Payouts King Ransomware Leverages QEMU Virtual Machines to Evade Endpoint Security and Establish Covert Backdoors

The Payouts King ransomware operation has been identified employing a sophisticated evasion technique, utilizing the open-source QEMU emulator to establish hidden virtual machines (VMs) on compromised systems. This method allows the threat actors to create reverse SSH backdoors, effectively bypassing conventional endpoint security solutions and facilitating discreet malicious activities.
This revelation, detailed by cybersecurity researchers at Sophos, highlights a concerning evolution in ransomware tactics. QEMU, primarily known as a legitimate CPU emulator and system virtualization tool, enables users to run various operating systems as VMs on a host computer. Its inherent capability to isolate environments provides a significant advantage to attackers: security solutions on the host system are typically unable to peer into these virtualized instances, creating a blind spot for detection. This allows threat actors to execute payloads, store malicious files, and establish covert remote access tunnels over SSH without immediate detection.
A Growing Trend of QEMU Abuse
The use of QEMU by malicious actors is not an entirely novel development but marks a persistent and evolving challenge for cybersecurity defenses. Historically, several prominent threat groups have leveraged QEMU for similar clandestine operations. For instance, the 3AM ransomware group has been documented employing QEMU to facilitate its attacks, likely for payload delivery and evasion. Similarly, the LoudMiner cryptomining operation famously abused virtual machines to covertly mine cryptocurrency on both Windows and macOS systems, demonstrating the cross-platform utility of such an approach. Even sophisticated phishing campaigns, such as those attributed to ‘CRON#TRAP,’ have incorporated backdoored Linux VMs to establish persistence and evade detection. These past incidents underscore QEMU’s established utility within the cybercriminal toolkit for its ability to create isolated, stealthy operational environments.
Sophos researchers documented two distinct campaigns that prominently feature QEMU as a core component of their attack infrastructure. One campaign, internally tracked as STAC4713, emerged in November 2025 and has been directly linked to the Payouts King ransomware operation. The second, designated STAC3725, was observed in February of the current year and notably exploits the critical CitrixBleed 2 vulnerability (CVE-2025-5777) affecting NetScaler ADC and Gateway instances. These campaigns illustrate a diverse set of initial access vectors and target profiles, yet converge on the use of QEMU for post-exploitation stealth and persistence.

Payouts King: The STAC4713 Campaign and GOLD ENCOUNTER
The STAC4713 campaign, attributed to the Payouts King ransomware, is associated with the GOLD ENCOUNTER threat group, known for its focus on targeting hypervisors and encrypting data within VMware and ESXi environments. This association suggests a high level of sophistication and a strategic understanding of enterprise infrastructure.
The attack chain for STAC4713 begins with initial access gained through exploiting various vulnerabilities. Early observations indicated the exploitation of exposed SonicWall VPNs, a common entry point for many threat actors due to often unpatched systems or weak credentials. More recent attacks have diversified, with Sophos noting the exploitation of the SolarWinds Web Help Desk vulnerability CVE-2025-26399. This particular vulnerability, if unpatched, could allow remote code execution, granting attackers a critical foothold. The group has also demonstrated an adaptability in their initial compromise strategies. In February, GOLD ENCOUNTER was observed leveraging an exposed Cisco SSL VPN, another critical network perimeter device. Further illustrating their social engineering prowess, in March, the group impersonated IT staff, tricking employees over Microsoft Teams into downloading and installing QuickAssist, a legitimate remote support tool that attackers then abuse for access.
Once initial access is secured, the threat actors proceed with establishing a robust and stealthy presence. A crucial step involves creating a scheduled task named ‘TPMProfiler.’ This task is designed to launch a hidden QEMU VM with SYSTEM privileges, ensuring deep system access and persistence. The virtual disk files required for the VM are cleverly disguised as legitimate database and DLL files, further aiding in evasion. To maintain covert access, the attackers configure port forwarding, establishing a reverse SSH tunnel back to their command-and-control (C2) infrastructure. This reverse tunnel is particularly insidious as it initiates outbound connections from the compromised host, which can often bypass ingress firewall rules.
