AI-Powered Exploitation Accelerates Threat Landscape, Demanding Urgent Defensive Modernization
The cybersecurity world is facing an unprecedented acceleration in threat capabilities, driven by advancements in artificial intelligence. General-purpose AI models are demonstrating a remarkable aptitude for discovering software vulnerabilities, a task that traditionally required highly specialized human expertise and significant time investment. This evolution presents a critical juncture, creating a narrow but potent window of risk as organizations race to integrate AI into their defensive strategies while adversaries concurrently leverage the same technology to uncover and exploit novel weaknesses at machine speed. The traditional cybersecurity paradigm, built on human-paced response, is no longer sufficient to counter the emerging threat landscape.
This shift was highlighted in a recent analysis by Google Threat Intelligence (GTIG) and Mandiant, which underscores the urgent need for organizations to fortify their defenses and adapt their operational playbooks. As AI’s offensive capabilities mature, the gap between vulnerability discovery and widespread exploitation is rapidly shrinking, threatening to overwhelm existing security postures. The implications are profound, potentially enabling mass exploitation campaigns, sophisticated ransomware operations, and an increase in the overall volume and velocity of cyberattacks.
The Evolving Adversary Lifecycle: AI as an Exploit Accelerator
Historically, the discovery of zero-day vulnerabilities and the subsequent development of exploits were the domain of highly skilled, resource-intensive threat actors. This process often involved meticulous code analysis, reverse engineering, and extensive testing, consuming weeks or months. However, the advent of advanced AI models is dramatically altering this landscape. These models can now autonomously identify complex vulnerabilities within software code, and increasingly, assist in generating functional exploit code. This democratizes a capability previously held by a select few, significantly lowering the barrier to entry for a wider range of threat actors, including those with less technical expertise.
Google Threat Intelligence has already observed threat actors actively leveraging Large Language Models (LLMs) for these purposes. Furthermore, underground forums are witnessing the marketing and sale of AI-powered exploit development tools and services, signaling a growing commoditization of these offensive capabilities. This trend suggests a fundamental shift in the economics of zero-day exploitation, where the cost and effort associated with developing and deploying exploits will decrease, while the potential for mass exploitation and lucrative extortion operations will increase.
The acceleration of exploit deployment is not a theoretical future threat; it is a trend already being observed among sophisticated adversaries. Google’s "2025 Zero-Days in Review" report, for instance, detailed how espionage operators with ties to the People’s Republic of China (PRC) have become exceptionally adept at rapidly developing and distributing exploits across disparate threat groups. This has significantly compressed the historically observed timeframe between the public disclosure of a vulnerability and its widespread exploitation in the wild, a phenomenon expected to intensify.
Scaling Defenses for Machine-Speed Threats
The cybersecurity community has long anticipated the potential for AI to revolutionize vulnerability discovery. Indeed, Google has been at the forefront of leveraging AI in its own defensive operations for years, employing tools like Big Sleep, CodeMender, and OSS-Fuzz to proactively identify and remediate vulnerabilities. These internal efforts highlight a proactive approach to harnessing AI for security.
However, the current scenario presents a dual challenge: not only must defenders continue to harden existing software, but they must also prepare for an onslaught of novel exploits generated at machine speed. Traditional security tooling, often reliant on human-speed patching protocols and manual triage, will be fundamentally inadequate to cope with an AI-enabled surge in vulnerabilities. The sheer volume of alerts and the speed at which new exploits can be weaponized will likely lead to severe overload and burnout for security and development teams.
The critical question for organizations is no longer solely about proactive scanning and adhering to traditional Service Level Agreements (SLAs) for patching. It is about empowering their workforce with the automation necessary to eliminate manual toil and respond to threats at an equivalent pace. This necessitates a strategic shift in the role of the security practitioner, moving from a manual investigator to a strategic coordinator capable of orchestrating AI-driven defense mechanisms.
A Modern, AI-Integrated Defensive Roadmap
To effectively modernize vulnerability management and prepare for AI-enabled threats, organizations must embrace automation and prioritize resilience. The traditional vulnerability management roadmap, designed for human-speed threats, is ill-equipped to handle adversaries that can identify, chain, and weaponize weaknesses faster than conventional programs can respond. A modern roadmap must therefore emphasize automation, resilience, and continuous validation.

This roadmap can be broadly categorized into two tiers: advanced modernization priorities for organizations ready to evolve their security programs to meet AI-enabled speeds, and foundational guidance for those still building core vulnerability management capabilities.
Advanced Modernization Priorities
For organizations with mature security programs, the focus shifts to advanced strategies designed for AI-speed defense.
Secure Your Code
The traditional focus on securing tangible assets like laptops and servers is no longer sufficient. In the current threat landscape, source code, code libraries, and the systems used for building and deploying software are equally critical targets. Code repository platforms must be rigorously protected, with access restricted to trusted internal networks and managed through strong identity controls. Proactive scanning for secrets within codebases is paramount to prevent adversaries from weaponizing exposed credentials.
