Microsoft Defender Under Siege: Active Exploitation of Zero-Day Vulnerabilities Prompts Urgent Warnings

Cybersecurity firm Huntress has issued a critical alert, revealing that malicious actors are actively exploiting three recently disclosed security vulnerabilities in Microsoft Defender, the ubiquitous endpoint protection platform. These exploits grant threat actors elevated privileges on compromised systems and can disable vital security updates, posing a severe risk to organizations globally. The ongoing attacks underscore the relentless pace of the cyber threat landscape and reignite discussions around vulnerability disclosure practices.
The vulnerabilities, publicly released as zero-days by a researcher known as Chaotic Eclipse (also identified as Nightmare-Eclipse), are codenamed BlueHammer, RedSun, and UnDefend. This unusual public disclosure, circumventing traditional coordinated vulnerability disclosure (CVD) channels, reportedly stemmed from the researcher’s dissatisfaction with Microsoft’s handling of the disclosure process. While Microsoft has since addressed BlueHammer as part of its scheduled Patch Tuesday updates earlier this week, the other two critical flaws, RedSun and UnDefend, remain unpatched, leaving countless systems exposed to active exploitation.
The Unfolding Crisis: Exploitation in the Wild
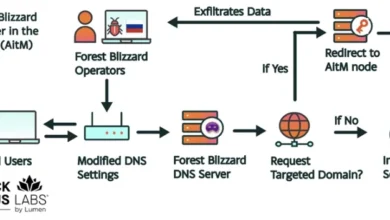
Huntress, a prominent provider of managed detection and response (MDR) services, first raised the alarm through a series of posts on X (formerly Twitter). Their intelligence indicated that all three vulnerabilities were being actively weaponized in the wild, with observed exploitation activities demonstrating sophisticated "hands-on-keyboard" threat actor behavior. This suggests not merely automated attacks but rather human-driven operations aiming for deeper compromise. The rapid deployment of these exploits by malicious actors underscores a highly adaptive and opportunistic threat landscape.
The initial exploitation of BlueHammer was detected as early as April 10, 2026, indicating that attackers had a week-long window of opportunity before Microsoft released a patch. The subsequent weaponization of RedSun and UnDefend proof-of-concept (PoC) exploits was observed on April 16, just as news of the BlueHammer fix began to circulate. This rapid adoption of newly disclosed flaws by threat actors highlights their agility and constant monitoring of the security research landscape, often leveraging public disclosures within hours or days.
According to Huntress’s detailed observations, the invocation of these exploits followed a common pattern of post-compromise enumeration commands. Specifically, threat actors were seen executing commands such as whoami /priv, cmdkey /list, and net group. These commands are standard reconnaissance tools used by attackers to understand their current privilege level, identify stored credentials, and map network groups, respectively. The presence of such commands is a strong indicator of active, human-controlled intrusion rather than automated malware. This "hands-on-keyboard" activity signifies a more targeted and persistent threat, where attackers are adapting their actions in real-time based on the compromised environment. Once these initial reconnaissance steps are completed, attackers typically leverage privilege escalation flaws like BlueHammer and RedSun to gain administrative access, enabling them to disable security software, install backdoors, exfiltrate data, or deploy devastating payloads like ransomware.
Unpacking the Vulnerabilities: BlueHammer, RedSun, and UnDefend
A deeper dive into the specifics of these vulnerabilities reveals their potential for severe impact on endpoint security and overall system integrity.
-
BlueHammer (CVE-2026-33825): This is a local privilege escalation (LPE) vulnerability affecting Microsoft Defender. An LPE flaw allows an attacker who has already gained a foothold on a system (even with low-level user privileges) to elevate their access to a higher privilege level, typically system or administrator. With administrative privileges, an attacker can bypass security controls, install or uninstall software, modify system configurations, and access sensitive data without restriction. This can lead to complete system takeover, lateral movement across the network, and the deployment of advanced persistent threats. Microsoft acknowledged BlueHammer and addressed it with CVE-2026-33825 as part of its April 2026 Patch Tuesday release. The patch, while welcome, came after observed active exploitation, emphasizing the critical importance of timely patching.