The hidden VM runs Alpine Linux version 3.22.0, a lightweight and security-focused distribution, making it ideal for a stealthy operational environment. Within this VM, the attackers deploy a suite of tools tailored for various stages of their attack. These include AdaptixC2, a command-and-control framework; Chisel, a fast TCP/UDP tunnel over HTTP; BusyBox, a collection of Unix utilities in a single executable; and Rclone, a versatile command-line program for managing files on cloud storage. In more recent incidents, the threat actors have also utilized the legitimate ADNotificationManager.exe binary to sideload a Havoc C2 payload (vcruntime140_1.dll), allowing them to maintain persistent and sophisticated control over the compromised system. Rclone is then leveraged for data exfiltration, moving sensitive information to remote SFTP locations.
Post-infection, the actors engage in extensive reconnaissance and data harvesting. They exploit Volume Shadow Copy Service (VSS) by using vssuirun.exe to create shadow copies, which can then be used to access system files that might otherwise be locked. Following this, they utilize the print command over SMB to copy critical system hives such as NTDS.dit, SAM, and SYSTEM to temporary directories. These files contain hashed credentials for domain users, local users, and system information, which are invaluable for lateral movement and privilege escalation within the network.

Payouts King and its Ties to BlackBasta Affiliates
A Zscaler report further illuminates the Payouts King operation, suggesting a strong likelihood of its ties to former BlackBasta affiliates. This assessment is based on the striking similarities in initial access methods, which include spam bombing, Microsoft Teams phishing, and the abuse of Quick Assist – tactics previously and extensively employed by the notorious BlackBasta ransomware group. This connection implies either a direct evolution of personnel from BlackBasta to Payouts King or a sharing of Tactics, Techniques, and Procedures (TTPs) among experienced cybercriminals. Such affiliations highlight the dynamic and often interconnected nature of the ransomware ecosystem, where experienced actors migrate, share knowledge, or rebrand.
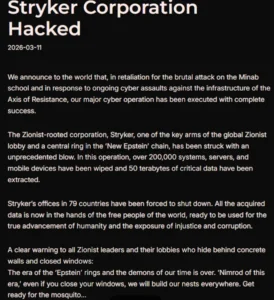
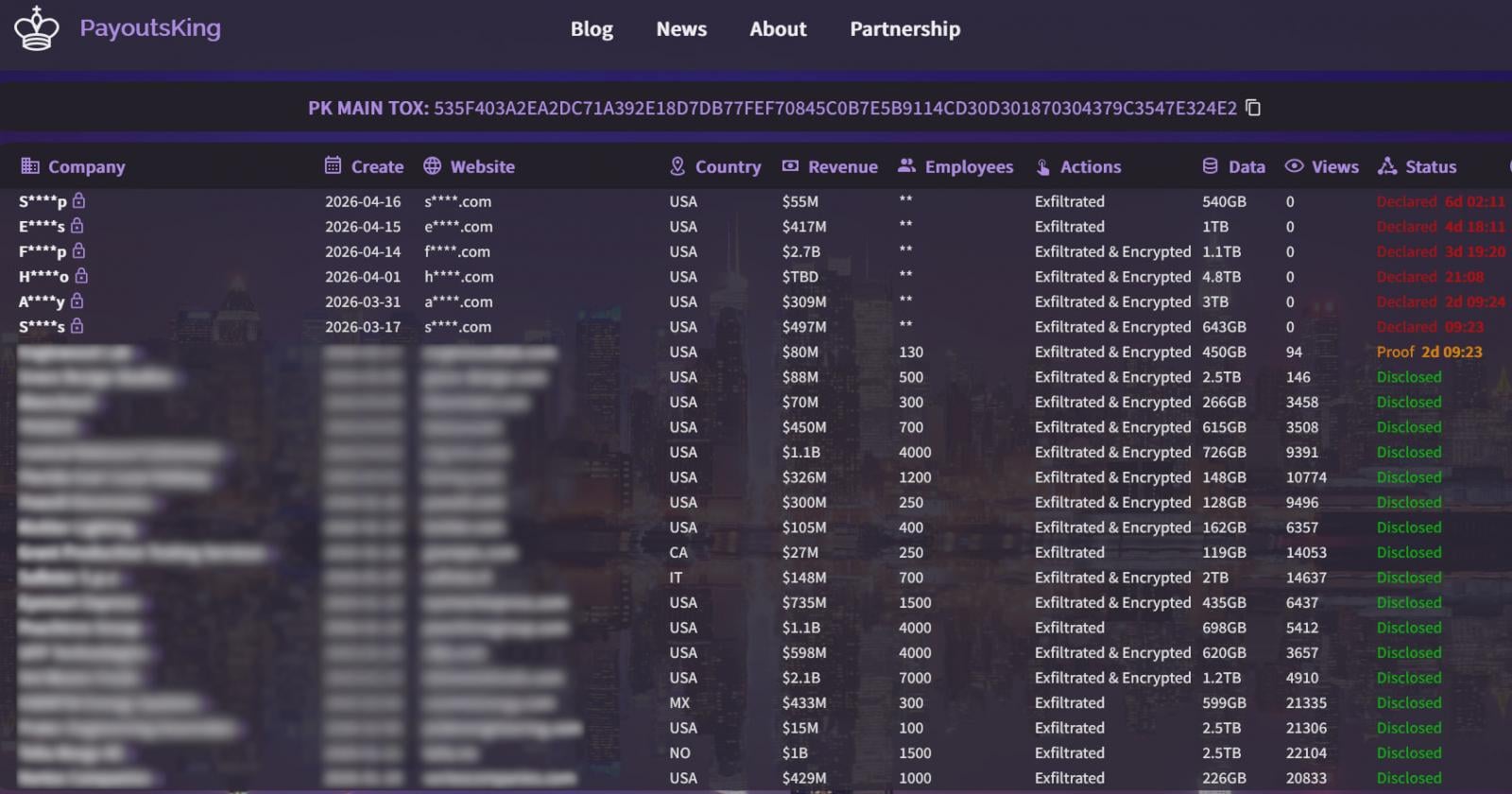
The Payouts King ransomware strain itself is characterized by heavy obfuscation and anti-analysis mechanisms, designed to thwart reverse engineering and detection efforts. It establishes persistence through scheduled tasks, mirroring the QEMU VM launch, and actively terminates security tools using low-level system calls to neutralize defensive measures. The encryption scheme employed is robust, combining