature of the data compromised.
To mitigate the risks posed by 0ktapus-style campaigns, cybersecurity experts are advocating for a multi-faceted approach. Group-IB researchers specifically recommended "good hygiene around URLs and passwords" and, crucially, the adoption of FIDO2-compliant security keys for MFA. FIDO2 (Fast IDentity Online) standards, often implemented via hardware security keys like YubiKeys, offer strong, phishing-resistant authentication by verifying the origin of the login request and ensuring the user is interacting with the legitimate service, not a spoofed site. This cryptographic approach makes it exceedingly difficult for attackers to intercept or trick users into providing credentials to a fake domain.
Furthermore, continuous and effective security awareness training remains paramount. As Roger Grimes emphasized, "Whatever MFA someone uses, the user should be taught about the common types of attacks that are committed against their form of MFA, how to recognize those attacks, and how to respond. We do the same when we tell users to pick passwords but don’t when we tell them to use supposedly more secure MFA." This highlights a critical gap in many organizations’ security postures: while technology provides tools, human vigilance and education are equally vital in preventing successful attacks. Users must be educated to scrutinize URLs, verify sender identities, and understand the specific mechanisms of their MFA to detect and report suspicious activity.
The Future of Digital Identity Security
The 0ktapus campaign serves as a stark reminder that the battle for digital identity is intensifying. As organizations increasingly migrate to cloud-based services and adopt remote work models, identity becomes the new perimeter. Threat actors are adapting their tactics, evolving from brute-force attacks and simple phishing to highly sophisticated social engineering and MFA bypass techniques. The focus is shifting from merely protecting endpoints to securing the entire identity lifecycle.
The incident underscores the need for organizations to:
- Implement Phishing-Resistant MFA: Prioritize the adoption of FIDO2-compliant hardware security keys or certificate-based authentication over SMS or app-based OTPs where feasible.
- Enhance Employee Training: Regularly educate employees on the latest phishing techniques, emphasizing the importance of scrutinizing links, verifying sources, and never entering credentials on unverified pages.
- Strengthen Supply Chain Security: Conduct thorough due diligence on third-party vendors, implement strict access controls, and monitor vendor access to internal systems.
- Continuous Monitoring and Threat Intelligence: Deploy advanced threat detection systems and subscribe to robust threat intelligence feeds to identify emerging threats and indicators of compromise proactively.
- Incident Response Planning: Develop and regularly test comprehensive incident response plans to ensure a swift and effective reaction to potential breaches.
The 0ktapus campaign, with its widespread impact and sophisticated methodology, stands as a critical case study in the ongoing arms race between cyber defenders and attackers. It unequivocally demonstrates that even seemingly robust security measures like MFA can be circumvented, emphasizing the urgent need for organizations to continuously adapt their defenses, invest in advanced security technologies, and, critically, empower their human firewall through ongoing education and awareness. The security of the interconnected digital world depends on it.