-
RedSun: Similar to BlueHammer, RedSun is also an LPE vulnerability impacting Microsoft Defender. Its function is to allow an attacker to gain elevated privileges on a compromised system. The existence of multiple LPE flaws in a core security product like Defender is particularly concerning, as it provides threat actors with alternative pathways to achieve their objectives even if one vulnerability is patched. This redundancy in attack vectors means that even if an organization patches one LPE, another unpatched flaw could still be exploited. As of the time of this report, RedSun remains unpatched, leaving systems vulnerable to this critical escalation technique.
-
UnDefend: This vulnerability presents a different, yet equally dangerous, threat. UnDefend can be used to trigger a denial-of-service (DoS) condition specifically targeting Microsoft Defender’s ability to receive definition updates. In the context of antivirus software, definition updates are paramount. They provide the latest signatures, behavioral rules, and heuristics necessary to detect and neutralize new and evolving malware threats. By blocking these updates, UnDefend effectively renders Microsoft Defender impotent against emerging threats, creating a critical window for subsequent attacks that the outdated definitions would fail to catch. This flaw also remains unpatched, creating a dangerous blind spot for affected organizations and severely degrading their defensive posture.
The combination of LPE flaws and a DoS vulnerability targeting updates represents a potent toolkit for attackers. An LPE allows them to gain control, and the DoS allows them to maintain that control by preventing the very software designed to stop them from updating its defenses. This dual capability makes these vulnerabilities particularly attractive to sophisticated threat actors aiming for persistent and covert access.
The Zero-Day Dilemma: Chaotic Eclipse’s Disclosure
The circumstances surrounding the disclosure of these vulnerabilities add another layer of complexity to this unfolding story. Chaotic Eclipse, also known as Nightmare-Eclipse, chose to release details and proof-of-concept code for all three vulnerabilities as "zero-days." A zero-day vulnerability is a flaw that is unknown to the vendor and for which no patch exists, making it particularly dangerous when publicly disclosed and exploited.
The decision by a security researcher to publicly release zero-days is often controversial and typically reserved for situations where the researcher believes the vendor has been unresponsive or negligent in addressing the reported issues through established coordinated vulnerability disclosure (CVD) channels. CVD is an industry-standard practice where researchers privately notify vendors of vulnerabilities, allowing them time to develop and release patches before the details are made public. This process aims to protect users by minimizing the window during which vulnerabilities can be exploited without a fix. It is a delicate balance between public interest and potential harm.

While the specific details of Chaotic Eclipse’s interactions with Microsoft prior to the public disclosure are not fully public (beyond the inference of dissatisfaction), the researcher’s GitHub repositories for BlueHammer, RedSun, and UnDefend explicitly state their motivation, hinting at a breakdown in the typical disclosure process. This act reignites the perennial debate within the cybersecurity community: the tension between a researcher’s ethical obligation to protect users by ensuring vulnerabilities are patched quickly, and the potential harm caused by publicizing flaws that could be immediately weaponized by malicious actors. In this instance, the rapid exploitation observed by Huntress underscores the immediate risks associated with full public disclosure without a corresponding patch. Such disclosures, while sometimes seen as a way to force a vendor’s hand, can inadvertently put end-users at greater risk by providing adversaries with ready-made attack tools.
Microsoft’s Patch Tuesday Response and Ongoing Challenges
In response to the active exploitation of BlueHammer, Microsoft moved to address the vulnerability as part of its regularly scheduled Patch Tuesday updates. These monthly updates are a critical component of Microsoft’s security posture, bundling fixes for a wide array of security flaws across its product portfolio. The vulnerability was assigned CVE-2026-33825, allowing organizations to track and prioritize its remediation.