Organizations remain accountable for vulnerabilities originating from their software supply chains. This presents a complex challenge: balancing the need to update to the latest versions with the risk of introducing new vulnerabilities or disrupting trusted, known-good versions. Security controls must extend to build runners, CI/CD pipelines, and other automated execution mechanisms, which are increasingly attractive targets for sophisticated threat actors.
AI-enabled scanning tools can significantly accelerate the detection of critical vulnerabilities and identify patterns of weaknesses that, while minor individually, can be chained together by AI to achieve a critical breach. Frameworks like the Wiz SDLC Threat Framework (SITF) can help organizations map their Software Development Life Cycle (SDLC) threat models and identify these potential "attack chains." Furthermore, static and dynamic scanning alone are insufficient. Organizations should deploy emerging commercial and open-source agentic solutions that can continuously review code and mitigate flaws before they can be exploited.
Move to Automated Security Operations
Traditional security dashboards and static detection rules will buckle under the weight of AI-driven attacks. Security operations must evolve into a more dynamic, agentic Security Operations Center (SOC). Legacy models, often reactive and constrained by manual workflows, are ill-suited for machine-speed threats.
By deploying specialized AI agents, such as Google Cloud’s Triage and Investigation Agent and Gemini within Google Security Operations, security teams can automate alert triage, analyze suspicious code without manual reverse engineering, correlate signals across diverse tools, and generate response playbooks in real-time. This automation frees up human analysts to focus on high-value decision-making, enabling the SOC to respond to AI-enabled attacks at AI speed.
Reduce Attack Surface
A zero-trust approach to network design is essential. Organizations must prioritize reducing exposure across internet-facing systems, critical infrastructure, control planes, and trusted service infrastructure. Network segmentation and identity-based access controls are crucial to limit the blast radius of any compromise, even if an edge device is breached through a zero-day exploit.
Maintain Continuous Asset Discovery and Posture Management
Unidentified assets represent a significant blind spot and a critical weakness that AI-enabled threat actors can exploit with increasing efficiency. Static spreadsheets and manual asset tracking are no longer viable or scalable. Security teams require a continuously updated, automated inventory encompassing endpoints, servers, public-facing systems, network infrastructure, AI systems, cloud environments, and ephemeral assets like Kubernetes pods. Dynamic asset discovery is vital for eliminating blind spots and identifying "shadow AI" deployments. Seamless integration of asset data into downstream security tooling enhances the accuracy and effectiveness of frontline detection and response.
Expand Automated Scanning Coverage
Automated vulnerability scanning should encompass all major operating systems in use, including Windows, macOS, and Linux, across both endpoints and servers. This comprehensive visibility is critical for reducing blind spots. Wherever possible, this visibility should feed directly into automated remediation pipelines to ensure vulnerabilities are addressed rapidly.

Enhance Network Device Patching and Limit Connectivity
Organizations require highly automated, repeatable processes for identifying missing firmware and security updates on network devices and for efficiently scheduling maintenance. Network infrastructure has long been a preferred target for sophisticated threat actors, and AI will only accelerate the discovery of weaknesses in these often-overlooked systems. Perimeter controls should be used to block unnecessary outbound connections from internal network devices. Any attempt by these devices to communicate externally should be investigated to determine if it is required for normal operations or signals malicious activity. Establishing baselines for normal outbound connections is crucial for alerting against anomalies.
Formalize Emergency Remediation SLAs
While AI can accelerate patching, emergency response still hinges on clear human processes. Organizations must define remediation SLAs based on vulnerability severity, exposure, and asset criticality. These expectations need to be aligned across security, IT, and business stakeholders. When a vulnerability is actively exploited in the wild, teams require a pre-approved, low-friction process to apply temporary mitigations, such as restricting public access or isolating affected systems, while permanent fixes are validated. For extremely critical business processes, having secondary systems that can deliver the same objectives with different underlying technologies provides greater flexibility for emergency remediation while minimizing business disruption.
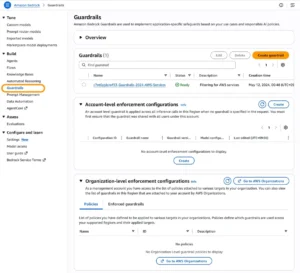
Secure AI Agents and Implement SAIF
As organizations deploy AI agents, they concurrently create new attack surfaces that require robust protection. Frameworks such as Google’s Secure AI Framework (SAIF) provide guidance for the secure deployment of AI models and applications. Tools like Google Cloud Model Armor can serve as a protective layer for LLM environments by screening inputs and outputs for prompt injection and jailbreak attempts. Google Cloud Sensitive Data Protection can prevent sensitive data leakage. Locking down connections that AI systems can establish, such as those via Management Center Proxy (MCP), with fine-grained IAM roles is critical to prevent insecure plugin use threats. Defensive AI systems must be secured with the same rigor as any other critical infrastructure to prevent them from becoming points of compromise.
Foundational Vulnerability Management Priorities
Not all organizations possess mature security programs. For those with limited or inconsistent vulnerability management capabilities, the immediate priority is to establish a reliable foundation before pursuing advanced AI-enabled operating models.
