Financially Motivated Cybercrime Group TeamPCP Deploys Data Wiper Targeting Iran Amid Escalating Geopolitical Tensions
A financially motivated cybercrime syndicate, identified as TeamPCP, has escalated its operations by deploying a destructive data-wiping worm specifically engineered to target systems within Iran, marking a concerning shift from pure financial extortion to actions with potential geopolitical ramifications. This advanced worm, capable of spreading through inadequately secured cloud services, is designed to erase data on infected systems that either utilize Iran’s time zone settings or have Farsi designated as the default language. The emergence of this targeted campaign over the past weekend underscores the increasingly blurred lines between conventional cybercrime and actions typically associated with nation-state actors, injecting a new, unpredictable element into the already volatile landscape of the Iran war.
The Rise of TeamPCP: A Cloud-Native Threat
Experts tracking the group, including security researchers from Flare and Aikido, pinpoint the origins of TeamPCP’s activities to December 2025. Initially, the group established itself as a formidable threat by systematically compromising corporate cloud environments. Their methodology leverages a sophisticated, self-propagating worm that meticulously scans for and exploits exposed Docker APIs, Kubernetes clusters, Redis servers, and the notorious React2Shell vulnerability. Docker, a platform for developing, shipping, and running applications, often exposes APIs that, if left unsecured, can grant attackers broad control over containerized applications. Similarly, Kubernetes, an open-source system for automating deployment, scaling, and management of containerized applications, presents a rich target for lateral movement and data exfiltration if its clusters are misconfigured. Redis, an open-source, in-memory data store used as a database, cache, and message broker, can also be exploited if exposed without proper authentication, allowing unauthorized access to sensitive data. The React2Shell vulnerability, a remote code execution flaw, further augments their arsenal by providing initial access points into vulnerable systems.
Once initial access is gained, TeamPCP’s strategy involves moving laterally through victim networks, meticulously siphoning authentication credentials, and subsequently extorting victims, primarily communicating their demands via the encrypted messaging platform Telegram. This financially driven approach has allowed them to amass significant resources and a reputation for effective, large-scale compromise of enterprise cloud infrastructure.
In January, the security firm Flare published a comprehensive profile of TeamPCP, shedding light on their distinct operational paradigm. Flare highlighted that TeamPCP’s strength does not lie in discovering novel zero-day exploits or developing entirely original malware strains. Instead, their effectiveness stems from the "large-scale automation and integration of well-known attack techniques." Assaf Morag of Flare articulated this, stating, "The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem." This industrialized approach allows them to achieve a wide blast radius, targeting infrastructure rather than individual endpoints, with a heavy preference for cloud services. Their analysis indicated that Azure (61%) and AWS (36%) collectively accounted for 97% of their compromised servers, underscoring their specialization in major cloud platforms. This focus on cloud control planes, rather than traditional end-user devices, represents a significant evolution in cybercrime, as compromising these central management points grants them extensive control over an organization’s digital assets.
Escalating Tactics: Supply Chain Attacks and the CanisterWorm
TeamPCP’s operational sophistication continued to evolve, demonstrating a clear pivot towards supply chain attacks to maximize their impact and reach. On March 19, the group executed a critical supply chain attack against Trivy, a popular open-source vulnerability scanner developed by Aqua Security. This attack involved injecting credential-stealing malware into official releases of Trivy distributed via GitHub Actions. GitHub Actions, a continuous integration and continuous delivery (CI/CD) platform, allows developers to automate tasks within their software development workflows. By compromising these actions, TeamPCP effectively poisoned the well, ensuring that anyone using the affected Trivy releases would inadvertently download and execute their malicious payload.
Aqua Security swiftly responded by removing the harmful files, but not before the attackers were able to publish malicious versions. Security firm Wiz later noted that these compromised versions were capable of exfiltrating a range of highly sensitive data, including SSH keys, cloud credentials, Kubernetes tokens, and cryptocurrency wallets from unsuspecting users. The incident highlighted the profound vulnerability of the software supply chain, where a single compromise can cascade through numerous organizations relying on the affected tools.