AES-256 (CTR mode) for file encryption with RSA-4096 for key exchange. For larger files, the ransomware utilizes intermittent encryption, a technique that encrypts only portions of a file to speed up the process and make recovery without the decryption key virtually impossible, while still rendering the file unusable. Upon successful encryption, victims are directed to leak sites on the dark web via dropped ransom notes, where their stolen data may be published if the ransom is not paid, adding an extra layer of extortion. The extortion portal itself, as observed by BleepingComputer, presents a clear and unambiguous demand, typical of modern ransomware operations.
The STAC3725 Campaign: Exploiting CitrixBleed 2
The second campaign, STAC3725, demonstrates a different initial access vector but a similar reliance on QEMU for stealth. Active since February, this campaign exploits the CitrixBleed 2 vulnerability (CVE-2025-5777) to gain initial access to target environments. This critical vulnerability in NetScaler ADC and Gateway instances, if left unpatched, allows for session hijacking and potential remote code execution, granting attackers a direct gateway into internal networks.
Upon compromising NetScaler devices, the attackers deploy a ZIP archive containing a malicious executable. This executable is designed to install a service named ‘AppMgmt,’ create a new local administrator user called CtxAppVCOMService for additional persistence, and then install a ScreenConnect client. ScreenConnect, a legitimate remote access tool, is subsequently abused to connect to a remote relay server, establishing a persistent session with system privileges. This provides the attackers with a stable and often legitimate-looking channel for remote control.

Following the establishment of the ScreenConnect session, the threat actors drop and extract a QEMU package. This package is then used to run a hidden Alpine Linux VM, similar to the STAC4713 campaign, but utilizing a custom .qcow2 disk image. A key difference in STAC3725 is the attackers’ approach to tooling: instead of deploying a pre-built toolkit, they manually install and compile their chosen tools directly inside the VM. This meticulous approach can further complicate forensic analysis and detection, as it avoids reliance on easily identifiable, pre-packaged malware. The arsenal includes powerful tools such as Impacket, a collection of Python classes for working with network protocols; KrbRelayx and Coercer for Kerberos relay attacks and coercion; BloodHound.py for Active Directory reconnaissance; NetExec for network execution and enumeration; Kerbrute for Kerberos username enumeration; and Metasploit, a comprehensive penetration testing framework.