When contacted for comment, a Microsoft spokesperson confirmed that the BlueHammer exploit had indeed been addressed via CVE-2026-33825. The spokesperson reiterated the company’s commitment: "Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible." They also emphasized their support for "coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community." This statement reflects Microsoft’s official stance on responsible disclosure, highlighting the challenges of balancing rapid response with thoroughness.
However, the fact that RedSun and UnDefend remain unpatched is a significant concern. Microsoft’s patching process involves rigorous testing to ensure fixes do not introduce new instabilities or regressions across its vast and diverse user base. While this meticulous approach is understandable for a product used by billions worldwide, the existence of actively exploited zero-days places immense pressure on the vendor to accelerate its response. The company faces the monumental task of securing a vast ecosystem of software and hardware, continually balancing the speed of patch deployment with the stability and integrity of its products, a challenge made more complex by the sheer volume of vulnerabilities discovered monthly.
A Chronology of Compromise
To provide a clear picture of the rapid developments and the narrow window between disclosure and exploitation, here is a chronological overview of the key events:
- Prior to April 10, 2026: Chaotic Eclipse (Nightmare-Eclipse) discovers BlueHammer, RedSun, and UnDefend vulnerabilities in Microsoft Defender. It is inferred that attempts at coordinated disclosure with Microsoft are made, but reportedly lead to dissatisfaction on the researcher’s part regarding Microsoft’s response or timeline.
- April 10, 2026: Threat actors are observed by Huntress actively weaponizing and exploiting the BlueHammer vulnerability (CVE-2026-33825) in compromised systems. This marks the earliest known in-the-wild exploitation of one of the flaws.
- Early April 2026 (Leading up to Patch Tuesday): Chaotic Eclipse publicly discloses the details and proof-of-concept code for BlueHammer, RedSun, and UnDefend on platforms like GitHub, effectively making them zero-days. This public release makes the vulnerabilities immediately accessible to a wide range of actors, including those with malicious intent.
- "Earlier this week" (approx. April 15, 2026 – Patch Tuesday): Microsoft releases its monthly security updates. A fix for BlueHammer, identified as CVE-2026-33825, is included in this release.
- April 16, 2026: Huntress observes threat actors utilizing proof-of-concept (PoC) exploits for RedSun and UnDefend in compromised environments. This indicates a rapid uptake by malicious actors following the public disclosure, demonstrating their efficiency in converting PoC code into functional attacks.
- April 17, 2026: Huntress issues its public warning, detailing the active exploitation of all three flaws and emphasizing the unpatched status of RedSun and UnDefend, prompting widespread concern within the cybersecurity community. This news article is published on this date, disseminating the urgent warning.
This timeline vividly illustrates the compressed nature of modern cyber threats, where the window between vulnerability disclosure and active exploitation can be mere days or even hours, demanding unprecedented agility from both defenders and vendors.
Broader Implications for Endpoint Security
The active exploitation of Microsoft Defender vulnerabilities carries significant implications for organizations and the broader cybersecurity landscape. Microsoft Defender is often the first, and sometimes only, line of defense for millions of Windows users and enterprises globally. Its deep integration into the operating system makes it a powerful security tool, but also a high-value target for adversaries, as compromising it can yield widespread access.
- Erosion of Trust and Reliance: Repeated vulnerabilities in core security products can erode user and organizational trust in their default defenses. While no software is perfectly secure, LPE flaws in antivirus software are particularly concerning as they undermine the very purpose of endpoint protection, which is to prevent unauthorized access and malicious activity. Organizations that rely heavily on Defender might be forced to re-evaluate their security stack.
- Enhanced Attacker Capabilities: LPE flaws are often the critical missing link for attackers to achieve full system control after an initial breach. Coupled with a DoS flaw that disables updates, these vulnerabilities provide a potent combination that can facilitate persistent access, enable lateral movement within networks, and ultimately lead to the deployment of devastating payloads like ransomware, data wipers, or sophisticated espionage tools. The ability to blind the antivirus while escalating privileges is a powerful advantage for an attacker.