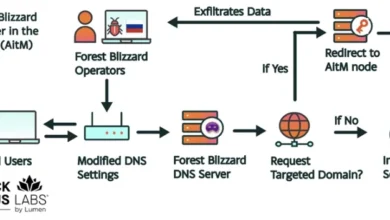
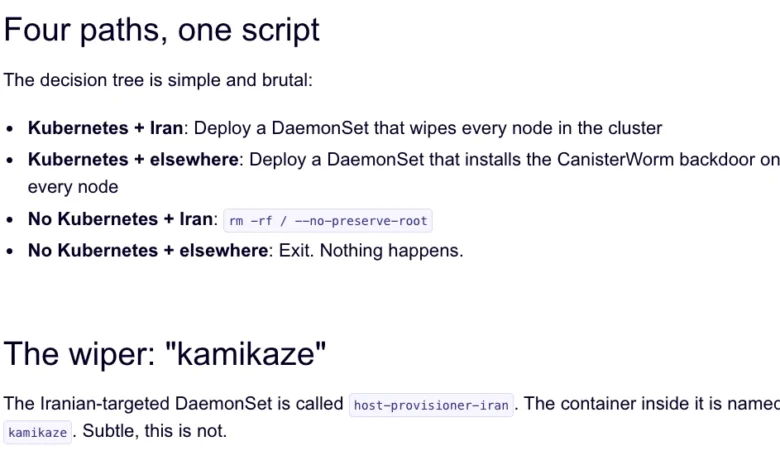
The technical infrastructure utilized in the Trivy attack, which Aikido security researchers refer to as "CanisterWorm," played a pivotal role in the subsequent Iran-targeting wiper campaign. Charlie Eriksen, a security researcher at Aikido, revealed that this infrastructure was leveraged to deploy a new, highly destructive payload over the past weekend. This payload’s unique characteristic is its conditional execution: it initiates a data-wiping attack only if the victim’s system locale and timezone settings correspond to Iran.
Eriksen elaborated on the wiper’s destructive capabilities in a blog post published on Sunday, explaining that if the malicious component detects a victim in Iran with access to a Kubernetes cluster, it proceeds to destroy data on every node within that cluster. "If it doesn’t [detect a Kubernetes cluster], it will just wipe the local machine," Eriksen clarified in a statement to KrebsOnSecurity, indicating a tiered approach to destruction based on the victim’s environment. This targeted destruction, specifically engineered for Iranian systems, marks a significant departure from TeamPCP’s previously observed financially motivated extortion schemes, raising questions about their ultimate objectives.
The "CanisterWorm" moniker stems from TeamPCP’s innovative use of Internet Computer Protocol (ICP) canisters to orchestrate their campaigns. ICP canisters are essentially tamperproof, blockchain-based "smart contracts" that encapsulate both code and data. Their distributed architecture grants them exceptional resilience against takedown attempts, as they can serve web content directly and remain accessible as long as their operators continue to pay virtual currency fees to keep them online. This decentralized, blockchain-backed infrastructure provides TeamPCP with a robust and difficult-to-disrupt command and control mechanism, allowing them to rapidly deploy and modify payloads, as evidenced by their "up and down" changes to the malicious code.

Braggadocio and Blurring Lines: The Motivation Behind the Iran Wiper
TeamPCP has not shied away from publicizing their exploits. Eriksen noted that the group has been openly bragging about their successes in a private Telegram group, claiming to have stolen vast quantities of sensitive data from major corporations, including a prominent multinational pharmaceutical firm. Their actions, such as spamming numerous compromised GitHub accounts with "junk messages" after the second Aqua Security compromise, suggest a deliberate attempt to flaunt their access and capabilities. "It was almost like they were just showing off how much access they had," Eriksen observed. "Clearly, they have an entire stash of these credentials, and what we’ve seen so far is probably a small sample of what they have."
This public display of power extends beyond mere boasting. Catalin Cimpanu, a reporter for Risky Business, highlighted in his newsletter "GitHub is Starting to Have a Real Malware Problem" that such actions, including pushing meaningless commits or employing services that sell GitHub stars and "likes," are often tactics used by attackers. The goal is to keep malicious packages prominently displayed at the top of GitHub search results, increasing their visibility and potential for wider distribution.
The true motivation behind the Iran-targeting wiper remains a subject of ongoing analysis. While TeamPCP is primarily known for financial extortion, this specific targeting introduces a geopolitical dimension. Eriksen speculated on the group’s motives, suggesting, "It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention." He further characterized their behavior as "really playing this Chaotic Evil role here," implying a desire for disruption and notoriety beyond pure profit. This chaotic element makes them particularly unpredictable and dangerous, as their actions may not align with conventional financial incentives. The fact that the malicious canister occasionally redirected visitors to a Rick Roll video on YouTube when not serving malware downloads further underscores this seemingly erratic, yet calculated, behavior.