Observed activities within the STAC3725 campaign include extensive credential harvesting, leveraging the collected tools to extract authentication data. Kerberos username enumeration and Active Directory reconnaissance are conducted to map the network, identify high-value targets, and plan lateral movement. Finally, data is staged for exfiltration via FTP servers, indicating a clear intent for data theft and subsequent extortion.
Chronology of Key Events
- November 2025: Sophos first observes the STAC4713 campaign, later linked to Payouts King ransomware. Initial access vectors include exposed SonicWall VPNs.
- February (current year): Sophos spots the STAC3725 campaign, exploiting CitrixBleed 2 (CVE-2025-5777).
- February (current year): GOLD ENCOUNTER (associated with Payouts King) uses an exposed Cisco SSL VPN for initial access in a new attack.
- March (current year): GOLD ENCOUNTER employs social engineering via Microsoft Teams and QuickAssist abuse for initial access.
- Ongoing: Payouts King ransomware utilizes QEMU VMs, reverse SSH backdoors, and a sophisticated toolkit for evasion, credential theft, and data exfiltration, with observed ties to former BlackBasta affiliates.
Implications and Recommendations for Organizations
The sophisticated use of QEMU by threat actors like Payouts King presents significant challenges for traditional cybersecurity defenses. The ability to run malicious operations within hidden, isolated virtual machines effectively blinds endpoint detection and response (EDR) solutions that primarily monitor the host operating system. This necessitates a shift in defensive strategies, focusing on deeper visibility and behavioral analytics.
Sophos strongly recommends that organizations adopt proactive measures to detect and mitigate these advanced threats. Key indicators of compromise (IoCs) to monitor include:
- Unauthorized QEMU installations: Scrutinize systems for any QEMU binaries or related files that are not explicitly authorized and documented by IT teams.
- Suspicious scheduled tasks: Investigate scheduled tasks running with SYSTEM privileges, particularly those with unusual names like ‘TPMProfiler’ or those executing unfamiliar processes.
- Unusual SSH port forwarding: Monitor network traffic for unexpected SSH port forwarding activities, especially those initiating from internal systems to external, unknown IP addresses.
- Outbound SSH tunnels on non-standard ports: Be vigilant for outbound SSH connections on ports other than the standard 22, as attackers often use custom ports to evade detection.
Beyond these specific IoCs, the broader implications highlight several critical areas for improvement:
- Patch Management: The exploitation of vulnerabilities like SolarWinds Web Help Desk (CVE-2025-26399) and CitrixBleed 2 (CVE-2025-5777) underscores the paramount importance of a rigorous and timely patch management program. Unpatched systems remain the most common and easily exploitable entry points for sophisticated attackers.
- Network Segmentation: Implementing robust network segmentation can limit the lateral movement of attackers even if an initial compromise occurs.
- Behavioral Analytics and Threat Hunting: Relying solely on signature-based detection is insufficient against such advanced evasion techniques. Organizations need to invest in behavioral analytics tools that can detect anomalous activities within VMs or unusual network flows, and develop proactive threat hunting capabilities to uncover hidden threats.
- Identity and Access Management: Strong authentication mechanisms, including multi-factor authentication (MFA) for all critical systems and VPNs, are crucial to prevent credential theft and unauthorized access. Regular auditing of user accounts and permissions can also help mitigate risks.
- Security Awareness Training: The success of social engineering tactics, such as Microsoft Teams phishing leading to QuickAssist abuse, emphasizes the need for continuous and effective security awareness training for all employees. Users must be educated on identifying phishing attempts and the risks associated with installing unauthorized software or granting remote access.
- Supply Chain Security: The reliance on third-party software and devices (SonicWall, SolarWinds, Citrix) highlights the broader supply chain risks. Organizations must assess the security posture of their vendors and ensure all third-party components are regularly updated and secured.
In conclusion, the Payouts King ransomware, with its association with GOLD ENCOUNTER and potential ties to former BlackBasta affiliates, represents a highly adaptable and dangerous threat. Its innovative use of QEMU virtual machines to create stealthy operational environments signifies a significant challenge to conventional cybersecurity defenses. As threat actors continue to evolve their tactics, organizations must adopt a multi-layered, proactive security strategy that combines robust technical controls with vigilant monitoring, timely patching, and comprehensive security awareness. The ongoing "arms race" between attackers and defenders necessitates continuous adaptation and investment in advanced detection and response capabilities to protect critical assets from these increasingly sophisticated threats.