- Reinforcement of Defense-in-Depth: This incident strongly reinforces the perennial need for a multi-layered, defense-in-depth security strategy. Relying solely on a single endpoint protection solution, even one as robust as Microsoft Defender, is insufficient against determined adversaries. Organizations must implement additional controls, including network segmentation, strong access controls (e.g., least privilege), regular security audits, and robust patching programs across all software and systems.
- The Critical Role of MDR and Threat Hunting: Huntress’s ability to detect these "hands-on-keyboard" activities highlights the critical role of advanced threat hunting and managed detection and response (MDR) services. These services go beyond automated alerts to actively look for anomalous behavior that indicates sophisticated, human-driven attacks, providing a vital early warning system that can identify threats that bypass conventional security tools.
Expert Commentary and Industry Reactions
Security experts across the industry have echoed Huntress’s warning, urging organizations to prioritize patching and continuous monitoring. The consensus is that the speed of modern cyber threats demands a proactive and multi-faceted defense.
A representative from Huntress, speaking hypothetically given the public nature of their alerts, might emphasize: "Our observations confirm that threat actors are incredibly agile, rapidly incorporating newly disclosed vulnerabilities into their attack chains. The moment a zero-day is public, it’s a race against time for defenders. Organizations must operate under the assumption of potential compromise and implement proactive threat hunting to catch these sophisticated attacks before they escalate and cause irreversible damage."
Industry analysts frequently point out the inherent difficulties faced by large vendors like Microsoft in securing their vast ecosystems. "Securing a platform as vast and complex as Windows, with its myriad components and integrations, is an unenviable task," stated a leading cybersecurity analyst. "While the goal is always zero vulnerabilities, the reality is that flaws will emerge. The critical factor is the speed and effectiveness of response, and the transparent communication with the security community and customers. This incident highlights the immense pressure on vendors to respond quickly to zero-days."
The incident also serves as a stark reminder for the security research community. While the motivations behind a zero-day disclosure can be rooted in frustration or a desire to force a vendor’s hand, the immediate consequence can be increased risk for end-users who suddenly face an unpatched, actively exploited vulnerability. This incident will undoubtedly fuel further debate on the optimal balance between public interest and responsible disclosure, particularly when public disclosures are rapidly weaponized.
Mitigation and Best Practices
In light of the active exploitation and the unpatched status of RedSun and UnDefend, organizations are strongly advised to take immediate action to protect their systems:
- Prioritize Patching: Ensure all Windows systems are updated with the latest Microsoft Patch Tuesday releases, specifically verifying the application of CVE-2026-33825 for BlueHammer. Implement robust patch management policies to ensure timely deployment across all endpoints, ideally within days of release.
- Enhance Monitoring and Detection: Increase vigilance on endpoint activity. Monitor for the specific commands identified by Huntress (
whoami /priv,cmdkey /list,net group) and other indicators of compromise (IoCs) that may emerge from security advisories. Leverage endpoint detection and response (EDR) solutions and MDR services to detect and respond to "hands-on-keyboard" activities and anomalous behavior indicative of privilege escalation. - Implement Defense-in-Depth: Do not rely solely on Microsoft Defender. Deploy additional security layers, including firewalls, intrusion prevention systems, application whitelisting, and strict least privilege access policies for users and applications. Consider complementary endpoint protection platforms if feasible.
- Network Segmentation: Segment networks to limit lateral movement should a system be compromised. This can contain the impact of an LPE exploit and prevent an attacker from escalating a local breach into a full-scale network compromise.
- Regular Backups and Incident Response Plan: Maintain offline, immutable backups of critical data and systems. Ensure a well-tested incident response plan is in place to quickly mitigate and recover from successful attacks, minimizing downtime and data loss.
- Stay Informed: Continuously monitor advisories from cybersecurity vendors like Huntress and official sources like Microsoft’