The Pervasive Threat of Supply Chain Attacks and Cloud Vulnerabilities
TeamPCP’s activities are not isolated incidents but rather symptomatic of a broader, alarming trend in the cybersecurity landscape: the significant increase in supply chain attacks. Cimpanu’s reporting indicates a surge in such incidents since 2024, as threat actors increasingly recognize the efficiency and extensive reach offered by compromising widely used software components or development tools. The attack on Trivy was, in fact, the second major supply chain incident involving the scanner in as many months. In late February, Trivy was also impacted by "HackerBot-Claw," an automated threat that exploited misconfigured workflows in GitHub Actions to steal authentication tokens. This recurrence highlights the persistent vulnerabilities within the software development ecosystem and the urgent need for enhanced security measures.
The challenge for platforms like GitHub is immense. As Cimpanu noted, "on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix." The very nature of open-source collaboration, while fostering innovation, also creates a complex attack surface that malicious actors are increasingly exploiting. Organizations worldwide rely heavily on open-source components and CI/CD pipelines, making them attractive targets for adversaries seeking to compromise numerous downstream victims simultaneously.
Official Responses and Broader Implications
Security firms like Aqua Security, Wiz, Flare, and Aikido have played a crucial role in rapidly detecting, analyzing, and reporting on TeamPCP’s evolving tactics. Their swift actions, such as Aqua Security’s removal of malicious files from Trivy’s GitHub releases and the issuance of advisories, are critical for mitigating the immediate impact of these attacks. However, the recurring nature of these incidents, especially within popular development tools, underscores the need for proactive and systemic changes across the industry.
The update on March 23rd, reporting that TeamPCP also pushed credential-stealing malware to the KICS vulnerability scanner from Checkmarx via a compromised GitHub Action, further solidifies the pattern of targeting development security tools. The KICS GitHub Action was compromised for several hours on that day, allowing TeamPCP to potentially harvest more sensitive credentials. This continuous targeting of security tools is particularly insidious, as it undermines the very mechanisms designed to protect software integrity.
The implications of TeamPCP’s activities are far-reaching:
- Escalation of Cybercrime: The shift from pure financial motivation to geopolitically tinged data wiping by a criminal group represents a dangerous evolution. It suggests that financially driven actors might be willing to engage in more destructive, politically motivated operations, either for hire or for notoriety, blurring the lines between cybercrime and cyber warfare.
- Increased Risk for Cloud-Native Environments: TeamPCP’s specialized focus on cloud infrastructure and vulnerabilities in Docker, Kubernetes, and Redis means that organizations heavily reliant on these technologies face an elevated and persistent threat. Robust cloud security postures, including rigorous access control, continuous monitoring, and secure configuration management, are more critical than ever.
- Software Supply Chain Integrity Under Siege: The repeated compromises of popular open-source tools like Trivy and KICS highlight a systemic weakness in the software supply chain. Developers and organizations must implement stringent security practices for their CI/CD pipelines, including integrity checks, least privilege access for GitHub Actions, and thorough vetting of all third-party components.
- Challenges for Platform Security: GitHub, as a central repository for open-source development, faces an immense challenge in securing its platform against sophisticated supply chain attacks. This necessitates significant investment in advanced threat detection, proactive vulnerability scanning of repositories, and potentially more stringent verification processes for popular actions and packages.
- The Rise of Resilient C2 Infrastructure: The use of ICP canisters demonstrates a growing trend among advanced threat actors to leverage decentralized, blockchain-based infrastructure for command and control. Such infrastructure is inherently resilient to traditional takedown attempts, making it harder for law enforcement and security researchers to disrupt malicious operations.
- Unpredictability of "Chaotic Evil" Actors: Groups like TeamPCP, driven by a mix of financial gain and a desire for disruption or attention, introduce a high degree of unpredictability into the cyber threat landscape. Their willingness to engage in destructive acts, potentially without clear political alignment, poses a unique challenge for threat intelligence and national security agencies.
While Eriksen noted that it’s difficult to ascertain if TeamPCP’s wiper successfully destroyed data from victim systems and that the malicious payload was only active for a short period, the intent and capability demonstrated are deeply concerning. The rapid deployment, modification, and withdrawal of malicious code suggest a highly agile and adaptive adversary. As the digital battleground continues to evolve, the actions of groups like TeamPCP serve as a stark reminder of the persistent and dynamic threats faced by individuals, corporations, and even nations in the interconnected world. The collective vigilance of security researchers, platform providers, and users will be paramount in mitigating these burgeoning risks.