The Current Reality of Vulnerability Management
Vulnerability management programs vary significantly based on an organization’s overall security maturity. In mature environments, these programs are highly automated, with vulnerabilities identified, routed to appropriate owners, and automatically validated upon remediation. In less mature environments, vulnerability management is often inconsistent, narrowly scoped, and may focus primarily on high-profile zero-day threats. Tracking may still rely on manual methods like spreadsheets, leading to overlooked systems, including critical infrastructure like Active Directory domain controllers, remaining unpatched.
Such organizations must immediately modernize and elevate their vulnerability management programs. The increasing volume of AI-enabled threats exacerbates the challenge for organizations already struggling to remediate all identified vulnerabilities, underscoring the urgency of building automated, measurable, tracked, and validated programs. Achieving this requires coordination across the foundational pillars of any security program: people, process, and technology.
Foundation Step #1 – Baseline Current State
Begin by assessing existing tools, processes, and coverage. Scan all in-scope systems, identify Critical and High findings, and remediate them according to agreed-upon urgency and service levels. Concurrently, establish a process for tracking vulnerabilities actively exploited in the wild and the emergency patching actions they may necessitate. This phase should also confirm that system owners have defined maintenance windows and the operational support required to meet remediation SLAs.
Foundation Step #2 – Expand System Scanning Coverage
Broaden vulnerability scanning across all major operating systems in use, including Windows, macOS, and Linux, for both endpoints and servers. Extend coverage to other network-attached systems, including network devices themselves. The objective is to reduce blind spots and ensure vulnerability visibility across the entire environment, not just isolated segments.
Foundation Step #3 – Confirm Asset Inventory and Ownership
Maintain a simple, accurate inventory of key asset classes, including endpoints, servers, public-facing systems, network infrastructure, and specialized devices. Each asset must have a clearly defined owner responsible for remediation coordination, exception handling, and lifecycle accountability.
Foundation Step #4 – Establish Standard Program Reporting
Create a consistent reporting cadence that provides stakeholders with a clear view of program health and risk. Reporting should encompass scanning coverage by asset class, top Critical and High vulnerabilities, public-facing exposure, patch compliance, SLA performance, and documented exceptions or risk acceptances. The goal is to generate reports that drive decision-making, not just dashboards for visibility.

Foundation Step #5 – Prioritize Public-Facing and High-Risk Vulnerabilities
Identify the attack surface and prioritize vulnerabilities affecting internet-exposed systems, critical infrastructure, and assets that present the highest likelihood of exploitation or business impact. Track remediation against defined deadlines, with clear escalation paths for at-risk timelines. Where possible, engineer internet-exposed systems for automatic patching.
Foundation Step #6 – Develop a Specialized Process for High-Sensitivity Devices
For device classes requiring additional coordination, such as medical devices, industrial control systems, or other operational technology, create a streamlined process for identifying vulnerabilities, coordinating with vendors or support teams, and applying compensating controls when patching is not feasible. These assets often necessitate a different remediation model than standard IT systems.
Foundation Step #7 – Formalize Remediation SLAs and Exception Handling
Define remediation SLAs based on severity, exposure, and asset criticality, ensuring they are understood across security, IT, and business stakeholders. Establish a formal exception process for situations where remediation cannot be completed within the required timeframe. Exceptions must be documented, risk-assessed, approved by appropriate stakeholders, and reviewed periodically.
How Google Can Help
In today’s cybersecurity landscape, organizations are not only defending against human attackers but also against tactics amplified by AI tools. To counter these machine-speed threats, Google offers a comprehensive, AI-integrated defensive ecosystem. This includes advanced threat intelligence, AI-powered security operations platforms, and robust cloud security solutions designed to provide visibility, automate detection, and accelerate response across the entire enterprise.
Outlook and Implications
The cybersecurity community has an opportunity to lead with reason and proactive, disciplined preparation rather than succumbing to panic. While access to the most capable frontier AI models is currently restricted to responsible actors, the broader availability of these technologies is inevitable. This signals an impending surge in vulnerability management demands for defenders. The traditional window between vulnerability disclosure and active exploitation has largely vanished, leaving organizations to contend with an overwhelming number of simultaneous exploit threats.
Furthermore, the traditional concept of vulnerability severity is undergoing a fundamental shift. In an environment where AI agents can chain together multiple low-level vulnerabilities, the practical impact difference between a remote code execution (RCE) flaw and a seemingly benign local-only exploit is rapidly diminishing.
To build upon the foundational steps outlined, organizations can partner with Mandiant to plan, prioritize, and implement an AI-enabled cyber defense strategy. AI offers security teams powerful new avenues for understanding their environments, automating remediation at scale, and enhancing workforce capabilities. By adopting AI-integrated defenses today, organizations can better prepare for the speed, scale, and sophistication of tomorrow’s adversaries.
Acknowledgement
This comprehensive analysis was made possible through the collective expertise of numerous professionals across Mandiant and Google Threat Intelligence (GTIG). Special thanks are extended to Omar ElAhdan, Chris Linklater, Austin Larsen, Jared Semrau, Dan Nutting, John Hultquist, and Kimberly Goody for their invaluable contributions to this post.